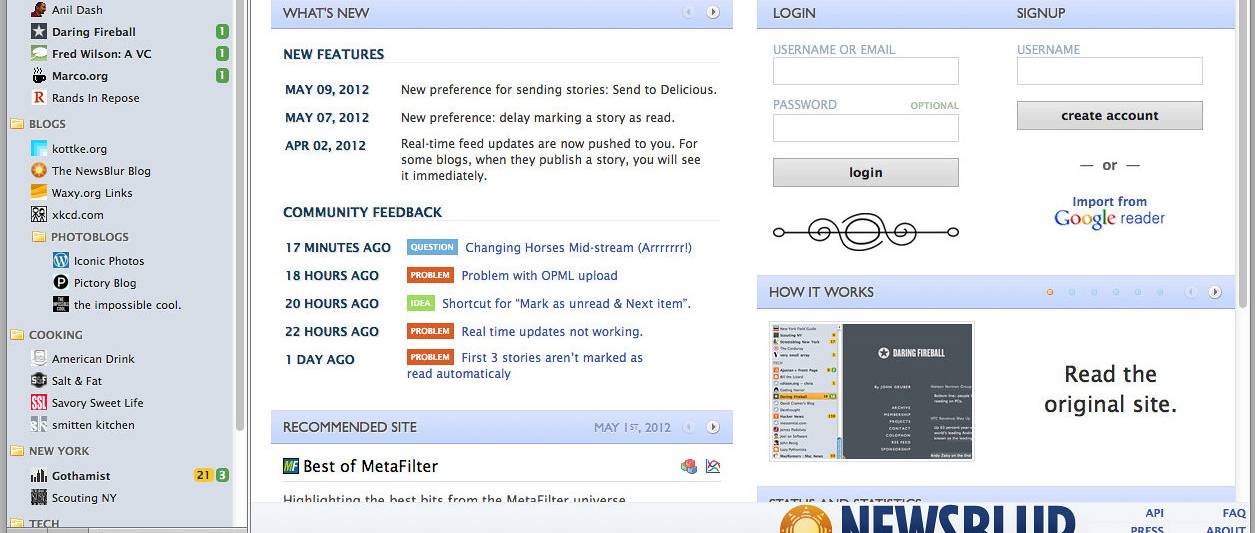
Own news reader NewsBlur remaining down for quite a few hours final week adhering to a knowledge exposure. (“newsblur start” by renaissancechambara is accredited under CC BY 2.)
Turns out the recent story about the own information reader NewsBlur being down for numerous hrs last week next a data exposure has a content ending: the proprietor retained an unique duplicate of the databases that was compromised and restored the provider in 10 hrs.
The real databases publicity was triggered by a persistent dilemma with Docker, an issue that is been pretty perfectly-regarded in the Linux group for quite a few many years. Evidently, when sys admins use Docker to containerize a databases on a Linux server, Docker inserts an “allow rule” into iptables, opening up the database to the general public internet. This involves sys admins to reconfigure the uncomplicated firewall (UFW) configuration file on the server and insert new procedures for Docker.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In the NewsBlur case, the database (about 250 gigabytes) was compromised and ransomed although the RSS reader was applying Docker to containerize a MongoDB. NewsBlur founder Samuel Clay reported in a site article that the hacker was equipped to duplicate the database and delete the first in about a few hours.
Clay utilized some finest techniques security professionals should take into consideration: appropriate ahead of he transitioned to Docker, he shut down the initial major MongoDB cluster, which was untouched during the attack. At the time he was aware of the issue, Clay then took the snapshot of the first MongoDB, restored the databases, patched the Docker flaw, and received the support up and jogging.
It is examples like the NewsBlur situation that display why container security has turn into one of the fastest expanding regions in cybersecurity, said Ray Kelly, principal security engineer at WhiteHat Security. Kelly stated businesses are relocating at a frantic rate to go to containerized architectures to enable with scalability and redundancy – and they often really do not look at the security implications.
“Each container is effectively its own mini OS and wants to be vetted for security vulnerabilities this kind of as privileges/roles, application layer attacks and in this circumstance network and firewall openings,” Kelly explained. “Ideally these responsibilities are done before going reside. Regretably, security generally receives placed in the back of the queue in favor of new features and quick deployments.”
Andrew Barratt, controlling principal, remedies and investigations at Coalfire, extra that as the architecture of our devices turns into much more elaborate, with far more automation, containerization, and virtualization, it’s important to not make any assumptions about the security configurations.
“Active screening of these would have caught this early if done by an experienced adversary simulation or most probably even a a lot more common architectural overview,” Barratt explained. “Sadly, the tables got dropped and the information was no far more. At least in this instance, there was no want to pay out the ransom.”
Some elements of this post are sourced from:
www.scmagazine.com

 Indexsinas SMB Worm Campaign Infests Whole Enterprises
Indexsinas SMB Worm Campaign Infests Whole Enterprises