Just one of the good sources readily available to businesses today is the huge ecosystem of price-added products and services and methods. Specially in technology remedies, there is no close to the expert services of which companies can avail themselves.
In addition, if a business enterprise requirements a specific option or service they never tackle in-house, there is most probable a third-party vendor that can get care of that for them.
It is very effective for enterprises currently to entry these huge swimming pools of third-party resources. Nevertheless, there can be security issues for companies working with third-party vendors and their services inspite of the added benefits. Let us appear at navigating vendor risk management as IT professionals and see how firms can accomplish this in a hugely intricate cybersecurity environment.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
How can 3rd-party vendors introduce cybersecurity challenges?
As stated, third-party distributors can be really helpful to businesses performing small business nowadays. They enable providers to stay away from developing out technology and other alternatives in-house and eat these as a services. These expert services are critical for modest businesses that could not have the methods or complex expertise to make out the infrastructure and application answers essential.
On the other hand, when organizations interact with technology methods that combine with their company-critical and delicate methods, they must take into consideration the prospective cybersecurity pitfalls concerned.
As the proverbial “weakest connection in the chain,” if the cybersecurity methods and posture of a third-party seller are inadequate, if their methods integrate with your programs, the resulting cybersecurity dangers now have an impact on your techniques. What are the authentic-entire world outcomes of a vendor-similar information breach?
Acquire be aware of the subsequent. In 2013, Focus on Corporation, acknowledged as one of the large shops in the U.S., fell sufferer to a details breach because of to the hack of a 3rd-party company possessing network qualifications for Target’s network.
Attackers first hacked the network of Fazio Mechanical Products and services, a supplier of refrigeration and HVAC services for Goal. As a outcome, attackers compromised 40 million accounts, and Target agreed to pay out $10 million in damages to shoppers who had information stolen.
What is Vendor Risk Management (VRM)?
To meet the cybersecurity problems in functioning with 3rd-party sellers, businesses need to target on seller risk management (VRM). What is VRM? Seller risk administration (VRM) lets corporations to aim on identifying and mitigating risks involved with 3rd-party distributors.
With VRM, organizations have visibility into the distributors they have founded interactions with and the security controls they have applied to make sure their devices and processes are protected and safe.
With the substantial threats and compliance rules that have evolved for organizations today, VRM is a discipline that must be given due notice and have the obtain-in from IT pros and board customers alike.
Navigating Vendor Risk Management as IT Industry experts
Mainly, the accountability to find, realize, and mitigate vendor risk administration similar to overall cybersecurity falls on the IT department and SecOps. In addition, IT is frequently responsible for forming the VRM technique for the organization and making certain the organization’s general cybersecurity is not sacrificed doing work with 3rd-party methods.
To apply a VRM effectively, companies have to have to have a framework for handling vendor risk. In this article are the 7 ways we endorse having to make absolutely sure your business is safe from seller risk:
1 — Recognize all vendors supplying services for your group
Before you can properly recognize the risk to your small business, you require to know all suppliers utilized by your group. A comprehensive inventory may possibly consist of every thing from garden treatment to credit score card solutions.
Having said that, acquiring a thorough understanding and inventory of all vendors aids to ensure risk is calculated correctly.
2 — Define the acceptable amount of risk for your business
Unique varieties of businesses might have unique expectations and risk parts that differ. For illustration, what is outlined as vital to a health care business may perhaps fluctuate from a money institution. Whatsoever the scenario, pinpointing the appropriate amounts of hazards assists assure the appropriate mitigations are place in location, and the risk is suitable to business stakeholders.
3 — Discover the most critical risks
The risk posed by certain sellers is most possible likely to be higher than other folks. For instance, a garden treatment company with no obtain to your specialized infrastructure will almost certainly be much less risky than a 3rd-party seller with network-level access to specific business-critical methods. Therefore, rating your risk degrees associated to precise vendors is important to understanding your all round risk.
4 — Classify the distributors who offer providers for your small business
Following vendors are discovered who provide services for your organization, these ought to be classified according to what providers they supply and the hazards they pose to your enterprise.
5 — Conduct typical seller risk assessments
Even if a small business poses a slight risk at a single place, this may well improve afterwards. Like your business, the point out of vendor infrastructure, expert services, software program, and cybersecurity posture is regularly in flux. Consequently, perform standard seller assessments to immediately identify a unexpected alter in the risk to your corporation.
6 — Have legitimate contracts with suppliers and proactively track the terms
Make certain you have legitimate contracts with all suppliers. A contractual settlement lawfully establishes the anticipations across all fronts, together with security and risk assessment. Track the contracts and terms around time. It allows pinpointing any deviation from the agreement conditions as expressed.
7 — Keep track of vendor challenges about time
Watch the threats posed by sellers in excess of time. As talked over over, conducting normal seller risk assessments and checking the risk about time aids to acquire visibility into the risk that might continue to improve with a specific vendor. It could signal the will need to look for one more seller.
