A hack-for-hire group that was initial exposed in 2019 has expanded its emphasis to set its sights on entities with enterprise or political ties to Russia.
Dubbed Void Balaur, the cyber mercenary collective has a history of launching cyberattacks against biotechnology and telecom organizations since 2015. As lots of as 3,500 victims have been reported as of November 2021.
“Void Balaur […] mainly dabbles in cyber espionage and details theft, offering the stolen details to any individual prepared to spend,” Pattern Micro observed at the time.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Attacks executed by the group are commonly both generic and opportunistic and are aimed at getting unauthorized accessibility to greatly-utilised email expert services, social media, messaging, and corporate accounts.
Previously this June, Google’s Menace Assessment Group (TAG) took the wraps off a established of credential theft attacks targeting journalists, European politicians, and non-profit’s mounted by the threat actor.
“Void Balaur also goes soon after targets useful for prepositioning or facilitating long run attacks, SentinelOne researcher Tom Hegel claimed, incorporating the targets span Russia, the U.S., the U.K., Taiwan, Brazil, Kazakhstan, Ukraine, Moldova, Ga, Spain, Central African Republic, and Sudan.
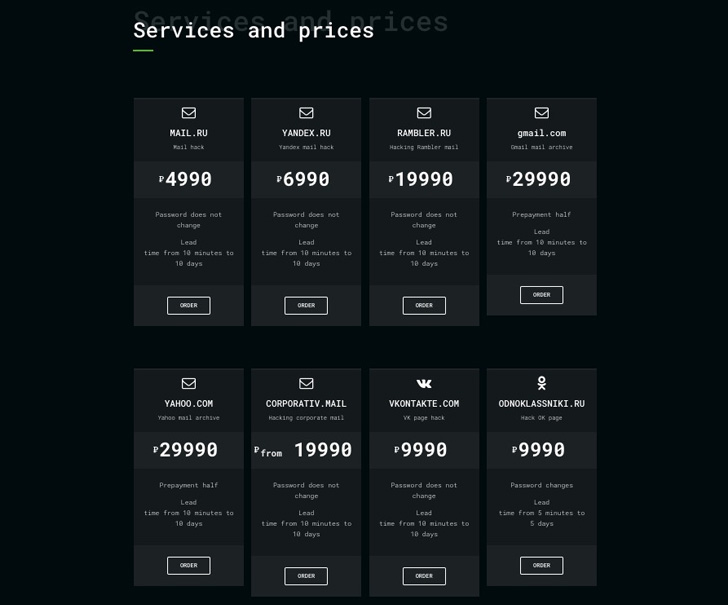
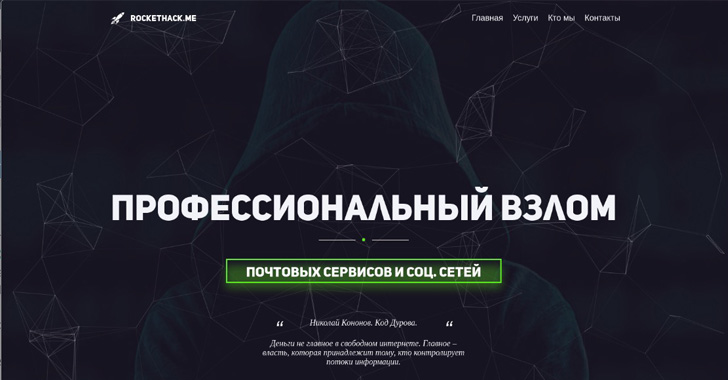
The hack-for-use service featuring linked to the group is claimed to be advertised underneath diverse personas, these kinds of as Hacknet and RocketHack. In excess of the several years, the operators have furnished other solutions, like remote entry to gadgets, SMS records, and serious-time locale monitoring.
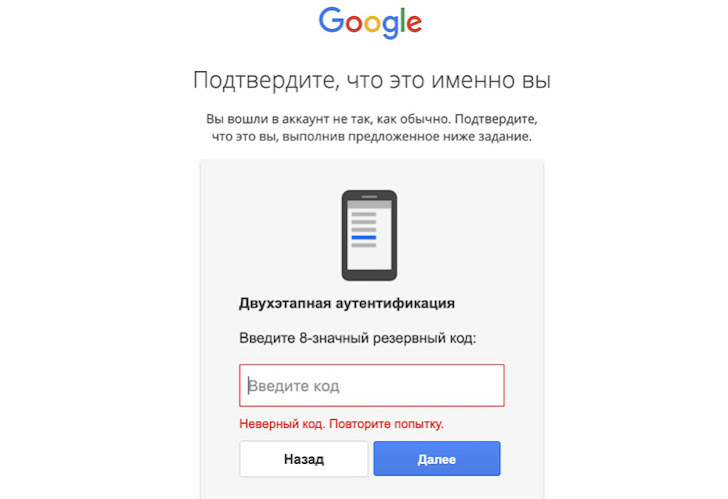
What’s far more, the attack infrastructure operated by Void Balaur encompasses a lot more than 5,000 exceptional domains that claim to be email web-sites, authentication expert services, and community products and services portals.

But in what appears to be an operational oversight, one of the domains controlled by the group (accounts-my-mail-gmail[.]com) resolved to an IP deal with that is owned and operated by the Russian Federal Guard Support (FSO) in early 2022, suggesting a possible relationship.
Whilst Void Balaur’s attacks are aimed at men and women and corporations across the world, campaigns mounted in 2022 have singled out people today that are concerned in enterprise and political scenarios that are of curiosity to Russia.
Also common is the use of highly reproducible phishing e-mails that mimic nearby federal government solutions or banking companies to trick targets into providing their account qualifications on clicking a destructive connection.
“Void Balaur stays a very lively and evolving danger to individuals across the globe. From the focusing on of properly recognised email providers to the presenting of hacking company networks, the group signifies a crystal clear example of the hack-for-retain the services of marketm,” Hegel claimed.
Found this posting exciting? Comply with THN on Fb, Twitter and LinkedIn to study far more special articles we submit.
Some elements of this short article are sourced from:
thehackernews.com

 Seven-Year Mobile Surveillance Campaign Targets Uyghurs
Seven-Year Mobile Surveillance Campaign Targets Uyghurs