Colonial Pipeline, which carries 45% of the gasoline eaten on the U.S. East Coastline, on Saturday explained it halted operations owing to a ransomware attack, once once again demonstrating how infrastructure is susceptible to cyberattacks.
“On May 7, the Colonial Pipeline Firm figured out it was the sufferer of a cybersecurity attack,” the firm mentioned in a statement posted on its internet site. “We have because determined that this incident entails ransomware. In response, we proactively took particular units offline to comprise the danger, which has temporarily halted all pipeline functions, and impacted some of our IT techniques.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Colonial Pipeline is the greatest refined merchandise pipeline in the U.S., a 5,500 mile (8,851 km) technique associated in transporting around 100 million gallons from the Texas city of Houston to New York Harbor.
Cybersecurity firm FireEye’s Mandiant incident response division is claimed to be helping with the investigation, according to studies from Bloomberg and The Wall Street Journal, with the attack linked to a ransomware pressure identified as DarkSide.
“We are engaged with Colonial and our interagency companions concerning the circumstance,” the U.S. Cybersecurity and Infrastructure Security Company (CISA) reported. “This underscores the threat that ransomware poses to businesses irrespective of size or sector. We really encourage each firm to acquire action to fortify their cybersecurity posture to lower their exposure to these sorts of threats.”
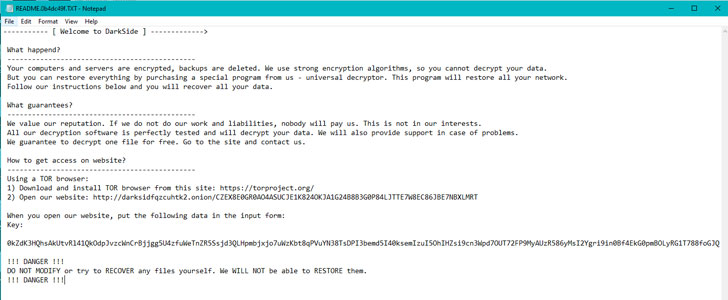 Darkside ransom be aware
Darkside ransom be aware
An evaluation of the ransomware revealed by Cybereason previously in April 2021 reveals that DarkSide has a pattern of remaining used in opposition to targets in English-speaking international locations, even though keeping away from entities found in previous Soviet Bloc nations.
The operators at the rear of the ransomware also just lately switched to an affiliate application in March, wherein risk actors are recruited to distribute the malware by breaching company network victims, although the main developers choose demand of preserving the malware and payment infrastructure.
DarkSide, which commenced functions in August 2020, has released stolen facts from additional than 40 victims to date. It is really not instantly distinct how substantially cash the attackers demanded or no matter if Colonial Pipeline has paid out. A different report from Bloomberg alleged that the cybercriminals driving the attack stole 100GB of details from its network.
Mounting Threat of Ransomware
The most current cyber attack comes as a coalition of government and tech firms in the personal sector, termed the Ransomware Endeavor Power, unveiled a listing of 48 suggestions to detect and disrupt the mounting ransomware menace, in addition to aiding corporations get ready and react to such attacks much more efficiently.
Perhaps damaging intrusions focusing on utilities and critical infrastructure have witnessed a surge in modern many years, fueled in portion by ransomware attacks that have ever more jumped on the double extortion bandwagon to not only encrypt the victim’s data, but exfiltrate the information beforehand and threaten to make it general public if the ransom demand from customers is not paid.
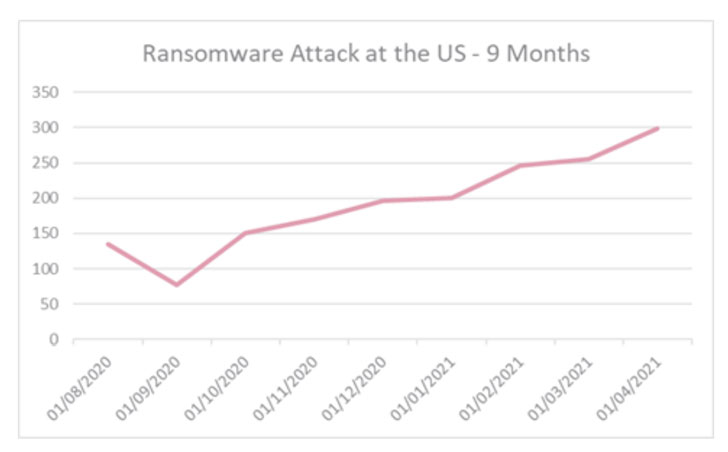
Dependent on facts gathered by Verify Stage and shared with The Hacker News, cyberattacks targeting American utilities jumped by 50% on average for each week, from 171 at the begin of March to 260 to the stop of April. What is additional, around the past nine months, the regular monthly selection of ransomware attacks in the U.S. practically tripled to 300.
“Also, in recent months an ordinary of 1 in each individual 88 Utilities firm in the U.S. experienced from an tried Ransomware attack, up by 34% when compared to the common from the commencing of 2021,” the American-Israeli cybersecurity company mentioned.
In February 2020, CISA issued an warn warning of growing ransomware infections impacting pipeline operations pursuing an attack that strike an unnamed normal fuel compression facility in the country, resulting in the corporation to shut down its pipeline asset for about two times.
Securing pipeline infrastructure has been an location of target for the Office of Homeland Security, which in 2018 assigned CISA to oversee what is known as the Pipeline Cybersecurity Initiative (PCI) that aims to recognize and address emerging threats and put into action security steps to protect more than 2.7 million miles of pipelines dependable for transporting oil and pure gas in the U.S.
The agency’s Countrywide Risk Administration Middle (NRMC) has also revealed a Pipeline Cybersecurity Assets Library in February 2021 to “deliver pipeline facilities, corporations, and stakeholders with a set of absolutely free, voluntary means to reinforce their cybersecurity posture.”
Observed this posting interesting? Stick to THN on Fb, Twitter and LinkedIn to read through extra exceptional material we put up.
Some elements of this short article are sourced from:
thehackernews.com


 Major U.S. Pipeline Crippled in Ransomware Attack
Major U.S. Pipeline Crippled in Ransomware Attack