Menace actors are increasingly mimicking legit applications like Skype, Adobe Reader, and VLC Participant as a means to abuse rely on associations and maximize the probability of a productive social engineering attack.
Other most impersonated respectable apps by icon include 7-Zip, TeamViewer, CCleaner, Microsoft Edge, Steam, Zoom, and WhatsApp, an evaluation from VirusTotal has unveiled.
“One particular of the easiest social engineering methods we’ve noticed requires building a malware sample seem to be a genuine plan,” VirusTotal reported in a Tuesday report. “The icon of these programs is a critical aspect made use of to encourage victims that these courses are legitimate.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
It’s no surprise that risk actors vacation resort to a variety of methods to compromise endpoints by tricking unwitting consumers into downloading and operating seemingly innocuous executables.

This, in change, is principally attained by using advantage of legitimate domains in a bid to get all around IP-dependent firewall defenses. Some of the top rated abused domains are discordapp[.]com, squarespace[.]com, amazonaws[.]com, mediafire[.]com, and qq[.]com.
In overall, no less than 2.5 million suspicious files downloaded from 101 domains belonging to Alexa’s prime 1,000 websites have been detected.
The misuse of Discord has been well-documented, what with the platform’s material shipping and delivery network (CDN) becoming a fertile floor for hosting malware together with Telegram, though also giving a “fantastic communications hub for attackers.”
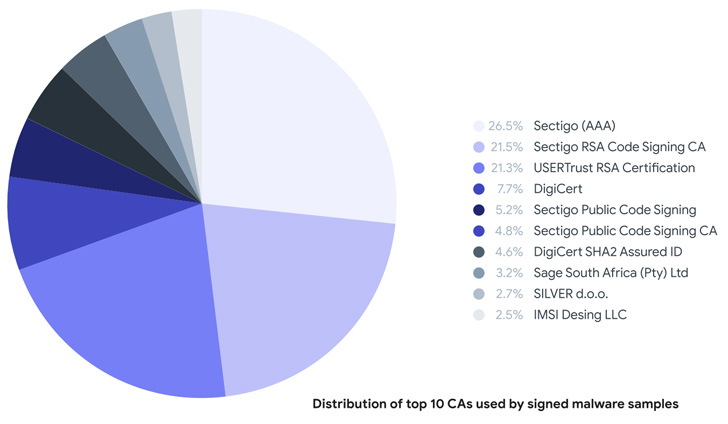
A further oft-utilised strategy is the exercise of signing malware with legitimate certificates stolen from other software program makers. The malware scanning support mentioned it found more than one particular million destructive samples due to the fact January 2021, out of which 87% had a respectable signature when they ended up initially uploaded to its database.
VirusTotal mentioned it also uncovered 1,816 samples considering that January 2020 that masqueraded as authentic software package by packaging the malware in installers for other common computer software these types of as Google Chrome, Malwarebytes, Zoom, Courageous, Mozilla Firefox, and Proton VPN.

These a distribution method can also outcome in a provide chain when attackers manage to crack into a genuine software’s update server or attain unauthorized obtain to the resource code, building it probable to sneak the malware in the type of trojanized binaries.
Alternatively, legitimate installers are remaining packed in compressed files along with malware-laced files, in 1 circumstance like the legit Proton VPN installer and malware that installs the Jigsaw ransomware.
That’s not all. A 3rd system, albeit additional advanced, involves incorporating the authentic installer as a moveable executable useful resource into the malicious sample so that the installer is also executed when the malware is run so as to give an illusion that the computer software is doing work as supposed.
“When considering about these tactics as a entire, one particular could conclude that there are both equally opportunistic factors for the attackers to abuse (like stolen certificates) in the shorter and mid expression, and routinely (most possible) automated treatments in which attackers aim to visually replicate purposes in distinct ways,” the scientists mentioned.
Found this post attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to study much more distinctive articles we publish.
Some sections of this short article are sourced from:
thehackernews.com


 Over 200,000 DrayTek routers vulnerable to total device takeover
Over 200,000 DrayTek routers vulnerable to total device takeover