A team of researchers these days unveils two critical security vulnerabilities it uncovered in Dell Wyse Slim purchasers that could have most likely permitted attackers to remotely execute malicious code and obtain arbitrary information on impacted products.
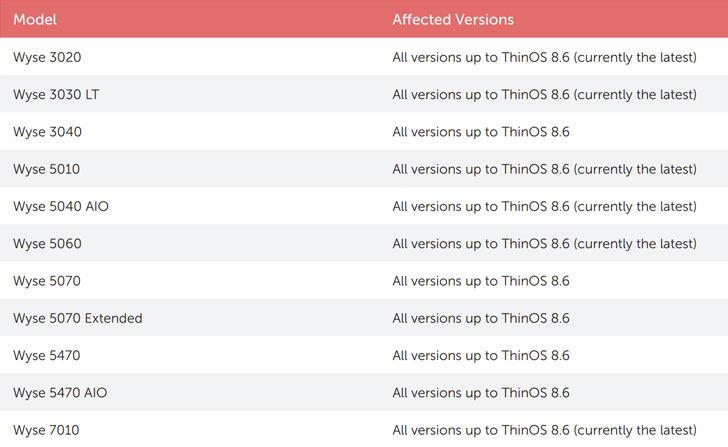
The flaws, which have been uncovered by health care cybersecurity service provider CyberMDX and noted to Dell in June 2020, has an effect on all equipment running ThinOS variations 8.6 and below.
Dell has tackled equally the vulnerabilities in an update launched these days. The flaws also have a CVSS score of 10 out of 10, making them critical in severity.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Slender clientele are ordinarily desktops that operate from resources stored on a central server alternatively of a localized challenging generate. They perform by setting up a distant link to the server, which requires care of launching and running purposes and storing relevant details.
Tracked as CVE-2020-29491 and CVE-2020-29492, the security shortcomings in Wyse’s slim purchasers stem from the point that the FTP sessions utilised to pull firmware updates and configurations from a local server are unprotected sans any authentication (“anonymous”), consequently earning it achievable for an attacker in the exact network to read through and alter their configurations.
The to start with flaw, CVE-2020-29491, allows the consumer to obtain the server and go through configurations (.ini files) belonging to other purchasers.
A 2nd consequence of getting no FTP credentials is that any individual on the network can accessibility the FTP server and specifically alter the .ini information holding the configuration for other slender customer gadgets (CVE-2020-29492).
Most devastatingly, the configuration may well contain delicate knowledge, which includes possible passwords and account details that could be utilized to compromise the gadget.
Specified the relative ease of exploitation of these flaws, it can be recommended that the patches are used as quickly as probable to remediate the risk.
CyberMDX also suggests updating compatible purchasers to ThinOS 9, which removes the INI file administration function. In the party an up grade is not feasible, it really is suggested to disable the use of FTP for fetching the vulnerable data files and alternatively rely on an HTTPS server or Wyse Management Suite.
“Reading or altering people parameters [in the .ini files] opens the door to a wide variety of attack situations,” CyberMDX scientists reported. “Configuring and enabling VNC for total remote management, leaking remote desktop credentials, and manipulating DNS success are some of the scenarios to be informed of.”
Identified this posting attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to read far more distinctive articles we article.
Some components of this posting are sourced from:
thehackernews.com


 Institute for Security and Technology launches multisector ransomware task force
Institute for Security and Technology launches multisector ransomware task force