Shutterstock
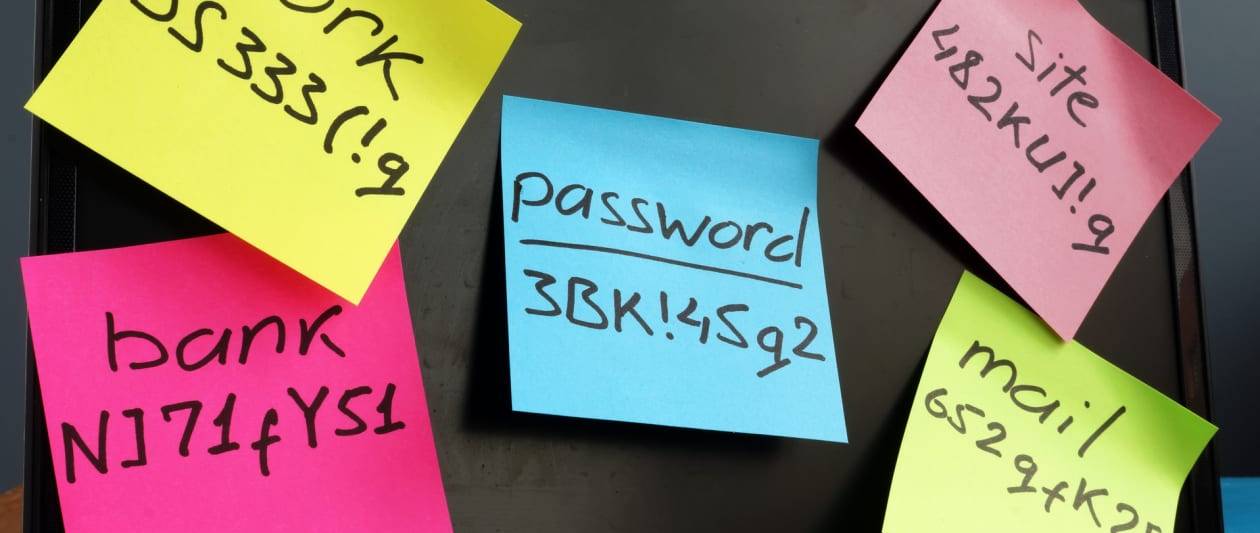
I’m about to so do a little something I’m certain will not shock regular viewers: decide on an argument with the powers that be. The organisation in question, getting the National Cyber Security Centre (NCSC) which, by and large, does a splendid work in each public and private sectors in matters of security assistance and support. By and substantial, but not on a person situation lately when it made a decision the time was proper to remind us of some password design information it 1st presented 5 many years in the past. It was wrong then and remains so to this working day.
Employing the correctly realistic hashtag of #thinkrandom, that tips was to use a few random words and phrases as your password. That’s 3 phrases, not four, so you can forget about about the XKCD comic recommendation of “correct, horse, battery, staple” that is wedged itself into cyber security folklore. Not that you should really use it anyway, as password reuse is of course verboten if you want to sustain any semblance of a sturdy security posture.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Whilst admitting the use of 3 random phrases is “not a password panacea”, the latest NCSC publishing serves to press residence the message that it’s greater than working with standard password complexity information, due to the fact the latter relies on us memorising a lot of very long and complex strings. Working with 3 random text, we are suggested, generates passwords that are “strong more than enough for lots of purposes”, and helps get all over the reuse trouble that it states common complicated passwords generates.
Random obtain reminiscences
Let us offer with the past of these 1st: password reuse. There is definitely no bloody change among attempting to bear in mind 97 exceptional complex and random password strings and undertaking so with 97 3 random word passphrases. You will fail except if you are a memory savant. That is a fact. It is a simple fact because as humans we are only not wired to don’t forget random matters.
