A Turkish-talking entity termed Nitrokod has been attributed to an energetic cryptocurrency mining campaign that involves impersonating a desktop software for Google Translate to infect above 111,000 victims in 11 nations considering the fact that 2019.
“The malicious equipment can be made use of by anyone,” Maya Horowitz, vice president of study at Test Point, reported in a assertion shared with The Hacker Information. “They can be found by a very simple web search, downloaded from a website link, and installation is a very simple double-simply click.”
The checklist of international locations with victims contains the U.K., the U.S., Sri Lanka, Greece, Israel, Germany, Turkey, Cyprus, Australia, Mongolia, and Poland.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The marketing campaign involves serving malware by no cost computer software hosted on well-liked sites this sort of as Softpedia and Uptodown. But in an intriguing tactic, the malware puts off its execution for weeks and separates its malicious activity from the downloaded phony program to steer clear of detection.
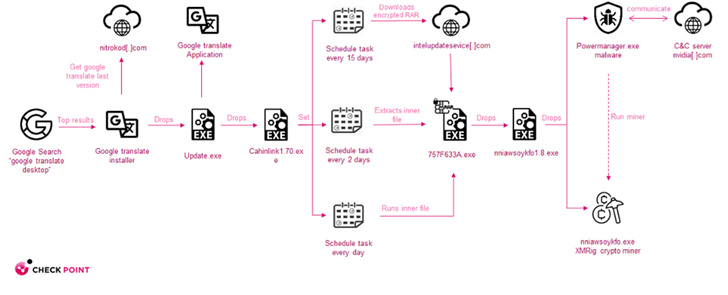
The set up of the infected plan is adopted by deployment of an update executable to the disk that, in switch, kick-commences a four-phase attack sequence, with each dropper paving for the subsequent, until eventually the precise malware is dropped in the seventh phase.
Upon execution of the malware, a relationship to a remote command-and-command (C2) server is set up to retrieve a configuration file to initiate the coin mining action.

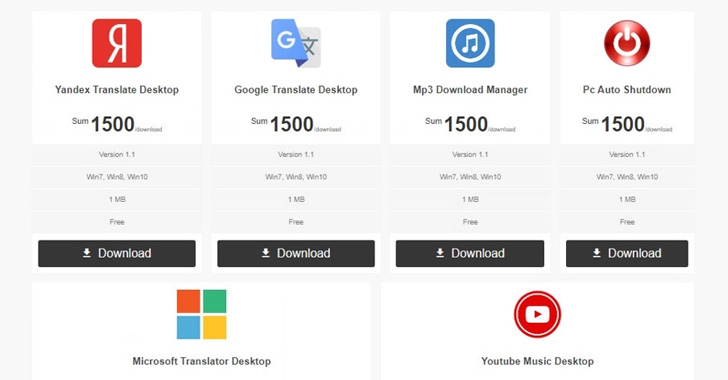
A notable factor of the Nitrokod campaign is that the phony application supplied for free are for providers that do not have an official desktop edition, these types of as Yandex Translate, Microsoft Translate, YouTube Audio, MP3 Obtain Manager, and Computer system Car Shutdown.
In addition, the malware is dropped virtually a thirty day period soon after the preliminary infection, by when the forensic path is deleted, creating it difficult to split down the attack and trace it back again to the installer.
“What’s most appealing to me is the actuality that the destructive software program is so well-known, nonetheless went below the radar for so prolonged,” Horowitz explained. “The attacker can easily pick out to alter the ultimate payload of the attack, shifting it from a crypto miner to, say, ransomware or banking trojan.”
Discovered this write-up appealing? Adhere to THN on Facebook, Twitter and LinkedIn to examine extra unique content we post.
Some pieces of this report are sourced from:
thehackernews.com

 A CISO’s Ultimate Security Validation Checklist
A CISO’s Ultimate Security Validation Checklist