4 unique destructive frameworks created to attack air-gapped networks were being detected in the initial 50 % of 2020 by yourself, bringing the overall variety of this kind of toolkits to 17 and supplying adversaries a pathway to cyber espionage and exfiltrate categorized info.
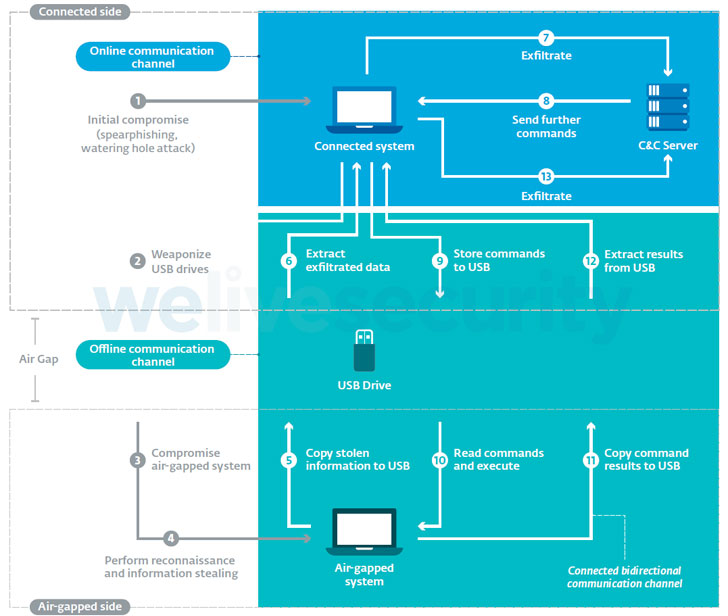
“All frameworks are designed to execute some variety of espionage, [and] all the frameworks made use of USB drives as the actual physical transmission medium to transfer data in and out of the specific air-gapped networks,” ESET researchers Alexis Dorais-Joncas and Facundo Muñoz stated in a comprehensive examine of the frameworks.
Air-gapping is a network security measure created to prevent unauthorized obtain to units by physically isolating them from other unsecured networks, including local space networks and the community internet. This also implies that the only way to transfer facts is by connecting a physical product to it, this kind of as USB drives or external really hard disks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Presented that the mechanism is just one of the most popular means SCADA and industrial manage techniques (ICS) are shielded, APT teams that are normally sponsored or component of nation-state initiatives have progressively set their sights on the critical infrastructure in hopes of infiltrating an air-gapped network with malware so as to surveil targets of fascination.
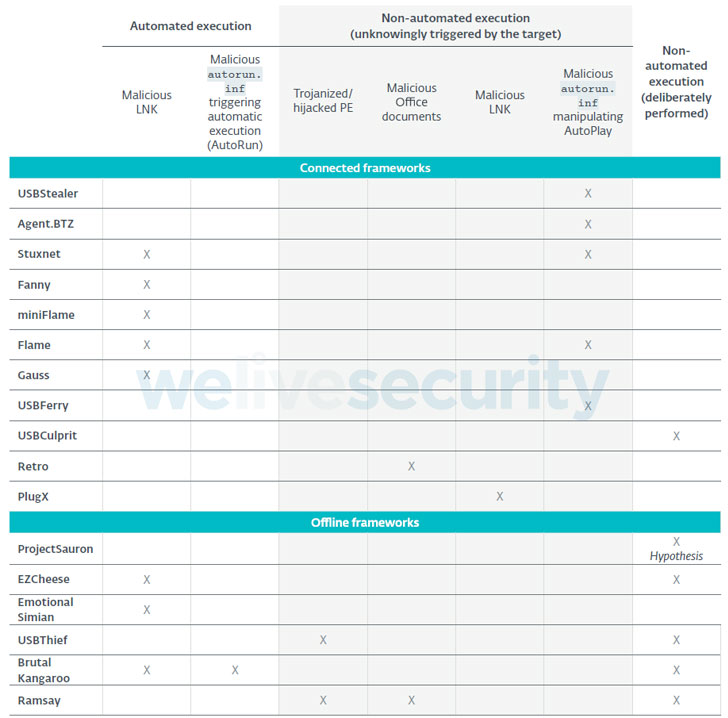
Mostly crafted to attack Windows-based working methods, the Slovak cybersecurity company mentioned that no much less than 75% of all the frameworks had been observed leveraging destructive LNK or AutoRun information on USB drives to both have out the first compromise of the air-gapped system or to shift laterally inside the air-gapped network.
Some frameworks that have been attributed to properly-recognized danger actors are as follows —
- Retro (DarkHotel aka APT-C-06 or Dubnium)
- Ramsay (DarkHotel)
- USBStealer (APT28 aka Sednit, Sofacy, or Extravagant Bear)
- USBFerry (Tropic Trooper aka APT23 or Pirate Panda)
- Fanny (Equation Group)
- USBCulprit (Goblin Panda aka Hellsing or Cycldek)
- PlugX (Mustang Panda), and
- Agent.BTZ (Turla Group)
“All frameworks have devised their have techniques, but they all have 1 thing in typical: with no exception, they all used weaponized USB drives,” the scientists defined. “The primary variance among related and offline frameworks is how the generate is weaponized in the to start with place.”

When related frameworks get the job done by deploying a malicious part on the related technique that displays the insertion of new USB drives and routinely spots the attack code desired to compromise the air-gapped system, offline frameworks like Brutal Kangaroo, EZCheese, and ProjectSauron rely on the attackers intentionally infecting their personal USB drives to backdoor the focused machine.
As safeguards, businesses with critical facts programs and sensitive details are encouraged to avert immediate email accessibility on related techniques, disable USB ports and sanitize USB drives, limit file execution on detachable drives, and carry out periodic investigation of air-gapped programs for any indications of suspicious exercise.
“Sustaining a totally air gapped method comes with the benefits of further safety,” Dorais-Joncas reported. “But just like all other security mechanisms, air gapping is not a silver bullet and does not prevent destructive actors from preying on outdated programs or lousy employee behavior.”
Observed this report interesting? Stick to THN on Fb, Twitter and LinkedIn to go through extra special content we submit.
Some components of this posting are sourced from:
thehackernews.com


 Police Arrest 1800 in Major Money Laundering Crackdown
Police Arrest 1800 in Major Money Laundering Crackdown