The PlugX distant entry trojan has been noticed masquerading as an open up resource Windows debugger tool termed x64dbg in an attempt to circumvent security protections and attain management of a target system.
“This file is a reputable open-resource debugger instrument for Windows that is usually made use of to analyze kernel-method and person-mode code, crash dumps, or CPU registers,” Pattern Micro scientists Buddy Tancio, Jed Valderama, and Catherine Loveria reported in a report printed final 7 days.
PlugX, also known as Korplug, is a publish-exploitation modular implant, which, among the other factors, is acknowledged for its numerous functionalities these types of as details exfiltration and its potential to use the compromised device for nefarious applications.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Whilst first documented a 10 years in the past in 2012, early samples of the malware day as considerably as February 2008, in accordance to a Craze Micro report at the time. More than the yrs, PlugX has been employed by risk actors with a Chinese nexus as perfectly as cybercrime teams.
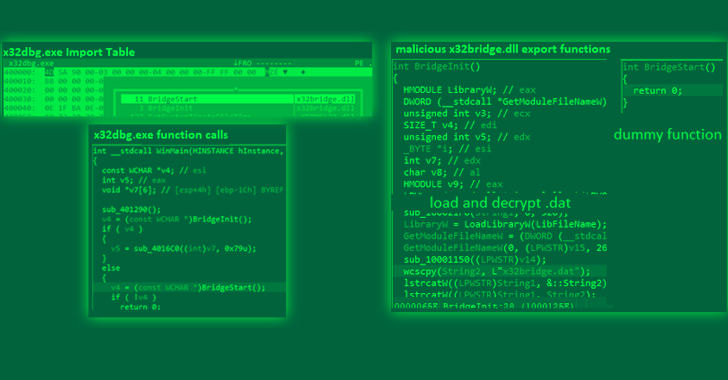
A single of the critical techniques the malware employs is a procedure DLL side-loading to load a malicious DLL from a digitally signed application software, in this circumstance the x64dbg debugging tool (x32dbg.exe).
It is really truly worth noting in this article that DLL aspect-loading attacks leverage the DLL look for purchase mechanism in Windows to plant and then invoke a respectable application that executes a rogue payload.
“Staying a genuine application, x32dbg.exe’s valid electronic signature can confuse some security tools, enabling danger actors to fly underneath the radar, retain persistence, escalate privileges, and bypass file execution constraints,” the scientists stated.
The hijacking of x64dbg to load PlugX was disclosed past month by Palo Alto Networks Unit 42, which learned a new variant of the malware that hides malicious data files on detachable USB gadgets to propagate the infection to other Windows hosts.
Persistence is attained by way of Windows Registry modifications and the development of scheduled duties to make sure continued entry even soon after process restarts.
Pattern Micro’s evaluation of the attack chain also exposed the use of x32dbg.exe to deploy a backdoor, a UDP shell customer that collects method details and awaits more instructions from a distant server.
“In spite of innovations in security technology, attackers carry on to use [DLL side-loading] because it exploits a fundamental trust in legitimate applications,” the researchers mentioned.
“This strategy will keep on being viable for attackers to provide malware and acquire obtain to delicate details as extended as programs and programs carry on to belief and load dynamic libraries.”
Found this posting attention-grabbing? Comply with us on Twitter and LinkedIn to browse additional unique written content we publish.
Some sections of this post are sourced from:
thehackernews.com

 Police Arrest Trio in Multimillion-Dollar Extortion Case
Police Arrest Trio in Multimillion-Dollar Extortion Case