Apple on Thursday introduced many security updates to patch a few zero-working day vulnerabilities that had been exposed as staying actively exploited in the wild.
Rolled out as section of its iOS, iPadOS, macOS, and watchOS updates, the flaws reside in the FontParser ingredient and the kernel, making it possible for adversaries to remotely execute arbitrary code and operate destructive packages with kernel-level privileges.
The zero-times were being identified and described to Apple by Google’s Undertaking Zero security group.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Apple is aware of reports that an exploit for this issue exists in the wild,” the iPhone maker reported of the 3 zero-days without having giving any further details so as to permit a large majority of users to install the updates.
The record of impacted products incorporates iPhone 6s and later, iPod contact 7th technology, iPad Air 2 and later, iPad mini four and afterwards, and Apple Check out Series 1 and later.
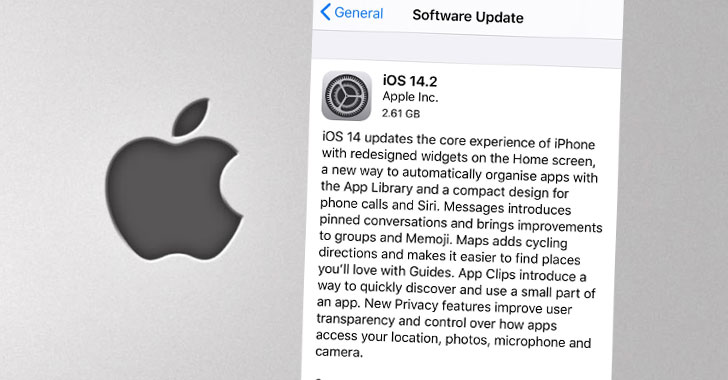
The fixes are offered in variations iOS 12.4.9 and 14.2, iPadOS 14.2, watchOS 5.3.9, 6.2.9, and 7.1, and as a supplemental update for macOS Catalina 10.15.7.
In accordance to Apple’s security bulletin, the flaws are:
- CVE-2020-27930: A memory corruption issue in the FontParser library that will allow for remote code execution when processing a maliciously crafted font.
- CVE-2020-27932: A memory initialization issue that lets a destructive software to execute arbitrary code with kernel privileges.
- CVE-2020-27950: A type-confusion issue that tends to make it possible for a destructive software to disclose kernel memory.
“Targeted exploitation in the wild similar to the other recently claimed 0days,” said Shane Huntley, Director of Google’s Threat Analysis Team. “Not connected to any election focusing on.”
The disclosure is the most current in the string of zero-times Project Zero has reported due to the fact October 20. Initial came the Chrome zero-working day in Freetype font rendering library (CVE-2020-15999), then a Windows zero-day (CVE-2020-17087), followed by two a lot more in Chrome and its Android variant (CVE-2020-16009 and CVE-2020-16010).
A patch for the Windows zero-working day is envisioned to be unveiled on November 10 as section of this month’s Patch Tuesday.
Whilst much more details are awaited on whether or not the zero-times ended up abused by the exact same danger actor, it’s suggested that buyers update their devices to the most recent variations to mitigate the risk associated with the flaws.
Observed this write-up appealing? Adhere to THN on Facebook, Twitter and LinkedIn to go through more unique written content we put up.
Some parts of this report are sourced from:
thehackernews.com

 Ransomware attack toys with Mattel systems, data
Ransomware attack toys with Mattel systems, data