Cybersecurity scientists have learned numerous security vulnerabilities in Zimbra email collaboration computer software that could be perhaps exploited to compromise email accounts by sending a destructive concept and even realize a complete takeover of the mail server when hosted on a cloud infrastructure.
The flaws — tracked as CVE-2021-35208 and CVE-2021-35208 — have been learned and described in Zimbra 8.8.15 by scientists from code quality and security alternatives supplier SonarSource in May 2021. Mitigations have due to the fact been released in Zimbra variations 8.8.15 Patch 23 and 9.. Patch 16.
- CVE-2021-35208 (CVSS rating: 5.4) – Saved XSS Vulnerability in ZmMailMsgView.java
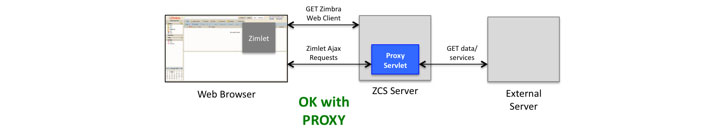
- CVE-2021-35209 (CVSS rating: 6.1) – Proxy Servlet Open up Redirect Vulnerability
“A combination of these vulnerabilities could help an unauthenticated attacker to compromise a total Zimbra webmail server of a focused corporation,” mentioned SonarSource vulnerability researcher, Simon Scannell, who identified the security weaknesses. “As a outcome, an attacker would get unrestricted entry to all despatched and gained e-mails of all workforce.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Zimbra is a cloud-based email, calendar, and collaboration suite for enterprises and is readily available equally as an open up-resource version and a commercially supported version with added functions such as a proprietary connector API to synchronize mail, calendar, and contacts to Microsoft Outlook, amongst many others. It is really made use of by in excess of 200,000 enterprises across 160 countries.
CVE-2021-35208 considerations a cross-web site scripting (XSS) vulnerability in the Calendar Invite element that can be activated in a victim’s browser on viewing a specially-crafted email information that contains a JavaScript payload that, when executed, grants obtain to the target’s complete inbox as very well as the web client session, which can then be abused to start additional attacks.
The issue stems from the truth that the Zimbra web purchasers — an Ajax-primarily based desktop shopper, a static HTML client, and a cell-optimized consumer — complete the sanitization of the HTML written content of incoming e-mail on the server-side and in a way that allows a terrible actor to inject rogue JavaScript code.
“The draw back of making use of server-aspect sanitization is that all a few customers may well renovate the dependable HTML of an email later on to display screen it in their special way,” Scannell stated. “Transformation of previously sanitized HTML inputs can direct to corruption of the HTML and then to XSS attacks.”

On the other hand, CVE-2021-35208 relates to a server facet ask for forgery (SSRF) attack wherein an authenticated member of an organization can chain the flaw with the aforementioned XSS issue to redirect the HTTP shopper used by Zimbra to an arbitrary URL and extract sensitive info from the cloud, which includes Google Cloud API accessibility tokens and IAM qualifications from AWS, top to its compromise.
“Zimbra would like to warn its prospects that it is possible for them to introduce an SSRF security vulnerability in the Proxy Servlet,” the organization mentioned in its advisory. “If this servlet is configured to allow for a distinct area (via zimbraProxyAllowedDomains configuration placing), and that domain resolves to an internal IP address (such as 127…1), an attacker could maybe obtain companies jogging on a diverse port on the similar server, which would normally not be uncovered publicly.”
Found this write-up interesting? Observe THN on Facebook, Twitter and LinkedIn to browse more exceptional content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Three Zero-Day Bugs Plague Kaseya Unitrends Backup Servers
Three Zero-Day Bugs Plague Kaseya Unitrends Backup Servers