Researchers have demonstrated a novel course of attacks that could permit a poor actor to perhaps circumvent present countermeasures and crack the integrity defense of digitally signed PDF documents.
Called “Shadow attacks” by academics from Ruhr-University Bochum, the system employs the “massive flexibility provided by the PDF specification so that shadow files keep on being typical-compliant.”
The results were presented yesterday at the Network and Dispersed Procedure Security Symposium (NDSS), with 16 of the 29 PDF viewers examined — which includes Adobe Acrobat, Foxit Reader, Perfect PDF, and Okular — identified susceptible to shadow attacks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
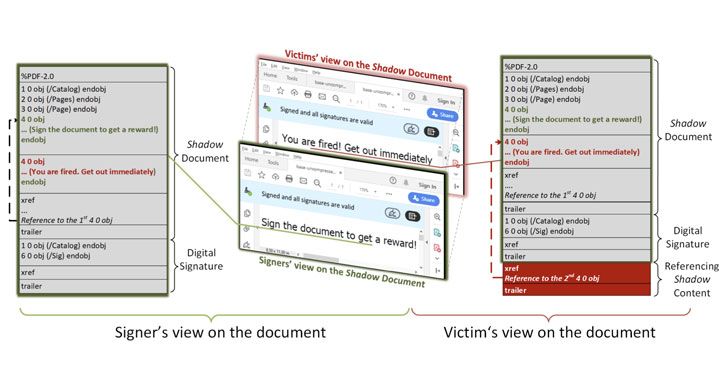
To have out the attack, a destructive actor produces a PDF doc with two different contents: one particular which is the content material that is envisioned by the party signing the doc, and the other, a piece of concealed content material that gets displayed at the time the PDF is signed.
“The signers of the PDF get the doc, critique it, and indication it,” the scientists outlined. “The attackers use the signed doc, modify it a little bit, and deliver it to the victims. Immediately after opening the signed PDF, the victims test whether the electronic signature was effectively confirmed. On the other hand, the victims see distinct articles than the signers.”

In the analog earth, the attack is equivalent to intentionally leaving vacant areas in a paper document and receiving it signed by the concerned party, ultimately allowing the counterparty to insert arbitrary written content in the spaces.
Shadow attacks build on a related risk devised by the researchers in February 2019, which uncovered that it was feasible to alter an present signed document with no invalidating its signature, thereby producing it achievable to forge a PDF document.

Whilst suppliers have due to the fact applied security steps to take care of the issue, the new review aims to prolong this attack product to determine the likelihood that an adversary can modify the visible written content of a digitally signed PDF without having invalidating its signature, assuming that they can manipulate the PDF prior to it really is signed.
At its main, the attacks leverage “harmless” PDF characteristics which do not invalidate the signature, this sort of as “incremental update” that permits for making improvements to a PDF (e.g., filling out a variety) and “interactive forms” (e.g., text fields, radio buttons, and so on.) to conceal the malicious material behind seemingly innocuous overlay objects or directly replace the initial content immediately after it really is signed.
A 3rd variant identified as “cover and switch” can be made use of to merge the aforementioned solutions and modify the contents of an complete document by only transforming the item references in the PDF.
“The attacker can construct a total shadow document influencing the presentation of each and every web page, or even the whole quantity of web pages, as very well as every item contained therein,” the researchers claimed.
Place just, the thought is to make a variety, which demonstrates the similar benefit before and just after signing, but a totally unique established of values publish an attacker’s manipulation.
To take a look at the attacks, the researchers have published two new open up-source resources termed PDF-Attacker and PDF-Detector that can be made use of to generate shadow documents and examination a PDF for manipulation prior to it’s signed and after it really is been altered.

The flaws — tracked as CVE-2020-9592 and CVE-2020-9596 — have been given that addressed by Adobe in an update unveiled on Could 12, 2020. As of December 17, 2020, 11 of the 29 tested PDF purposes keep on being unpatched.
This is not the to start with time PDF security has appear less than the lens. The scientists have previously demonstrated approaches to extract contents of a password-guarded PDF file by taking edge of partial encryption supported natively by the PDF specification to remotely exfiltrate content material after a person opens that document.
Separately, the scientists very last thirty day period uncovered a different set of 11 vulnerabilities impacting the PDF conventional (CVE-2020-28352 through CVE-2020-28359, and from CVE-2020-28410 to CVE-2020-28412) that could lead to denial-of-service, information disclosure, details manipulation attacks, and even arbitrary code execution.
Found this post interesting? Stick to THN on Fb, Twitter and LinkedIn to examine more distinctive written content we put up.
Some areas of this short article are sourced from:
thehackernews.com

 Most Firms Now Fear Nation State Attack
Most Firms Now Fear Nation State Attack