Cybersecurity researchers these days disclosed a new supply-chain attack focusing on the Vietnam Government Certification Authority (VGCA) that compromised the agency’s electronic signature toolkit to put in a backdoor on target methods.
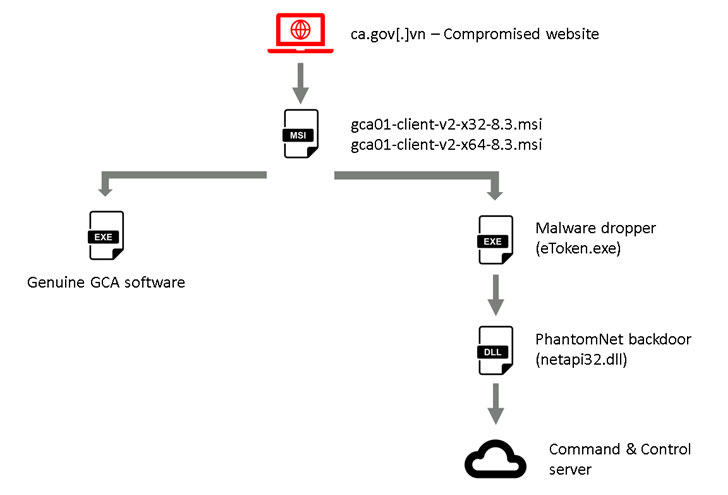
Uncovered by Slovak internet security organization ESET early this month, the “SignSight” attack included modifying software program installers hosted on the CA’s web-site (“ca.gov.vn”) to insert a spy ware resource identified as PhantomNet or Smanager.
According to ESET’s telemetry, the breach happened from at the very least July 23 to August 16, 2020, with the two installers in problem — “gca01-consumer-v2-x32-8.3.msi” and “gca01-customer-v2-x64-8.3.msi” for 32-bit and 64-little bit Windows devices — tampered to involve the backdoor.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Immediately after the attack was noted to VGCA, the certificate authority verified that “they have been knowledgeable of the attack prior to our notification and that they notified the customers who downloaded the trojanized application.”
“The compromise of a certification authority web-site is a great opportunity for APT groups, given that website visitors are probably to have a significant degree of trust in a point out firm responsible for electronic signatures,” ESET’s Matthieu Faou explained.
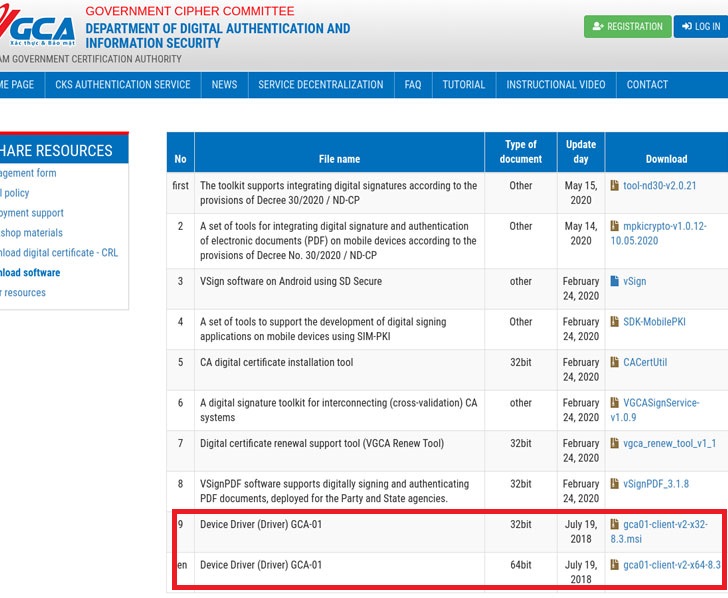
The electronic signature device, mandated by Vietnam’s Government Cipher Committee as aspect of an electronic authentication scheme, is used by the federal government sector as perfectly as private providers to digitally signal files making use of a USB token (also known as a PKI token) that suppliers the electronic signature and necessitates the aforementioned driver to work.
As a consequence, the only way a user can get contaminated is when the compromised application hosted on the formal site is manually downloaded and executed on the concentrate on process.
As soon as mounted, the modified software begins the real GCA system to mask the breach and then operates the PhantomNet backdoor that masquerades as a seemingly harmless file named “eToken.exe.”
The backdoor — compiled most not too long ago on April 26 — can take the responsibility of collecting procedure facts, with supplemental destructive capabilities deployed as a result of plugins retrieved from hardcoded command-and-manage servers (e.g. “vgca.homeunix[.]org” and “office environment365.blogdns[.]com”) that mimic the names of VGCA and common efficiency software program.
ESET claimed in addition to Vietnam, it noticed victims in the Philippines, but their shipping and delivery system continues to be unfamiliar. The top target of the attackers remains unclear as perfectly, what with minor to no facts about the submit-compromise exercise.
If anything, the incident highlights why supply-chain attacks are significantly getting a widespread attack vector amid cyberespionage groups, as it lets the adversaries to deploy malware on quite a few desktops at the identical time covertly.
In November, ESET disclosed a Lazarus campaign in South Korea that made use of respectable security application and stolen electronic certificates to distribute distant administration instruments (RATs) on concentrate on techniques.
Then final 7 days, it also observed that a chat software package referred to as Equipped Desktop, employed by 430 government companies in Mongolia, was abused to provide the HyperBro backdoor, the Korplug RAT, and a different Trojan called Tmanger.
And finally, a provide-chain attack on SolarWinds Orion software uncovered this 7 days was exploited to breach various important US authorities businesses, including the Departments of Homeland Security, Commerce, Treasury, and State.
“Source-chain attacks are normally really hard to locate, as the destructive code is usually concealed among the a whole lot of respectable code, generating its discovery drastically a lot more complicated,” Faou concluded.
Observed this short article appealing? Follow THN on Facebook, Twitter and LinkedIn to go through far more exceptional content we write-up.
Some elements of this write-up are sourced from:
thehackernews.com

 BEC Hits Double Digits as COVID-19 Scams Abound
BEC Hits Double Digits as COVID-19 Scams Abound