Cybersecurity scientists right now disclosed a new kind of modular backdoor that targets position-of-sale (POS) restaurant management software package from Oracle in an attempt to pilfer delicate payment facts saved in the devices.
The backdoor — dubbed “ModPipe” — impacts Oracle MICROS Cafe Organization Collection (RES) 3700 POS methods, extensively used software program suite dining establishments, and hospitality institutions to proficiently handle POS, inventory, and labor management, deployed in restaurant and hospitality sectors mainly in the US.
“What tends to make the backdoor unique are its downloadable modules and their capabilities, as it consists of a personalized algorithm made to assemble RES 3700 POS database passwords by decrypting them from Windows registry values,” ESET researchers stated in an assessment.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Exfiltrated credentials allow ModPipe’s operators access to databases contents, such as a variety of definitions and configuration, status tables and facts about POS transactions.”
It really is worth noting that specifics these types of as credit rating card figures and expiration dates are shielded behind encryption barriers in RES 3700, therefore restricting the quantity of beneficial facts feasible for more misuse, despite the fact that the scientists posit that the actor powering the attacks could be in possession of a second downloadable module to decrypt the contents of the database.
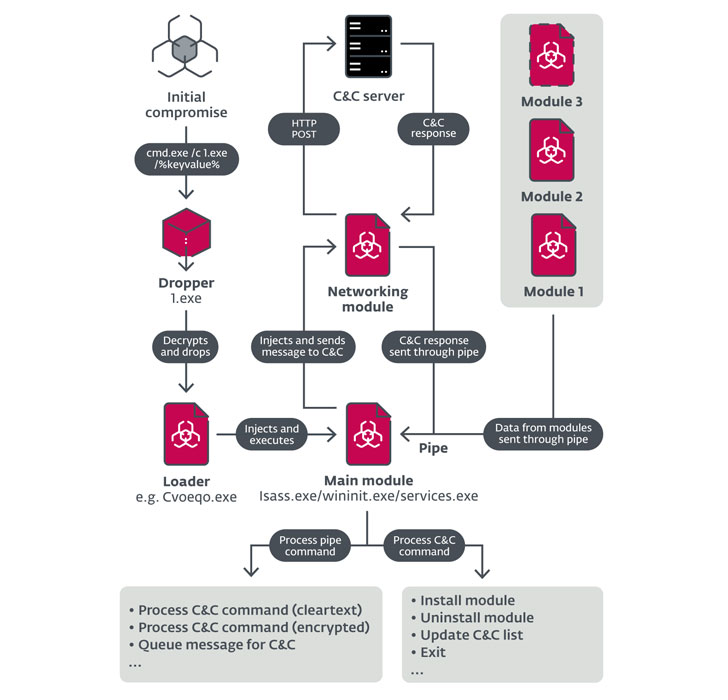
The ModPipe infrastructure is made up of an first dropper that’s employed to install a persistent loader, which then unpacks and loads the subsequent-stage payload — the key malware module that is applied to build communications with other “downloadable” modules and the command-and-regulate (C2) server through a standalone networking module.
Main among the downloadable modules include “GetMicInfo,” a element that can intercept and decrypt database passwords using a distinctive algorithm, which ESET scientists theorize could have been executed possibly by reverse-engineering the cryptographic libraries or by earning use of the encryption implementation details received in the aftermath of a details breach at Oracle’s MICROS POS division in 2016.
A 2nd module called “ModScan 2.20” is devoted to accumulating added information and facts about the mounted POS procedure (e.g., variation, database server facts), whilst a further module by the title of “Proclist” gathers information about at the moment functioning procedures.
“ModPipe’s architecture, modules and their abilities also point out that its writers have substantial knowledge of the focused RES 3700 POS program,” the researchers stated. “The proficiency of the operators could stem from multiple situations, which includes thieving and reverse engineering the proprietary software package product or service, misusing its leaked pieces or acquiring code from an underground market.”
Businesses in the hospitality sector that are employing the RES 3700 POS are encouraged to update to the most current edition of the software program as very well as use equipment that run current versions of the underlying operating procedure.
Observed this post intriguing? Stick to THN on Facebook, Twitter and LinkedIn to go through extra special material we put up.
Some sections of this short article are sourced from:
thehackernews.com


 The essential cyber security toolkit for SMBs
The essential cyber security toolkit for SMBs