The notorious Emotet malware is staging a comeback of types nearly 10 months just after a coordinated law enforcement operation dismantled its command-and-regulate infrastructure in late January 2021.
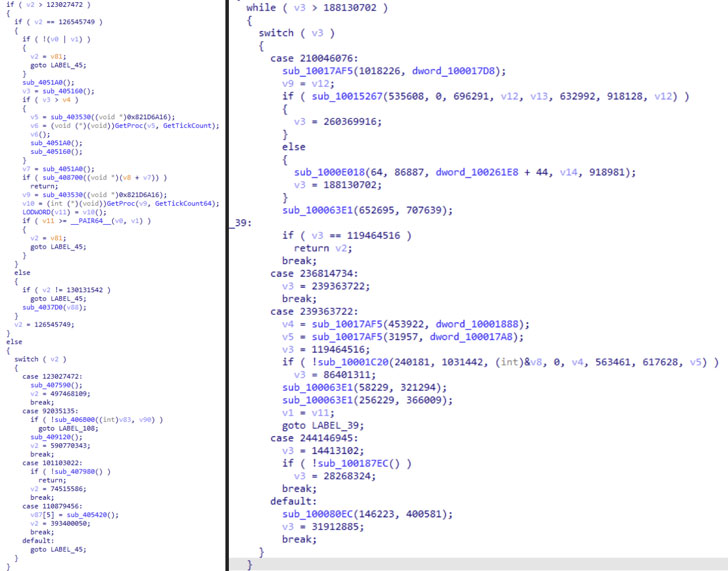
In accordance to a new report from security researcher Luca Ebach, the notorious TrickBot malware is becoming applied as an entry place to distribute what appears to be a new model of Emotet on methods earlier contaminated by the previous. The most current variant will take the sort of a DLL file, with the initially occurrence of the deployment getting detected on November 14.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Europol dubbed Emotet as the “world’s most unsafe malware” for its ability to act as a “doorway opener” for danger actors to obtain unauthorized entry, turning out to be a precursor to numerous critical facts theft and ransomware attacks. Curiously, the loader procedure enabled other malware family members this sort of as Trickbot, QakBot, and Ryuk to enter a machine.
The resurfacing is also substantial not minimum because it follows concerted attempts on the part of the regulation enforcement to instantly uninstall the malware en masse from the compromised pcs in April.

As of composing, malware tracking study task Abuse.ch’s Feodo Tracker demonstrates nine Emotet command-and-handle servers that are at the moment on the web.
Samples of the new Emotet loader can be accessed right here. To avoid units from staying co-opted into the freshly energetic Emotet botnet, network administrators are strongly advised to block all the suitable IP addresses.
Observed this post intriguing? Comply with THN on Facebook, Twitter and LinkedIn to study extra distinctive information we put up.
Some sections of this write-up are sourced from:
thehackernews.com

 New ‘Moses Staff’ Hacker Group Targets Israeli Companies With Destructive Attacks
New ‘Moses Staff’ Hacker Group Targets Israeli Companies With Destructive Attacks