Cyber criminals are utilizing a beforehand undocumented phishing-as-a-support (PhaaS) toolkit called Caffeine to properly scale up their attacks and distribute nefarious payloads.
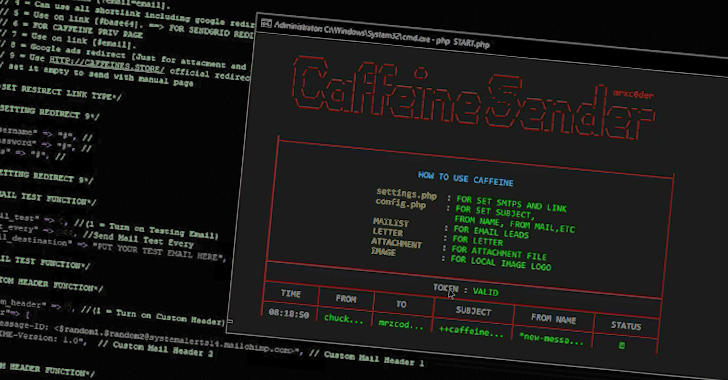
“This platform has an intuitive interface and will come at a somewhat minimal price when offering a multitude of attributes and tools to its felony customers to orchestrate and automate core things of their phishing strategies,” Mandiant stated in a new report.
Some of the main attributes supplied by the platform comprise the skill to craft custom made phishing kits, regulate redirect internet pages, dynamically produce URLs that host the payloads, and keep track of the results of the campaigns.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The enhancement comes a tiny in excess of a thirty day period soon after Resecurity took the wraps off an additional PhaaS service dubbed EvilProxy that is provided for sale on dark web legal boards.
But not like EvilProxy, whose operators are identified to vet potential consumers before activating the subscriptions, Caffeine is noteworthy for running an open up registration process, correctly enabling any one with an email handle to indicator up for the service.
This restriction-free strategy not only obviates the need to have for approaching the actors on underground community forums or demanding a referral from an current consumer, but also makes it possible for Caffeine to fast extend its clientele and decreased the barrier for entry.
Earning it further stand aside from the relaxation, the PhaaS toolkit is noteworthy for featuring phishing email templates for use versus Chinese and Russian targets.
“Although the use of phishing platforms is absolutely not a novel mechanism to facilitate attacks, it is well worth noting that these types of element-abundant alternatives, like Caffeine, are easily obtainable to cybercriminals,” the scientists claimed.
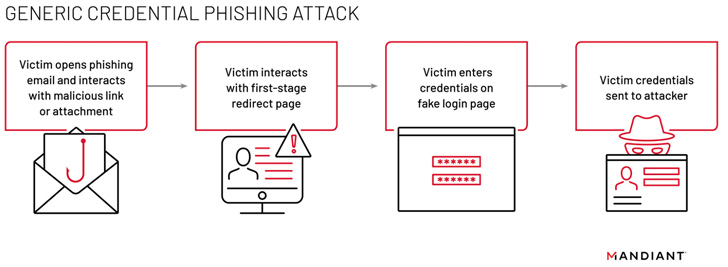
PhaaS services normally entail an operator to build and deploy a significant chunk of the phishing strategies, right from bogus sign-in pages, site hosting, web-site templates, and credential theft.
The evolution of email-dependent phishing threats into a support-based financial system implies that adversaries who intention to perform phishing attacks can now basically order this kind of means and infrastructure with no having to perform on it them selves. Caffeine is no exception.

It involves buyers to generate an account, and acquire a membership that expenditures $250 a month (Simple), $450 for a few months (Skilled), or $850 for a six-thirty day period license (Company) to avail its extensive selection of solutions, such as the campaign management dashboard and the applications to configure the attacks.
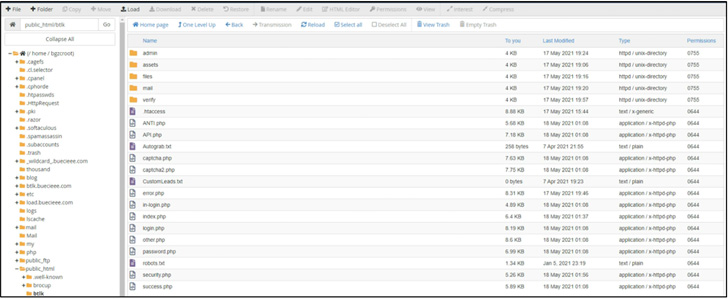
The greatest purpose of the phishing campaign is to facilitate the theft of Microsoft 365 credentials via rogue signal-in internet pages hosted on respectable WordPress sites, indicating that the Caffeine actors are leveraging compromised admin accounts, misconfigured sites, or flaws in web infrastructure platforms to deploy the kits.
Whilst the login pages are currently constrained to Microsoft 365 credential harvesting lures, the Google-owned danger intelligence firm noted that extra login website page formats could be introduced in the foreseeable future as for every shopper demands.
“It is also significant to keep in mind that defensive actions from PhaaS attacks can be a video game of cat and mouse,” Mandiant said. “As quickly as risk actor infrastructure receives taken down, new infrastructure can be spun up.”
Located this posting exciting? Abide by THN on Facebook, Twitter and LinkedIn to read through far more unique information we article.
Some pieces of this posting are sourced from:
thehackernews.com

 The best TeamViewer alternatives
The best TeamViewer alternatives