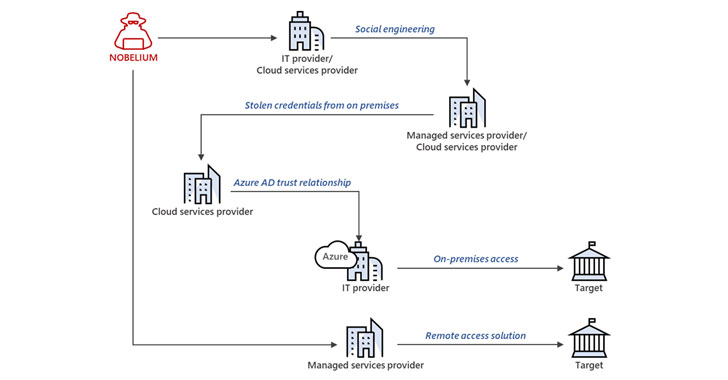
Nobelium, the danger actor guiding the SolarWinds compromise in December 2020, has been behind a new wave of attacks that compromised 14 downstream buyers of numerous cloud support companies (CSP), managed provider companies (MSP), and other IT products and services companies, illustrating the adversary’s continuing fascination in concentrating on the provide chain through the “compromise-one-to-compromise-numerous” method.
Microsoft, which disclosed facts of the marketing campaign on Monday, said it notified additional than 140 resellers and technology service suppliers due to the fact Might. Involving July 1 and October 19, 2021, Nobelium is reported to have singled out 609 buyers, who were being collectively attacked a grand full of 22,868 instances.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“This latest action is yet another indicator that Russia is hoping to attain extended-phrase, systematic access to a wide variety of points in the technology provide chain and build a system for surveilling – now or in the foreseeable future – targets of desire to the Russian federal government,” claimed Tom Burt, Microsoft’s company vice president of shopper security and believe in.
The freshly disclosed attacks do not exploit any particular security weaknesses in application but instead leverage a diverse array of strategies these kinds of as password spraying, token theft, API abuse, and spear-phishing to siphon qualifications involved with privileged accounts of services suppliers, enabling the attackers to transfer laterally in cloud environments and mount more intrusions.
The intention, according to Microsoft, seems that “Nobelium eventually hopes to piggyback on any direct obtain that resellers may have to their customers’ IT devices and a lot more quickly impersonate an organization’s dependable technology spouse to attain entry to their downstream shoppers.”
If something, the attacks are still a different manifestation of Nobelium’s oft-repeated strategies, which has been uncovered abusing believe in interactions enjoyed by service suppliers to burrow into numerous victims of desire for intelligence attain. As mitigations, the firm is recommending businesses to empower multi-factor authentication (MFA) and audit delegated administrative privileges (DAP) to stop any probable misuse of elevated permissions.
The advancement also comes less than a thirty day period following the tech huge exposed a new passive and very specific backdoor dubbed “FoggyWeb” deployed by the hacking group to supply further payloads and steal sensitive facts from Energetic Listing Federation Products and services (Advertisement FS) servers.
Identified this report exciting? Comply with THN on Facebook, Twitter and LinkedIn to read through extra special content we write-up.
Some areas of this write-up are sourced from:
thehackernews.com

 Tesco services knocked offline after suspected cyber attack
Tesco services knocked offline after suspected cyber attack