Researchers from European cybersecurity seller ESET have observed beforehand undocumented custom backdoors and applications employed by a reasonably new APT team named Polonium.
First found in June 2022 by the Microsoft Threat Intelligence Centre (MSTIC), Polonium is a extremely sophisticated, currently active hacking team, which appears to be exclusively focusing on Israeli organizations for cyber-espionage uses – they have not so much deployed sabotage equipment these types of as ransomware or wipers.
Microsoft scientists have joined Polonium to Lebanon and assessed the group has ties with Iran’s Ministry of Intelligence and Security (MOIS).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
ESET’s results, introduced at the Virus Bulletin 2022 conference in late September and revealed on October 11, 2022, show that Polonium has targeted far more than a dozen businesses considering the fact that at minimum September 2021. Their victims consist of businesses in engineering, facts technology, legislation, communications, branding and marketing and advertising, media, insurance and social providers. The group’s most new steps have been noticed in September 2022.
Polonium has created custom made instruments for getting screenshots, logging keystrokes, spying by way of webcam, opening reverse shells, exfiltrating files and extra. Their toolset is made up of many open-supply equipment, the two custom and off-the-shelf, as properly as 7 personalized backdoors:
- CreepyDrive, which abuses OneDrive and Dropbox cloud services for command & handle (C&C)
- CreepySnail, which executes commands gained from the attackers’ possess infrastructure
- DeepCreep and MegaCreep, which make use of Dropbox and Mega file storage solutions respectively
- FlipCreep, TechnoCreep and PapaCreep, which receive instructions from attackers’ servers
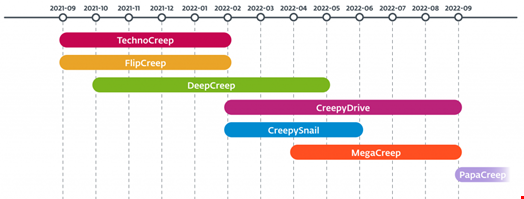
The most recent backdoor, PapaCreep, spotted in September 2022, was undocumented ahead of ESET’s analysis was produced general public. It is a modular backdoor, breaking its command execution, C&C communication, file upload and file down load capabilities into tiny components. “The edge is that the elements can run independently, persist by using separate scheduled responsibilities in the breached program, and make the backdoor more durable to detect,” BleepingComputer claimed.
“The several versions and improvements Polonium launched into its custom instruments present a continual and extended-time period work to spy on the group’s targets,” ESET said.
Though ESET was unable to discover how the team gained first entry to the qualified methods, some of the victims’ Fortinet VPN account credentials were leaked in September 2021 and designed obtainable on the net. “As these kinds of, it is possible that the attackers gained access to the victims’ interior networks by abusing those leaked VPN qualifications,” ESET added.
This correlates with previous results by Microsoft, which noted in June 2022 that the team was making use of identified VPN solution flaws to breach networks.
“Polonium didn’t use domain names in any of the samples that we analyzed, only IP addresses. Most of the servers are dedicated digital private servers (VPS), probable acquired rather than compromised, hosted at HostGW,” ESET stated, earning it more difficult to map the group’s actions.
Some sections of this article are sourced from:
www.infosecurity-journal.com


 #ISC2Congress: US Government is Embracing ‘Collective Defense’
#ISC2Congress: US Government is Embracing ‘Collective Defense’