An unidentified risk actor with the capabilities to evolve and tailor its toolset to target environments infiltrated large-profile corporations in Asia and Africa with an evasive Windows rootkit because at minimum 2018.
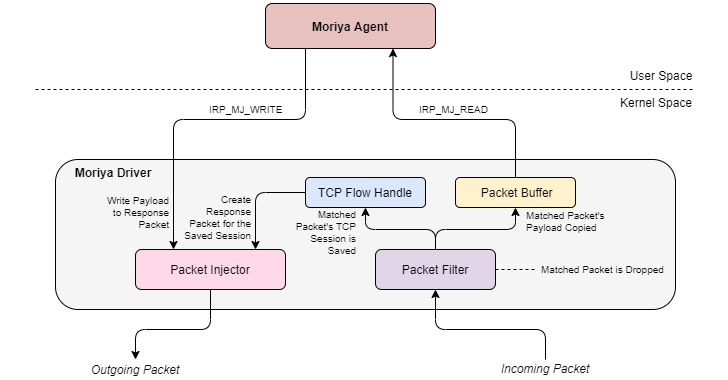
Named ‘Moriya,’ the malware is a “passive backdoor which will allow attackers to inspect all incoming site visitors to the contaminated equipment, filter out packets that are marked as selected for the malware and react to them,” stated Kaspersky researchers Mark Lechtik and Giampaolo Dedola in a Thursday deep-dive.
The Russian cybersecurity firm termed the ongoing espionage marketing campaign ‘TunnelSnake.’ Dependent on telemetry analysis, significantly less than 10 victims all around the planet have been focused to date, with the most distinguished victims getting two huge diplomatic entities in Southeast Asia and Africa. All the other victims have been positioned in South Asia.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The initial studies of Moriya emerged past November when Kaspersky claimed it uncovered the stealthy implant in the networks of regional inter-governmental organizations in Asia and Africa. Malicious exercise affiliated with the operation is claimed to have dated back to November 2019, with the rootkit persisting in the target networks for many months following the original infection.
“This resource was made use of to handle community struggling with servers in all those corporations by creating a covert channel with a C2 server and passing shell commands and their outputs to the C2,” the firm reported in its APT trends report for Q3 2020. “This ability is facilitated using a Windows kernel manner driver.”
Rootkits are especially perilous as they allow attackers to get significant privileges in the method, enabling them to intercept main enter/output functions carried out by the fundamental working procedure and improved blend with the landscape, hence earning it complicated to trace the attacker’s electronic footprints.
Microsoft, for its portion, has executed a number of protections into Windows over the years to reduce productive deployment and execution of rootkits, which tends to make Moriya all the far more noteworthy.
Bulk of the toolset, aside from the backdoor, consists of each proprietary and very well-identified pieces of malware these as China Chopper web shell, BOUNCER, Earthworm, and Termite that have been earlier utilised by Chinese-talking danger actors, supplying an insight into the attacker’s origins. The ways, approaches, and techniques (TTPs) utilised in the attacks also display that the qualified entities match the victimology sample related with Chinese-speaking adversaries.
The revelations arrive as state-of-the-art persistent threats (APTs) carry on to ramp up really-qualified data-stealing missions, even though simultaneously likely to terrific lengths to continue to be beneath the radar for as lengthy as achievable, rebuild their malware arsenal, generating them extra tailor-made, sophisticated, and more difficult to detect.
“The TunnelSnake marketing campaign demonstrates the activity of a innovative actor that invests important assets in building an evasive toolset and infiltrating networks of substantial-profile businesses,” Lechtik and Dedola reported. “By leveraging Windows motorists, covert communications channels and proprietary malware, the group powering it maintains a significant stage of stealth.”
Uncovered this report attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to read through additional special content we put up.
Some parts of this short article are sourced from:
thehackernews.com


 The IT Pro Podcast: Should companies spy on their employees?
The IT Pro Podcast: Should companies spy on their employees?