Security scientists are warning of formerly undisclosed flaws in completely patched Microsoft Trade servers getting exploited by malicious actors in authentic-entire world attacks to obtain distant code execution on impacted programs.
That’s in accordance to Vietnamese cybersecurity company GTSC, which identified the shortcomings as aspect of its security monitoring and incident response initiatives in August 2022.
The two vulnerabilities, which are formally but to be assigned CVE identifiers, are being tracked by the Zero Day Initiative as ZDI-CAN-18333 (CVSS score: 8.8) and ZDI-CAN-18802 (CVSS score: 6.3).

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
GTSC explained that thriving exploitation of the flaws could be abused to achieve a foothold in the victim’s units, enabling adversaries to fall web shells and carry out lateral actions across the compromised network.

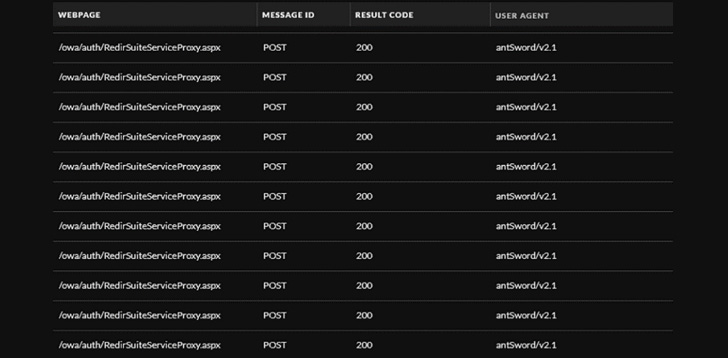
“We detected webshells, largely obfuscated, becoming dropped to Exchange servers,” the business famous. “Applying the consumer-agent, we detected that the attacker works by using Antsword, an energetic Chinese-based mostly open up source cross-system website administration device that supports web shell management.”
Exploitation requests in IIS logs are claimed to appear in the exact same format as the ProxyShell Trade Server vulnerabilities, with GTSC noting that the qualified servers had now been patched versus the flaws that came to gentle in March 2021.
The cybersecurity business theorized that the attacks are very likely originating from a Chinese hacking group owing to the web shell’s encoding in simplified Chinese (Windows Code site 936).
Also deployed in the attacks is the China Chopper web shell, a light-weight backdoor that can grant persistent remote entry and make it possible for attackers to reconnect at any time for even more exploitation.
It’s well worth noting that the China Chopper web shell was also deployed by Hafnium, a suspected state-sponsored team running out of China, when the ProxyShell vulnerabilities ended up subjected to popular exploitation last yr.
More publish-exploitation functions observed by GTSC include the injection of destructive DLLs into memory, drop and execute additional payloads on the contaminated servers using the WMI command-line (WMIC) utility.
The company mentioned at least extra than a person corporation has been the sufferer of an attack campaign leveraging the zero-working day flaws. More details about the bugs have been withheld in light of active exploitation.
We have reached out to Microsoft for more remark, and we will update the story if we hear again.

In the interim, as short term workarounds, it is really proposed to increase a rule to block requests with indicators of compromise working with the URL Rewrite Rule module for IIS servers –
- In Autodiscover at FrontEnd, pick out tab URL Rewrite, and then choose Ask for Blocking
- Incorporate string “.*autodiscover.json.*@.*Powershell.*” to the URL Path, and
- Issue enter: Opt for Ask for_URI
“I can verify important quantities of Exchange servers have been backdoored – which includes a honeypot,” Security researcher Kevin Beaumont said in a sequence of tweets, incorporating, “it appears to be like a variant of proxying to the admin interface all over again.”
“If you do not run Microsoft Exchange on premise, and you should not have Outlook Web App facing the internet, you are not impacted,” Beaumont mentioned.
Found this posting exciting? Comply with THN on Facebook, Twitter and LinkedIn to go through far more exceptional information we submit.
Some elements of this posting are sourced from:
thehackernews.com


 Researchers Discover Chaos, a Golang Multipurpose Botnet
Researchers Discover Chaos, a Golang Multipurpose Botnet