A new ransomware strain prepared in Golang dubbed “Agenda” has been noticed in the wild, concentrating on health care and instruction entities in Indonesia, Saudi Arabia, South Africa, and Thailand.
“Agenda can reboot programs in risk-free mode, attempts to prevent a lot of server-certain processes and solutions, and has multiple modes to run,” Development Micro scientists mentioned in an analysis very last week.
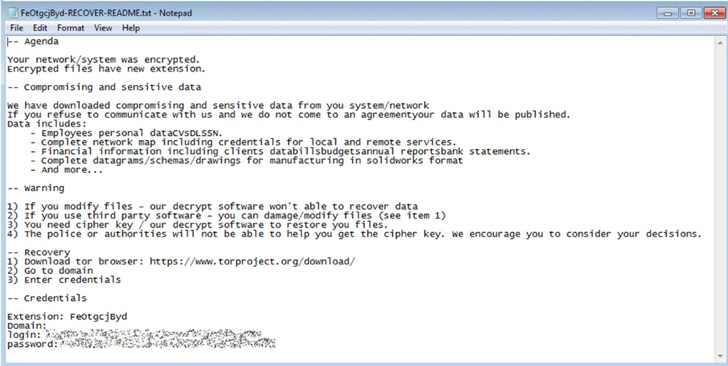
Qilin, the menace actor advertising the ransomware on the dark web, is reported to provide affiliate marketers with selections to tailor the binary payloads for every single victim, enabling the operators to decide the ransom observe, encryption extension, as nicely as the listing of procedures and products and services to terminate before commencing the encryption system.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Furthermore, the ransomware incorporates procedures for detection evasion by taking benefit of the ‘safe mode’ feature of a gadget to move forward with its file encryption plan unnoticed, but not prior to modifying the default user’s password and enabling computerized login.
Upon thriving encryption, Agenda renames the documents with the configured extension, drops the ransom note in every encrypted listing, and reboots the equipment in typical manner. The ransomware amount of money requested varies from firm to corporation, ranging any place from $50,000 to $800,000.
Agenda, besides leveraging regional account credentials to execute the ransomware binary, also comes with capabilities to infect an complete network and its shared drivers.
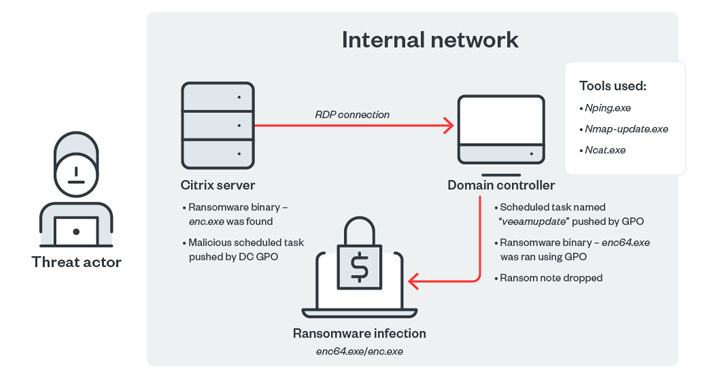
In one particular of the noticed attack chains involving the ransomware, a general public-struggling with Citrix server served as an entry place to in the end deploy the ransomware in significantly less than two days.
Pattern Micro reported it noticed source code similarities among Agenda and the Black Basta, Black Make a difference, and REvil (aka Sodinokibi) ransomware people.

Black Basta, which initially emerged in April 2022, is acknowledged to make use of the double extortion strategy of encrypting data files on the programs of focused corporations and demanding ransom to make decryption doable, although also threatening to publish the stolen delicate details really should a victim pick out not to spend the ransom.
As of final 7 days, the Black Basta team has compromised above 75 corporations, in accordance to Palo Alto Networks Unit 42, up from 50 in June 2022.
Agenda is also the fourth pressure after BlackCat, Hive, and Luna to use the Go programming language. “Ransomware proceeds to evolve, creating much more innovative approaches and procedures to lure businesses,” the researchers explained.
Uncovered this short article intriguing? Comply with THN on Facebook, Twitter and LinkedIn to study much more exceptional material we submit.
Some areas of this short article are sourced from:
thehackernews.com

 Global Ransomware Damages to Exceed $30bn by 2023
Global Ransomware Damages to Exceed $30bn by 2023