At minimum 300,000 IP addresses involved with MikroTik gadgets have been found vulnerable to several remotely exploitable security vulnerabilities that have considering the fact that been patched by the popular provider of routers and wireless ISP devices.
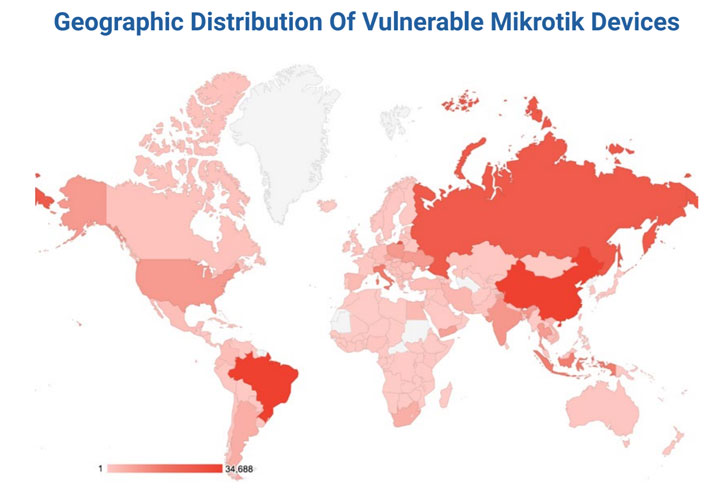
The most affected devices are situated in China, Brazil, Russia, Italy, Indonesia, with the U.S. coming in at number eight, cybersecurity business Eclypsium explained in a report shared with The Hacker News.
“These gadgets are both strong, [and] typically hugely susceptible,” the researchers pointed out. “This has made MikroTik units a favored among threat actors who have commandeered the units for everything from DDoS attacks, command-and-command (aka ‘C2’), visitors tunneling, and far more.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
MikroTik gadgets are an enticing focus on not minimum for the reason that there are more than two million of them deployed globally, posing a substantial attack area that can be leveraged by menace actors to mount an array of intrusions.

In fact, before this September, stories emerged of a new botnet named Mēris that staged a file-breaking dispersed denial-of-provider (DDoS) attack towards Russian internet enterprise Yandex by working with network devices from Mikrotik as an attack vector by exploiting a now-addressed security vulnerability in the running process (CVE-2018-14847).
The checklist of four vulnerabilities identified over the past three yrs and which could allow whole takeover of MikroTik products is below –
- CVE-2019-3977 (CVSS score: 7.5) – MikroTik RouterOS inadequate validation of up grade package’s origin, allowing for a reset of all usernames and passwords
- CVE-2019-3978 (CVSS rating: 7.5) – MikroTik RouterOS insufficient protections of a critical resource, major to cache poisoning
- CVE-2018-14847 (CVSS rating: 9.1) – MikroTik RouterOS directory traversal vulnerability in the WinBox interface
- CVE-2018-7445 (CVSS score: 9.8) – MikroTik RouterOS SMB buffer overflow vulnerability
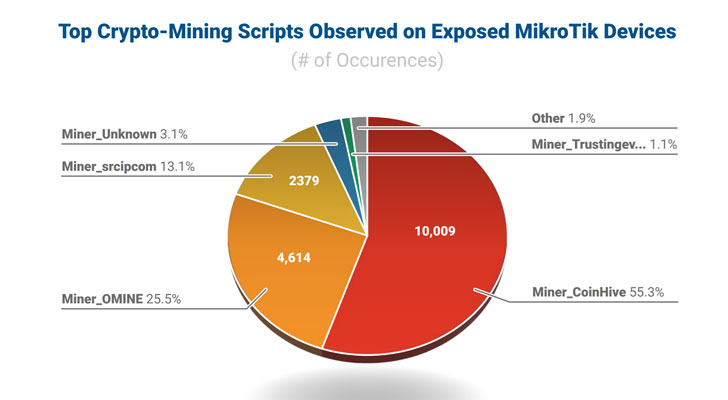
In addition, Eclypsium scientists stated they located 20,000 uncovered MikroTik products that injected cryptocurrency mining scripts into web internet pages that users visited.

“The skill for compromised routers to inject malicious content, tunnel, duplicate, or reroute visitors can be utilized in a wide variety of really harming techniques,” the scientists reported. “DNS poisoning could redirect a remote worker’s relationship to a destructive web-site or introduce a device-the-center.”
“An attacker could use perfectly-known methods and equipment to most likely seize delicate information this sort of as thieving MFA qualifications from a remote consumer making use of SMS around WiFi. As with prior attacks, enterprise site visitors could be tunneled to another area or destructive information injected into valid visitors,” the researchers added.
MikroTik routers are much from the only products to have been co-opted into a botnet. Researchers from Fortinet this 7 days disclosed how the Moobot botnet is leveraging a recognised distant code execution (RCE) vulnerability in Hikvision video clip surveillance products and solutions (CVE-2021-36260) to mature its network, and use the compromised units to start distributed denial-of-assistance (DDoS) attacks.
Discovered this report appealing? Observe THN on Fb, Twitter and LinkedIn to go through more exceptional content material we submit.
Some sections of this report are sourced from:
thehackernews.com


 Android bug prevents users from calling emergency services
Android bug prevents users from calling emergency services