A previously undocumented Android-based mostly distant obtain trojan (RAT) has been located to use monitor recording characteristics to steal delicate data on the device, including banking qualifications, and open up the door for on-unit fraud.
Dubbed “Vultur” due to its use of Virtual Network Computing (VNC)’s distant monitor-sharing technology to attain comprehensive visibility on specific buyers, the mobile malware was dispersed by means of the official Google Enjoy Retailer and masqueraded as an application named “Safety Guard,” attracting more than 5000 installations. Banking and crypto-wallet apps from entities located in Italy, Australia, and Spain were the principal targets.
“For the to start with time we are looking at an Android banking trojan that has display recording and keylogging as the most important system to harvest login credentials in an automatic and scalable way,” researchers from ThreatFabric said in a compose-up shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“The actors chose to steer absent from the widespread HTML overlay advancement we generally see in other Android banking Trojans: this method generally demands a much larger time and hard work expense from the actors to generate various overlays capable of tricking the consumer. Alternatively, they chose to just report what is revealed on the monitor, properly acquiring the exact close result.”
Whilst banking malware these as MysteryBot, Grandoreiro, Banker.BR, and Vizom have traditionally relied on overlay attacks — i.e., producing a wrong version of the bank’s login webpage and overlaying it on leading of the legitimate application — to trick victims into revealing their passwords and other significant non-public details, evidence is mounting that threat actors are pivoting away from this solution.
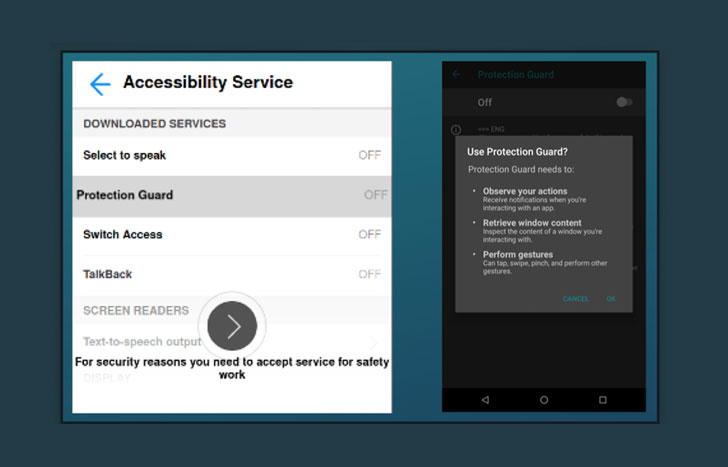
In a report revealed previously this week, Italian cybersecurity company Cleafy uncovered UBEL, an updated variant of Oscorp, that was noticed making use of WebRTC to interact with the compromised Android phone in genuine-time. Vultur adopts a identical tactic in that it will take edge of accessibility permissions to seize keystrokes and leverages VNC’s display screen recording function to stealthily log all routines on the phone, thus obviating the have to have to sign up a new unit and producing it hard for banking companies to detect fraud.
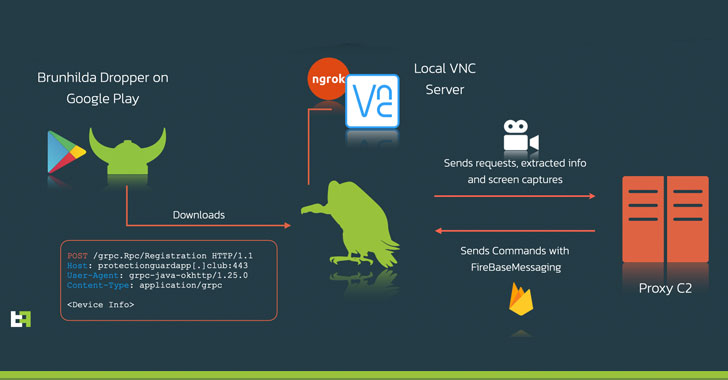
What’s far more, the malware employs ngrok, a cross-platform utility employed to expose regional servers powering NATs and firewalls to the community internet above safe tunnels, to deliver distant obtain to the VNC server jogging locally on the phone. Moreover, it also establishes connections with a command-and-command (C2) server to acquire instructions about Firebase Cloud Messaging (FCM), the effects of which, including extracted knowledge and monitor captures, are then transmitted back to the server.

ThreatFabric’s investigation also connected Vultur with an additional very well-regarded piece of destructive software program named Brunhilda, a dropper that makes use of the Play Keep to distribute distinct sorts of malware in what is actually identified as a “dropper-as-a-services” (DaaS) procedure, citing overlaps in the source code and C2 infrastructure made use of to aid attacks.
These ties, the Amsterdam-based mostly cybersecurity products and services organization mentioned, indicate Brunhilda to be a privately working danger actor that has its have dropper and proprietary RAT Vultur.
“The story of Vultur shows 1 a lot more time how actors change from applying rented Trojans (MaaS) that are marketed on underground marketplaces in the direction of proprietary/personal malware tailor-made to the requires of this group,” the researchers concluded. “These attacks are scalable and automated since the actions to complete fraud can be scripted on the malware backend and sent in the form of commands sequence, building it quick for the actor(s) to strike-and-operate.”
Uncovered this posting fascinating? Observe THN on Facebook, Twitter and LinkedIn to browse much more exceptional written content we write-up.
Some parts of this write-up are sourced from:
thehackernews.com

 Top 30 Critical Security Vulnerabilities Most Exploited by Hackers
Top 30 Critical Security Vulnerabilities Most Exploited by Hackers