Google has rolled out however yet another update to Chrome browser for Windows, Mac, and Linux to take care of four security vulnerabilities, including a person zero-day flaw that is getting exploited in the wild.
Tracked as CVE-2021-30554, the higher severity flaw fears a use immediately after cost-free vulnerability in WebGL (aka Web Graphics Library), a JavaScript API for rendering interactive 2D and 3D graphics in just the browser.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Profitable exploitation of the flaw could signify corruption of valid details, main to a crash, and even execution of unauthorized code or commands.
The issue was reported to Google anonymously on June 15, Chrome technological system manager Srinivas Sista noted, introducing the organization is “knowledgeable that an exploit for CVE-2021-30554 exists in the wild.”
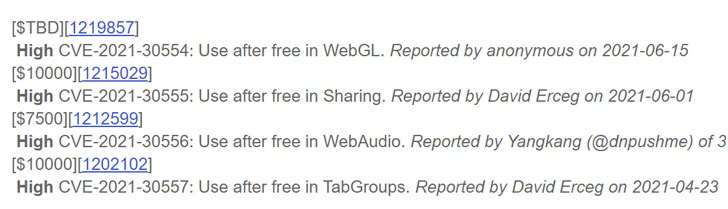
Even though it’s commonly the norm to limit information of the vulnerability until finally a the greater part of customers are up to date with the fix, the progress comes fewer than 10 times right after Google addressed a different zero-day vulnerability exploited in lively attacks (CVE-2021-30551).
CVE-2021-30554 is also the eighth zero-day flaw patched by Google considering the fact that the begin of the 12 months.

“I am delighted we are getting improved at detecting these exploits and the wonderful partnerships we have to get the vulnerabilities patched, but I continue to be anxious about how many are currently being learned on an ongoing basis and the position of professional vendors,” tweeted Shane Huntley, Director of Google’s Danger Examination Team, on June 8.
Chrome people are suggested to update to the most current variation (91..4472.114) by heading to Settings > Aid > ‘About Google Chrome’ to mitigate the risk linked with the flaw.
Observed this write-up interesting? Adhere to THN on Facebook, Twitter and LinkedIn to go through far more special material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Carnival discloses new data breach on email accounts
Carnival discloses new data breach on email accounts![[ebook] 7 signs you might need a new detection and](https://thecybersecurity.news/data/2021/06/eBook-7-Signs-You-Might-Need-a-New-Detection-and-80x80.jpg)