Editor’s Observe: This established of reviews originally appeared in June 2020. To locate out extra about SC Labs, get in touch with Adrian Sanabria at [email protected]
This month, SC Labs assessed numerous identification and entry management answers. This critique will come at a appropriate time with the modern gatherings bordering COVID-19 and the world wide change to functioning from property. The common, regarded perimeter has grown significantly immaterial above the yrs. The unprecedented, entire world-broad scramble to do the job remotely has emphasized that the beforehand identified perimeter is just about non-existent.
These attempting situations have mercilessly highlighted a selection of cybersecurity weaknesses throughout industries. It is our sincere hope that these critiques locate our readers in a state of proactive owing diligence in its place of a post-incident scramble subsequent a lesson figured out the difficult way. The identity and obtain management answers reviewed in this article guard the proverbial gates of critical corporation assets, examining the IDs of everyone that attempts to enter, making sure identities match conclude-user claims and privileged accessibility is sufficient for entry. Devoid of this cybersecurity bouncer to guard the doorway to your resources, destructive actors have a no cost pass into critical apps and info.
Product or service Group Opener

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
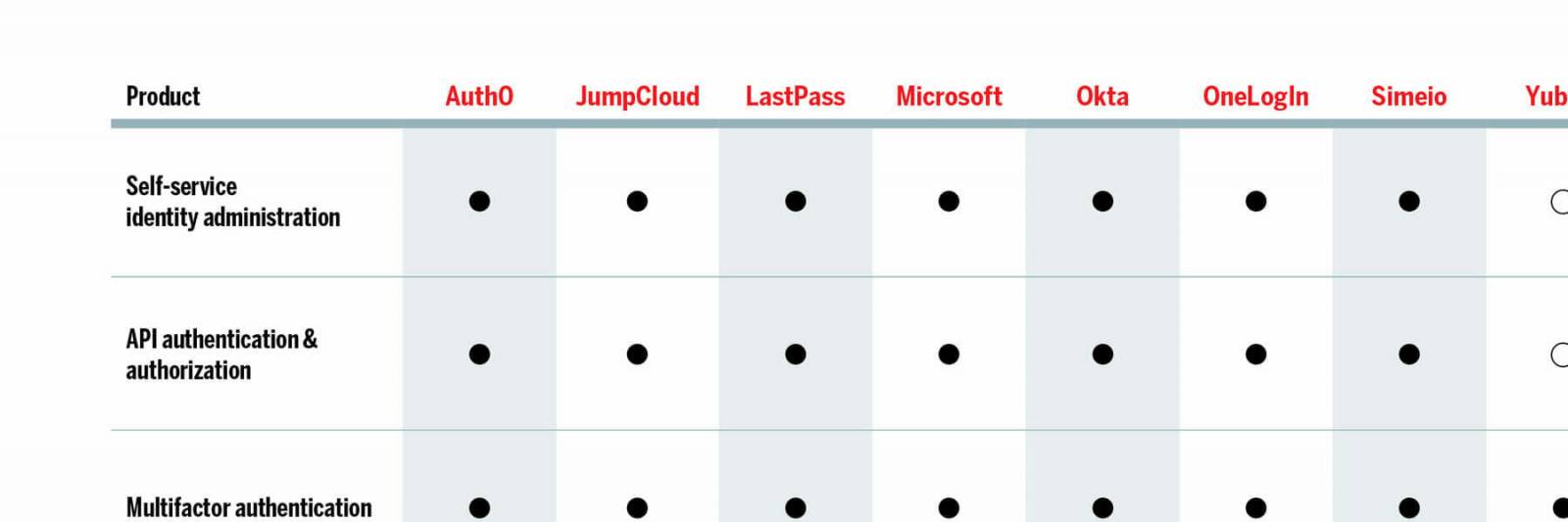
This thirty day period, SC Labs seemed at a handful of items inside the identity and entry management (IAM) area, which collectively perform as an organization gateway in between end-buyers and critical business info with centralized obtain management of cloud, on-premises and legacy programs and sources. The emphasis listed here is on the term collectively. Whilst these answers nearly exclusively provide core capabilities this sort of as authentication and authorization, the products and solutions we assessed are most powerful when deployed alongside at the very least a single other IAM solution. Numerous of these items now have constructed-in integration to assist a single a different.
Onboarding customers on to the platform, in most circumstances, is automatic with a broad range of directory integrations. Bisynchronous relationships concerning the identity system and supported directories normally takes the handbook function almost solely out of the arms of directors and drastically cuts down the complexity of implementation and time-to-benefit.
Some of this month’s items may run on the frontend with MSSP features even though a paired id and entry management remedy operates in the backend. This certain use scenario and style of deployment permits a seamless swap between IAM alternatives without the need of the have to have to retrain conclusion-end users. A third form of products, YubiKey (hardware), can incorporate an additional layer of identity security working as a crucial to the backend id and obtain administration lock.
We see the industrywide development of incorporating synthetic intelligence and machine mastering with identity options as nicely. State-of-the-art options this kind of as person conduct investigation allow dynamic assessments of, and responses to, various risk at the person or session level. A baseline comprehension of envisioned user conduct (time of day, IP deal with, locale, and so on.) enables the flagging of anomalous behavior.
Identification and entry administration items boost regular login credentials with numerous security capabilities including password administration and analysis, single indication-on and multifactor authentication. Some of the remedies have password vaults so that end users may securely retailer organization credentials. Password management retains tabs on the frequency with which passwords are reused and the inherent security of those passwords in accordance to length and complexity. One signal-on streamlines application and source access serving as a central, unified login portal. This encourages end customers to use extended and elaborate passwords since only have to have to signal in the moment to obtain all an organization’s sources in its place of acquiring to log into just about every solitary person useful resource. Some products even allow authentication at the workstation amount.
Id and access management goods are critical to enterprise security across industries and considerably boost current security investments. In addition to bringing in an further layer of security and going a action farther with info decline avoidance, their abilities and characteristics can boost efficiency and in general return on investment decision.
Choose of the Litter
Yubico YubiKey 5Ci delivers the easiest and maximum amount of security readily available for an identification solution that is so client pleasant. If there had been an simplicity-of-use classification, this would gain by a mile. The a single-contact YubiKey encounter comes with a significant ecosystem of integrations, a small whole expense of possession, and a substantial return on expenditure, building Yubico YubiKey an SC Labs Most effective Obtain.
Okta Identity Cloud is a flexible option with an considerable integration network that handles each identification use case for any technology. Okta reliably and proficiently improves productivity and security, driving profitability and development to optimize in general return on financial investment and to decrease the full expense of ownership, making this our SC Labs Suggested item for this month’s round of testing.
June testimonials
Auth0
JumpCloud
LogMeIn LastPass Id
Microsoft Azure Active Directory (Azure Advert)
Okta Identification Cloud
OneLogIn Trusted Practical experience Platform (TEP)
Simeio Identification Orchestrator
Yubico YubiKey 5Ci
Click on the connection below for the total-dimensions variation: https://www.scmagazine.com/wp-information/uploads/web-sites/2/2021/02/MATRIX-0620-scaled.jpg
Some parts of this article are sourced from:
www.scmagazine.com

 Rapid7 Expands Cloud Security Portfolio with Acquisition of Alcide
Rapid7 Expands Cloud Security Portfolio with Acquisition of Alcide