An ongoing campaign has been observed to leverage a network of internet sites performing as a “dropper as a company” to provide a bundle of malware payloads to victims seeking for “cracked” versions of common organization and buyer apps.
“These malware integrated an assortment of click on fraud bots, other details stealers, and even ransomware,” scientists from cybersecurity firm Sophos stated in a report posted past week.
The attacks function by having benefit of a variety of bait internet pages hosted on WordPress that contain “obtain” back links to software deals, which, when clicked, redirect the victims to a different web site that delivers potentially undesired browser plug-ins and malware, these types of as installers for Raccoon Stealer, Quit ransomware, the Glupteba backdoor, and a range of destructive cryptocurrency miners that masquerade as antivirus solutions.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Visitors who arrive on these internet sites are prompted to permit notifications If they enable this to come about, the web-sites repeatedly issue bogus malware alerts,” the researchers reported. “If the end users click on the alerts, they are directed by way of a series of internet websites until finally they get there at a place that’s decided by the visitor’s running technique, browser kind, and geographic spot.”
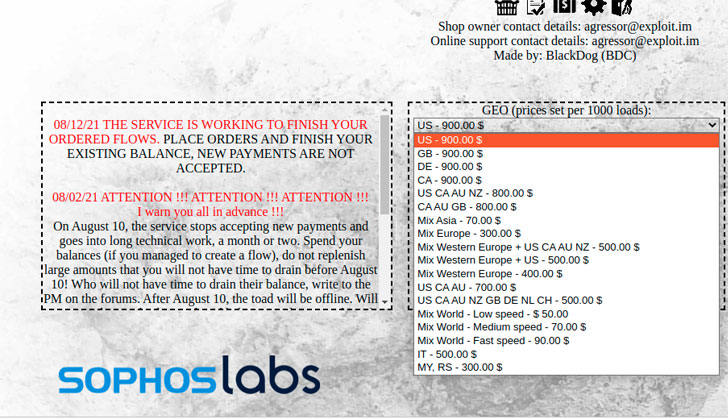
Working with tactics like look for engine optimization, inbound links to the web-sites show up at the best of search effects when persons look for for pirated variations of a wide assortment of application applications. The actions, regarded as to be the products of an underground market for paid obtain companies, enables entry-stage cyber actors to set up and tailor their campaigns primarily based on geographical focusing on.
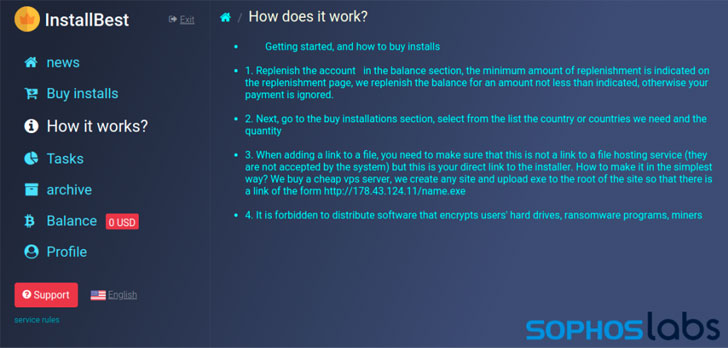
Traffic exchanges, as the distribution infrastructure is also known as, normally demand a Bitcoin payment ahead of affiliate marketers can develop accounts on the support and commence distributing installers, with web sites like InstallBest supplying assistance on “ideal tactics,” this sort of as recommending from working with Cloudflare-based mostly hosts for downloaders, as nicely as working with URLs in just Discord’s CDN, Bitbucket, or other cloud platforms.
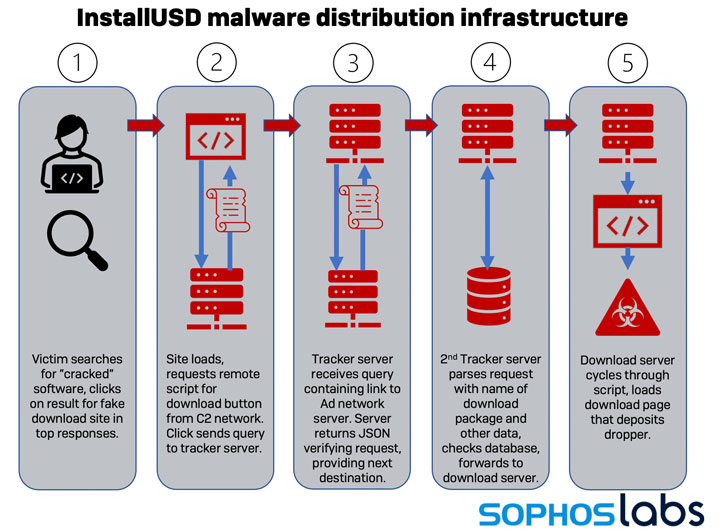
On top of that, the scientists also uncovered some of the providers that act as “go-betweens” to recognized malvertising networks that pay back internet site publishers for visitors. One this sort of founded site visitors supplier is InstallUSD, a Pakistan-primarily based advertising and marketing network, which has been joined to a selection of malware campaigns involving the cracked computer software web-sites.
This is significantly from the to start with time “warez” internet sites have been set to use as an infection vector by risk actors. Previously this June, a cryptocurrency miner known as Crackonosh was located abusing the process to install a coin miner bundle named XMRig for stealthily exploiting the infected host’s resources to mine Monero.
A thirty day period later, the attackers driving a piece of malware dubbed MosaicLoader ended up discovered targeting men and women looking for cracked computer software as section of a worldwide campaign to deploy a totally-showcased backdoor capable of roping the compromised Windows programs into a botnet.
Discovered this article interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read through much more unique written content we article.
Some components of this posting are sourced from:
thehackernews.com

 Critical Auth Bypass Bug Affect NETGEAR Smart Switches — Patch and PoC Released
Critical Auth Bypass Bug Affect NETGEAR Smart Switches — Patch and PoC Released