In what is yet a further act of sabotage, the developer behind the preferred “node-ipc” NPM package deal delivered a new version to protest Russia’s invasion of Ukraine, increasing problems about security in the open up-source and the software package supply chain.
Impacting versions 10.1.1 and 10.1.2 of the library, the changes introduced unwanted behavior by its maintainer RIAEvangelist, targeting end users with IP addresses situated both in Russia or Belarus, and wiping arbitrary file contents and replacing it with a heart emoji.
Node-ipc is a prominent node module utilized for regional and distant inter-method interaction with help for Linux, macOS, and Windows. It has more than 1.1 million weekly downloads.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“A quite distinct abuse and a critical provide chain security incident will take place for any system on which this NPM package will be referred to as upon, if that matches a geo-spot of both Russia or Belarus,” Synk researcher Liran Tal said in an evaluation.
The issue has been assigned the identifier CVE-2022-23812 and is rated 9.8 out of 10 on the CVSS vulnerability scoring system. The destructive code alterations had been posted on March 7 (variation 10.1.1), with a next update developing 10 hours later on the very same working day (model 10.1.1).
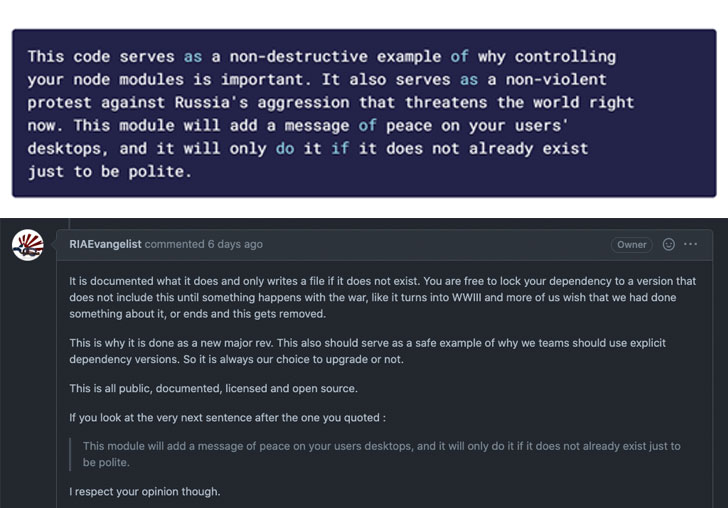
Apparently, although the harmful payload was taken out from the library with variation 10.1.3, a significant update was pushed soon after significantly less than 4 hours (version 11..), which imported one more dependency termed “peacenotwar,” also introduced by RIAEvangelist as variety of “non-violent protest from Russia’s aggression.”
“Any time the node-ipc module operation will get termed, it prints to STDOUT a information taken out of the peacenotwar module, as very well as sites a file on the user’s Desktop directory with contents relating to the current war-time condition of Russia and Ukraine,” Tal explained.
As of March 15, 2022, the hottest version of node-ipc – 11.1. – bumps the “peacenotwar” bundle model from 9.1.3 to 9.1.5 and bundles the “colors” NPM library, although also getting rid of the STDOUT console messages.
It truly is value noting that “colours,” along with a further bundle called “faker,” ended up the two deliberately sabotaged previously this January by its developer Marak Squires by introducing infinite loops to the source code, correctly breaking other programs that depended on the libraries.
In accordance to Bleeping Computer system, which first claimed the corruption, the improvements are claimed to have been retaliatory, with the developer noting that “Respectfully, I am no for a longer time likely to support Fortune 500s (and other scaled-down sized companies) with my absolutely free function.”
If something, the notion of using common modules as “protestware” to deploy damaging payloads and stage a source chain compromise operates the risk of undermining belief in open-supply software package.
“This security incident involves damaging acts of corrupting files on disk by one maintainer and their attempts to cover and restate that deliberate sabotage in various forms,” Tal stated. “Whilst this is an attack with protest-pushed motivations, it highlights a larger sized issue dealing with the application source chain: the transitive dependencies in your code can have a massive affect on your security.”
Uncovered this article exciting? Comply with THN on Fb, Twitter and LinkedIn to study more unique content material we post.
Some elements of this report are sourced from:
thehackernews.com


 Reporting Mandates to Clear Up Feds’ Hazy Look into Threat Landscape – Podcast
Reporting Mandates to Clear Up Feds’ Hazy Look into Threat Landscape – Podcast