Microsoft has delivered an unexpected emergency out-of-band security update to address a critical zero-day vulnerability — identified as “PrintNightmare” — that affects the Windows Print Spooler service and can permit distant threat actors to run arbitrary code and get around susceptible devices.
Tracked as CVE-2021-34527 (CVSS rating: 8.8), the remote code execution flaw impacts all supported editions of Windows. Very last week, the corporation warned it had detected active exploitation attempts focusing on the vulnerability.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The Microsoft Windows Print Spooler assistance fails to limit entry to operation that lets end users to increase printers and related motorists, which can enable a remote authenticated attacker to execute arbitrary code with Program privileges on a susceptible program,” the CERT Coordination Middle reported of the issue.
It is truly worth noting that PrintNightmare consists of both equally distant code execution and a local privilege escalation vector that can be abused in attacks to run commands with Method privileges on qualified Windows devices.
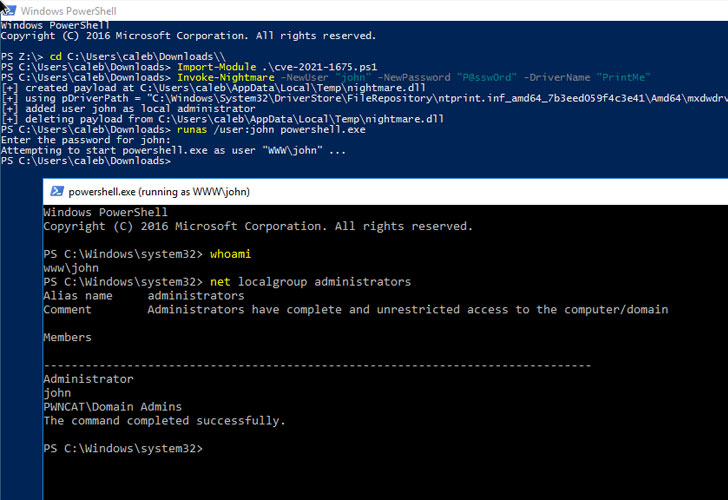
“The Microsoft update for CVE-2021-34527 only seems to address the Distant Code Execution (RCE by using SMB and RPC) variants of the PrintNightmare, and not the Nearby Privilege Escalation (LPE) variant,” CERT/CC vulnerability analyst Will Dormann stated.
This properly signifies that the incomplete resolve could nevertheless be made use of by a neighborhood adversary to obtain Procedure privileges. As workarounds, Microsoft recommends halting and disabling the Print Spooler company or turning off inbound distant printing through Team Coverage to block distant attacks.

Supplied the criticality of the flaw, the Windows maker has issued patches for:
- Windows Server 2019
- Windows Server 2012 R2
- Windows Server 2008
- Windows 8.1
- Windows RT 8.1
- and a wide variety of supported versions of Windows 10.
Microsoft has even taken the uncommon step of issuing the repair for Windows 7, which formally arrived at the end of assist as of January 2020.
The update, nevertheless, does not consist of Windows 10 version 1607, Windows Server 2012, or Windows Server 2016, for which the Redmond-centered organization said patches will be introduced in the forthcoming days.
Uncovered this report fascinating? Comply with THN on Facebook, Twitter and LinkedIn to browse extra exclusive content material we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com

 As Kaseya works to bring SaaS servers online, experts laud precautionary measures as ‘opposite of complacency’
As Kaseya works to bring SaaS servers online, experts laud precautionary measures as ‘opposite of complacency’