Company software program company Zoho on Friday warned that a recently patched critical flaw in its Desktop Central and Desktop Central MSP is currently being actively exploited by destructive actors, marking the 3rd security vulnerability in its solutions to be abused in the wild in a span of four months.

The issue, assigned the identifier CVE-2021-44515, is an authentication bypass vulnerability that could permit an adversary to circumvent authentication protections and execute arbitrary code in the Desktop Central MSP server.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“If exploited, the attackers can obtain unauthorized entry to the products by sending a specially crafted request top to distant code execution,” Zoho cautioned in an advisory. “As we are noticing indications of exploitation of this vulnerability, we strongly recommend clients to update their installations to the latest create as before long as probable.”
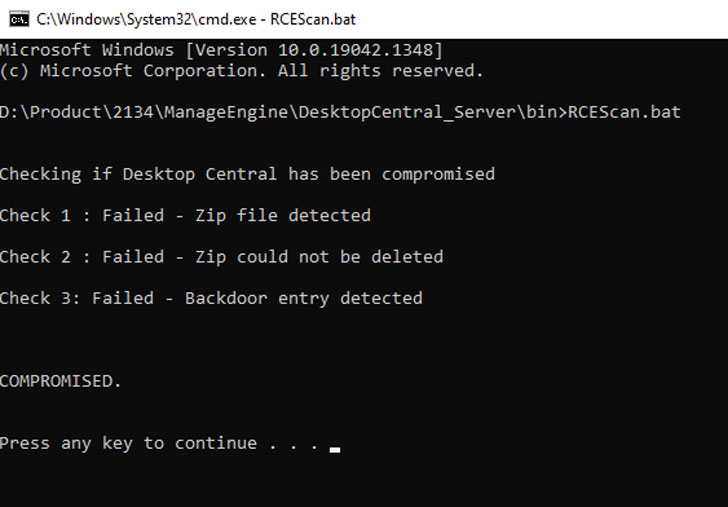
The business has also manufactured readily available an Exploit Detection Device that will assistance buyers discover symptoms of compromise in their installations.

With this growth, CVE-2021-44515 joins two other vulnerabilities CVE-2021-44077 and CVE-2021-40539 that have been weaponized to compromise the networks of critical infrastructure companies throughout the entire world.
The disclosure also arrives a working day following the U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned that CVE-2021-44077 — an unauthenticated, distant code execution vulnerability affecting ServiceDesk Furthermore — is getting exploited to fall web shells and carry out an array of write-up-exploitation activities as element of a campaign dubbed “TiltedTemple.”
Identified this write-up intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read more distinctive content material we post.
Some pieces of this report are sourced from:
thehackernews.com


 Ex Ubiquiti Developer Arrested for Data Theft
Ex Ubiquiti Developer Arrested for Data Theft