Despite the fact that businesses usually go to wonderful lengths to tackle security vulnerabilities that may perhaps exist inside their IT infrastructure, an organization’s helpdesk could pose a even larger risk thanks to social engineering attacks.
Social engineering is “the artwork of manipulating folks so they give up confidential data,” in accordance to Webroot. There are lots of distinct styles of social engineering techniques but one is area of vulnerability is how social engineering could be made use of in opposition to a helpdesk technician to steal a user’s credentials.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Approach of Getting Access With Social Engineering
The 1st action in these types of an attack is ordinarily for the attacker to acquire facts about the organization that they are targeting. The attacker may well get started by working with facts that is freely offered on the Internet to figure out who inside of the business is most probable to have elevated permissions or accessibility to sensitive facts. An attacker can usually get this info by a simple Google lookup or by querying small business-oriented social networks these as LinkedIn.
When an attacker identifies a person whose qualifications they want to steal, they have to have to know the user’s login title. There are any variety of strategies that an attacker could figure out a login name. One particular system might only be to try out to authenticate into the organization’s Active Directory environment. Some older Active Listing consumers will inform you if you have entered a negative username or an incorrect password.
An a lot easier process is for the attacker to query on the internet databases of leaked credentials. The attacker isn’t going to always need to locate the credentials for the account that they are attacking. They need only to obtain qualifications for someone at that corporation. That will expose the username framework that the firm makes use of. For case in point, the group might develop usernames primarily based on firstname.lastname or possibly a initially preliminary followed by a final title.
With these information and facts in hand, the attacker could possibly make a phone connect with to the organization’s helpdesk and ask for a password reset. The intention at the rear of this phone simply call isn’t really to get the password reset, but somewhat to locate out what types of protocols the firm has in position. For instance, the helpdesk technician may inquire the attacker (who is posing as a respectable personnel) a security issue these kinds of as, “what is your employee ID quantity”. The attacker can then convey to the technician that they do not have their worker ID range handy and will simply call back later on when they have it in entrance of them.
At this point, the attacker has numerous very important items of information in their possession. They know the victim’s identify, the victim’s login title, and the security concern that the helpdesk technician is heading ask prior to granting a password reset.
Combatting Social Engineering Attack With Security Issues
Regrettably, security thoughts are mostly ineffective. An skilled attacker can quickly acquire the responses to security inquiries from any amount of distinct resources. The Dark Web for instance, includes full databases of answers to likely security thoughts and we know conclude-end users often disclose way too a lot individual data on social media.
In addition to security issues, some corporations have historically used caller ID details as a tool for verifying a user’s identification. Even so, this method is also unreliable simply because cloud-based mostly PBX devices make it straightforward for an attacker to spoof caller ID information.
The crucial thing to try to remember is that social engineering attacks are not theoretical attack vectors, they occur in the genuine globe. Previously this calendar year, Electronic Arts was infiltrated by hackers who stole a massive amount of facts (such as supply code for the firm’s FIFA 21 soccer game). The hacker attained access by tricking the company’s IT assist team into giving them access to the firm’s network.
So, if security questions and other conventional id verification mechanisms are no for a longer period successful, how can an organization protect by itself towards this type of attack?
Onus on the Helpdesk Technician
The essential to stopping social engineering attacks versus the helpdesk is to make it unachievable for a helpdesk technician to knowingly or unknowingly help in this sort of an attack. The technician is, for all simple applications, the weak backlink in the security chain.
Take into consideration the earlier illustration in which an attacker contacts an organization’s helpdesk pretending to be an personnel who wants their password reset. Quite a few issues could conceivably transpire all through that conversation. Some attainable outcomes involve:
- The attacker solutions the security question utilizing stollen data sourced from social media or from the Dark Web
- The attacker tries to obtain the technician’s rely on by way of friendly conversation to achieve favor with the technician. The attacker hopes that the technician will forget the rules and go ahead and reset the password, even in the absence of the expected security information. In some cases, the attacker may also check out to make the helpdesk technician feel sorry for them.
- The attacker could possibly test to intimidate the helpdesk technician by posing as a CEO who is exceptionally upset that they are unable to log in. When the helpdesk technician asks a security query, the attacker could possibly scream that they do not have time to remedy a bunch of silly inquiries, and need that the password be reset right now (this technique has succeeded several instances in the true planet).
In the end, the technician’s discretion is the only point that establishes whether or not the asked for password reset is heading to transpire. There is absolutely nothing in the indigenous Energetic Directory applications that will prevent a technician from being ready to reset a user’s password if the technician fails to demonstrate the user’s identification sufficiently. As these, the Energetic Directory applications can be imagined of as a different weak connection in the security chain.
The Protected Solution to Socially Engineered Cyber Attack
The ideal way to remove the possibility that the firm will be breached by these forms of attacks is to reduce the helpdesk staff members from employing the Energetic Directory Users and Pcs console or equivalent instruments for password resets. Instead, it is superior to use a third-party answer these kinds of as Specops Secure Support Desk, that will bodily avoid a technician from resetting a password until particular MFA needs have been satisfied.
To see how the Protected Assistance Desk gets rid of the dangers linked with password resets, take into account a problem in which a genuine user requests a password reset. The helpdesk technician can send a six-digit code to the user’s cellular device (which has been preregistered and is regarded to belong to the person). The technician simply cannot see this code and does not know what code was sent. When the person gets the code, they ought to study it to the technician, who then enters the code into the Specops application.
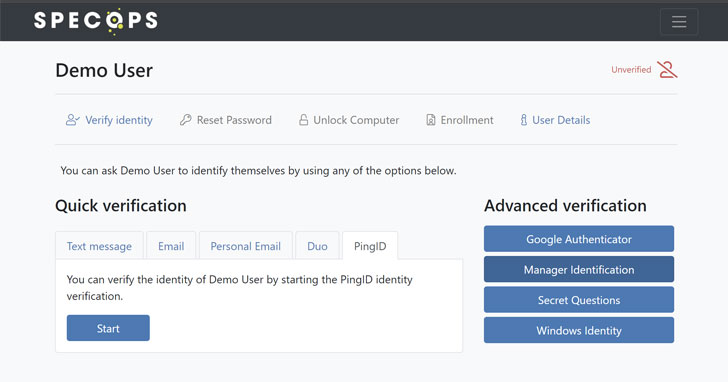 The admin view of an energetic helpdesk consumer verification using Specops Protected Assistance Desk
The admin view of an energetic helpdesk consumer verification using Specops Protected Assistance Desk
Only then is the technician permitted to reset the user’s password. This tends to make it unachievable for the technician to skirt the procedures and grant a password reset to somebody who has unsuccessful to meet the security requirements.
Exam out Specops Protected Assistance Desk in your Advert surroundings for free of charge to see how it will work.
Discovered this post exciting? Abide by THN on Fb, Twitter and LinkedIn to read through more exceptional written content we publish.
Some parts of this post are sourced from:
thehackernews.com

 FontOnLake: “Sophisticated” malware targets Linux systems
FontOnLake: “Sophisticated” malware targets Linux systems