Attackers are actively producing attempts to exploit a new variant of a lately disclosed privilege escalation vulnerability to probably execute arbitrary code on thoroughly-patched units, as soon as all over again demonstrating how adversaries transfer rapidly to weaponize a publicly readily available exploit.
Cisco Talos disclosed that it “detected malware samples in the wild that are trying to acquire edge of this vulnerability.”
Tracked as CVE-2021-41379 and found out by security researcher Abdelhamid Naceri, the elevation of privilege flaw impacting the Windows Installer software part was at first resolved as section of Microsoft’s Patch Tuesday updates for November 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Nonetheless, in what is a situation of an insufficient patch, Naceri found that it was not only attainable to bypass the take care of applied by Microsoft but also accomplish neighborhood privilege escalation via a newly discovered zero-working day bug.
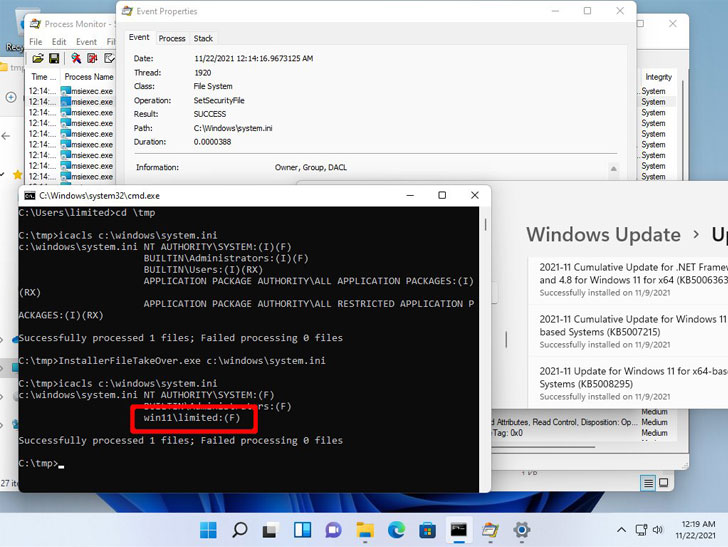
The evidence-of-principle (PoC) exploit, dubbed “InstallerFileTakeOver,” will work by overwriting the discretionary entry regulate list (DACL) for Microsoft Edge Elevation Assistance to substitute any executable file on the procedure with an MSI installer file, allowing an attacker to operate code with Process privileges.
An attacker with admin privileges could then abuse the accessibility to obtain total command above the compromised technique, including the capability to download more computer software, and modify, delete, or exfiltrate sensitive info saved in the equipment.

“Can ensure this is effective, local priv esc. Tested on Windows 10 20H2 and Windows 11. The prior patch MS issued didn’t resolve the issue effectively,” tweeted security researcher Kevin Beaumont, corroborating the findings.
Naceri mentioned that the newest variant of CVE-2021-41379 is “a lot more impressive than the unique a single,” and that the ideal system of motion would be to wait for Microsoft to launch a security patch for the dilemma “because of to the complexity of this vulnerability.”
It truly is not exactly apparent when Microsoft will act on the community disclosure and launch a correct. We have achieved out to the business for remark, and we will update the story if we hear back again.
Identified this write-up attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to read through additional special material we post.
Some sections of this report are sourced from:
thehackernews.com

 VMware Warns of Newly Discovered Vulnerabilities in vSphere Web Client
VMware Warns of Newly Discovered Vulnerabilities in vSphere Web Client