Former associates of the Conti cybercrime cartel have been implicated in five distinctive campaigns concentrating on Ukraine from April to August 2022.
The results, which occur from Google’s Threat Investigation Group (TAG), builds upon a prior report revealed in July 2022, detailing the continued cyber action aimed at the Eastern European nation amid the ongoing Russo-Ukrainian war.
“UAC-0098 is a risk actor that historically sent the IcedID banking trojan, leading to human-operated ransomware attacks,” TAG researcher Pierre-Marc Bureau said in a report shared with The Hacker News.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The attacker has recently shifted their target to targeting Ukrainian organizations, the Ukrainian federal government, and European humanitarian and non-gain corporations.”
UAC-0098 is considered to have functioned as an preliminary entry broker for ransomware groups these types of as Quantum and Conti (aka FIN12, Gold Ulrick, or Wizard Spiker), the former of which was subsumed by Conti in April 2022.
A single of the prominent strategies undertaken by the group in June 2022 entailed the abuse of Follina vulnerability (CVE-2022-30190) in the Windows working process to deploy CrescentImp and Cobalt Strike Beacons on to focused hosts in media and critical infrastructure entities.
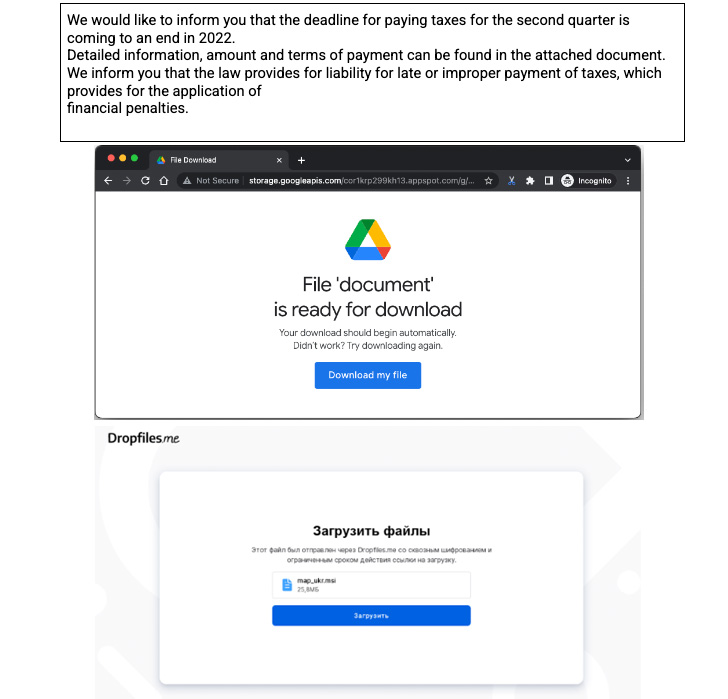
But this seems to be a part of a collection of attacks that commenced way back in late April 2022, when the team carried out an email phishing marketing campaign to produce AnchorMail (aka LackeyBuilder), a variant of the TrickBot group’s AnchorDNS implant that makes use of SMTP for command-and-command.
Subsequent phishing strategies distributing IcedID and Cobalt Strike have been directed towards Ukrainian businesses, regularly striking the hospitality sector, some of which impersonated the National Cyber Police of Ukraine or associates of Elon Musk and StarLink.
All-around mid-May perhaps, UAC-0098 is also explained to have leveraged a compromised account of a hotel in India to send out malware-laced attachments to organizations doing work in the hospitality business in Ukraine, before expanding to humanitarian NGOs in Italy.

Similar attacks have also been noticed against entities in the technology, retail and government sectors, with the IcedID binary hid as a Microsoft update to bring about the infection. Post-exploitation measures carried out pursuing a profitable compromise have not been discovered.
UAC-0098 is much from the only Conti-affiliated hacking team to set its sights on Ukraine given that the onset of the war. In July 2022, IBM Security X-Drive disclosed that the TrickBot gang orchestrated 6 distinct campaigns to systematically target the country with a plethora of malware.
“UAC-0098 activities are consultant illustrations of blurring traces among fiscally inspired and governing administration backed groups in Jap Europe, illustrating a craze of threat actors transforming their targeting to align with regional geopolitical pursuits,” Bureau stated.
“The team demonstrates sturdy fascination in breaching enterprises operating in the hospitality market of Ukraine, heading as much as launching several distinct strategies against the similar lodge chains.”
Observed this posting attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to read far more exclusive material we submit.
Some components of this posting are sourced from:
thehackernews.com

 Authorities Shut Down WT1SHOP Site for Selling Stolen Credentials and Credit Cards
Authorities Shut Down WT1SHOP Site for Selling Stolen Credentials and Credit Cards