This provides me to the second dilemma I have with the suggestions: the reality of randomness. Most folks, most of the time, will pick a few words that are much from random when constructing a full bunch of passphrases. What folks will do is, totally subconsciously, undertake patterns in the phrases they appear up with. Styles in both of those the connections amongst the phrases utilised to make remember less difficult and designs in between the passphrases by themselves to make numerous kinds much easier to remember.
People just do not do randomness nicely which is why there are computer-me-bobs for creating really random things, and much more on that afterwards. There is a seriously intriguing piece of study from the University of Cambridge Pc Laboratory, admittedly now just about a decade old but even now relevant, that points out this really well. Its evidence on multi-word passphrases was fairly damning: “By our metrics, even five-phrase phrases would be really insecure towards offline attacks,” the researchers discovered, since people today obviously sway toward speech fairly than randomness. “Phrases like young male which occur up normally in speech are proportionately much more probably to be preferred than exceptional phrases like younger table” the exploration concluded. Which is just what I would be expecting.
There is an app for that
Appear, I beautifully comprehend plenty of security industry experts disagree with me below. Their argument frequently being together the same traces as the NCSC, that adopting a a few random phrases method will produce more powerful passwords than those we usually see becoming employed and reused these days. This is genuine, and I’m not suggesting that Password, or P@ssw0rd, or even P@ssw0rd1 is a super-duper credential to be making use of. What I am suggesting is that, fairly than acquiring people to use 3 supposedly random words and phrases, it would be considerably better to recommend them to use some sort of protected password supervisor instead.
Skip the total 3 phrases point, really do not mention it at all, go straight for the “use a password supervisor dammit” jugular. That way you can create actually random and complicated and incredibly extended passwords, or the software can, and have a unique a single for each login.
Of program, the perennial issue of grasp password development rears its really unattractive head after additional. Instead than go over old floor involving muscle mass memory, encrypted USB sticks (which want nevertheless yet another password) or a biometric system (JEMpass) and even dice with many designs rolled randomly into a locked box (DiceKeys), let’s strategy this from the 3 random phrases angle. Or, instead, let us not. Just three text, no subject how random, would make a spectacularly inadequate master password if you question me. Instead, go for 5 or six, or far more if your memory will allow for.
These would, of system, want to be random alternatively than your concept of random. Which is wherever one particular password manager, in fact 1Password, arrives in. Did you see what I did there? Anyway, it has a password generator that anyone can use – which has the option of making a passphrase employing random text. Just decide on the “memorable password” dropdown, established the number of phrases to a thing you are at ease with, and you’re away. Other expert services, of training course, are also obtainable, these as Kaspersky’s very own password generator.
As I say, do not go for anything too small as this is the critical that unlocks all your other passwords. I’d also stay clear of unchecking the “full words” box as this produces gibberish words that aren’t definitely less difficult than a extended password to memorise. Practise typing the final result over and above to get that muscle memory working, and if you are a 1Password consumer, be absolutely sure to conserve the “emergency kit” that can be printed out and stored somewhere secure. The actuality is that for 99% of use circumstances a risk actor is not likely to ransack your house searching for a grasp password, nor your business office for that matter. If you do tumble into the 1% then the odds are large that you’ll previously be working with some sort of security protocol that would make the overall 3 random terms argument moot in any case.
Talking of passwords in the office, I can not wrap up this dialogue devoid of mentioning some additional investigate, this time from Outside of Identity. This discovered that not only did almost a quarter of staff questioned nevertheless have obtain to accounts from a preceding career, but 41% admitted to sharing passwords in the place of work, and 20% used the exact passwords at residence as they did for perform-similar accounts. Just in circumstance you puzzled why I bang on about the worth of password cleanliness, month right after month.
Some sections of this short article are sourced from:
www.itpro.co.uk

 Microsoft Issues Windows Update to Patch 0-Day Used to Spread Emotet Malware
Microsoft Issues Windows Update to Patch 0-Day Used to Spread Emotet Malware