Researchers have uncovered a new established of fraudulent Android applications in the Google Engage in keep that have been found to hijack SMS concept notifications for carrying out billing fraud.
The applications in question mostly targeted users in Southwest Asia and the Arabian Peninsula, attracting a complete of 700,000 downloads before they have been found out and removed from the platform.
The conclusions were described independently by cybersecurity corporations Development Micro and McAfee.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

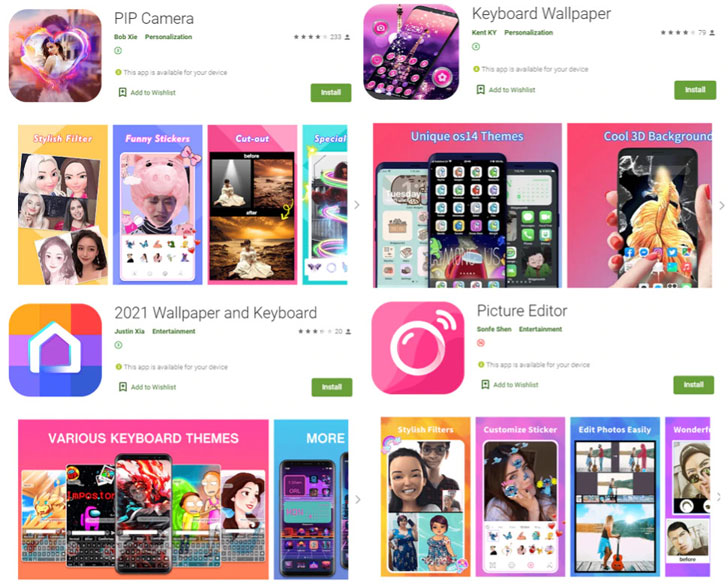
“Posing as photograph editors, wallpapers, puzzles, keyboard skins, and other camera-connected apps, the malware embedded in these fraudulent apps hijack SMS message notifications and then make unauthorized purchases,” researchers from McAfee explained in a Monday produce-up.
The fraudulent applications belong to the so-known as “Joker” (aka Bread) malware, which has been observed to regularly sneak previous Google Play defenses over the previous 4 yrs, resulting in Google removing no less than 1,700 infected apps from the Engage in Retail store as of early 2020. McAfee, having said that, is tracking the danger below a individual moniker named “Etinu.”
The malware is notorious for perpetrating billing fraud and its spy ware capabilities, which includes stealing SMS messages, get hold of lists, and device info. The malware authors commonly use a approach called versioning, which refers to uploading a clear edition of the app to the Perform Retail outlet to construct belief among end users and then sneakily including destructive code at a afterwards stage via app updates, in a bid to slip through the application evaluation system.
The additional code injected serves as the 1st-phase payload, which masquerades seemingly innocuous .PNG data files and establishes with a command-and-regulate (C2) server to retrieve a secret essential that’s used to decrypt the file to a loader. This interim payload then loads the encrypted 2nd payload that is in the end decrypted to put in the malware.
McAfee’s investigation of the C2 servers discovered users’ private details, together with carrier, phone range, SMS message, IP deal with, place, network standing, together with car-renewing subscriptions.

The record of 9 applications is underneath –
- Keyboard Wallpaper (com.studio.keypaper2021)
- PIP Photo Maker (com.pip.editor.digicam)
- 2021 Wallpaper and Keyboard (org.my.favorites.up.keypaper)
- Barber Prank Hair Dryer, Clipper and Scissors (com.super.shade.hairdryer)
- Picture Editor (com.ce1ab3.app.picture.editor)
- PIP Digicam (com.strike.digital camera.pip)
- Keyboard Wallpaper (com.daynight.keyboard.wallpaper)
- Pop Ringtones for Android (com.tremendous.star.ringtones)
- Awesome Girl Wallpaper/SubscribeSDK (neat.girly.wallpaper)
Buyers who have downloaded the apps are urged to test for any unauthorized transactions even though also taking ways to enjoy out for suspicious permissions asked for by apps and diligently scrutinize applications in advance of they are installed on the products.
“Judging by how Joker operators frequently be certain the malware’s persistence in Google Play even following remaining caught a lot of periods, most probably there are strategies [the operators] are profiting from this plan,” Development Micro scientists stated.
Observed this short article appealing? Abide by THN on Facebook, Twitter and LinkedIn to examine much more special articles we publish.
Some parts of this posting are sourced from:
thehackernews.com


 eBay, Apple, Microsoft, Facebook, and Google were phishers’ top targets in 2020
eBay, Apple, Microsoft, Facebook, and Google were phishers’ top targets in 2020