Track credential security for 3rd-party sellers
An location of concern doing the job with a seller or if you are a third-party seller made use of by an organization is qualifications. How do you ensure that credentials utilized by 3rd-party vendors are protected? How do you prove you are on prime of password security in your natural environment if a organization requests proof of your credential security?
Specops Password Plan is a resolution that will allow corporations to bolster their password security and in general cybersecurity posture by:
- Breached password defense
- Applying strong password policies
- Allowing for the use of numerous password dictionaries
- Apparent and intuitive consumer messaging
- Real-time dynamic responses to the customer
- Size-primarily based password expiration
- Blocking of common password components these types of as usernames in passwords
- Simply apply passphrases
- Standard expressions
Specops Breached Password Protection now involves Dwell Attack Facts as component of the Specops Breached Password Protection module. It will allow Specops Password Policy with Breached Password Safety to shield your group from breached passwords from the two billions of breached passwords in the Specops databases as nicely as from reside attack information.
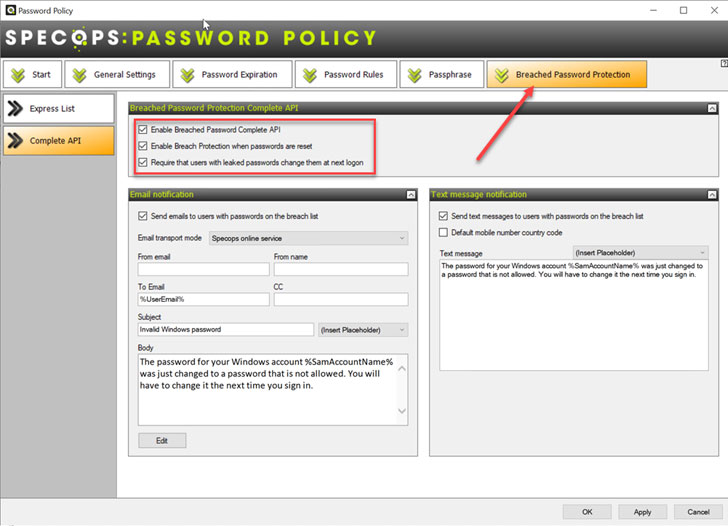 Secure vendor passwords with Specops Breached Password Security
Secure vendor passwords with Specops Breached Password Security
If 3rd-party vendor credentials in use in your environment develop into breached, you will be in a position to remediate the risk as quickly as possible. Also, in conjunction with Specops Password Auditor, you can immediately and quickly deliver reviews of the password expectations you have in position in your organization.
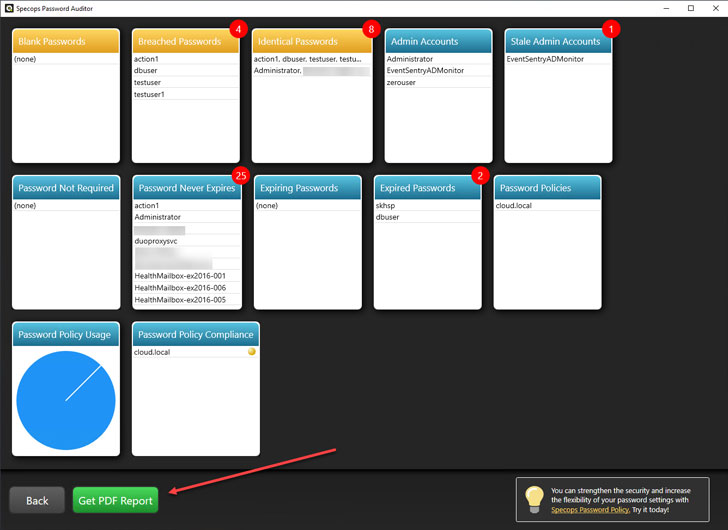 Deliver audit reports using Specops Password Auditor
Deliver audit reports using Specops Password Auditor
Wrapping it Up
Vendor Risk Management (VRM) is an essential portion of the all round cybersecurity processes of companies right now. It makes it possible for controlling the pitfalls connected with 3rd-party distributors and how these interact with your organization. Companies must put into practice a framework to examine vendor risk and be certain these threats are tracked, documented, and monitored as wanted.
Specops Password Plan and Specops Password Auditor enable corporations to bolster password security in their surroundings. It assists mitigate any pitfalls connected with seller passwords and simply monitors passwords to know if these turn into breached. In addition, Password Auditor can make reports if you present third-party expert services to corporations requesting you deliver facts about your password settings and guidelines.
Observed this write-up exciting? Comply with THN on Facebook, Twitter and LinkedIn to browse extra special content we write-up.
Some areas of this article are sourced from:
thehackernews.com


 Attackers Actively Exploiting Realtek SDK Flaws
Attackers Actively Exploiting Realtek SDK Flaws