Microsoft’s Active Listing is said to be applied by 95% of Fortune 500. As a final result, it is a prime goal for attackers as they glimpse to acquire obtain to credentials in the group, as compromised qualifications offer one particular of the most straightforward techniques for hackers to accessibility your data.
A essential authentication technology that underpins Microsoft Energetic Listing is Kerberos. Unfortunately, hackers use lots of different attacks versus Lively Directory’s implementation of the Kerberos authentication protocol. 1 of all those is AS-REP Roasting. So what is AS-REP Roasting, and how can organizations shield by themselves?
What is Active Listing Kerberos?
Kerberos was originally formulated by the Massachusetts Institute of Technology (MIT) and centered all over applying tickets to set up believe in. Microsoft’s implementation of Kerberos identified in Lively Directory is based on Kerberos Network Authentication Service (V5) as defined in RFC 4120. Nonetheless, Microsoft has added to and increased Kerberos with its protocol requirements and quite a few extensions.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
There are three distinctive factors identified in Kerberos authentication as located in Microsoft Energetic Directory. These include things like:
- Shopper – The consumer is the entity that is looking to receive tickets from the KDC
- Application Server – The resource that needs the issued tickets offered for authentication
- Crucial Distribution Centre (KDC) – The KDC is the reliable third-party that issues the authentication tickets. In Microsoft Active Listing, the KDC is each and every area controller servicing the Energetic Directory domain.
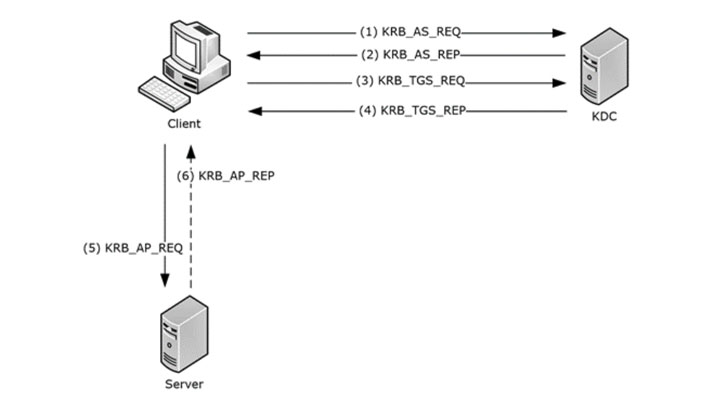 Overview of the Kerberos authentication protocol ticket trade
Overview of the Kerberos authentication protocol ticket trade
Crucial for understanding the threats linked with Active Directory credential theft, Kerberos is the default protocol utilized when logging into a Windows device section of an Energetic Listing area. It has been the default authentication protocol, replacing NTLM since Windows 2000 and later. What are the discrepancies in between the two?
The two protocols take care of authentication in another way. The NTLM authentication protocol relies on a a few-way handshake. The authentication facts is exchanged between the consumer and server to authenticate a user. Conversely, Kerberos works by using a two-way process that relies on a ticket-granting company working with a key distribution centre (KDC).
NTLM works by using password hashing, while Kerberos works by using encryption. When Kerberos is the default authentication system, NTLM is continue to made use of as a fallback authentication protocol. If authentication can’t transpire using Kerberos, the system will use NTLM rather.
What is AS-REP Roasting?
Even even though Kerberos is a significantly far more safe authentication protocol than NTLM, it is not devoid of its very own set of vulnerabilities, some of which can stem from the unique person account configurations configured for the account in Energetic Listing.
A single of the initial techniques in Kerberos authentication is preauthentication. Pre-authentication uses the user’s password to encrypt a timestamp. The area controller (DC) will decrypt this to validate the right password and not have a earlier request replayed. A vulnerability can final result when preauthentication is disabled.
After this is disabled, a hacker can ask for authentication knowledge for any consumer, and the DC will return an encrypted ticket-granting ticket (TGT). It can then be utilised to brute power in an offline atmosphere to crack the password.
Preauthentication can be disabled on any user account in Active Listing on the Account tab underneath the Account possibilities. Look for the checkbox “Do not require Kerberos preauthentication.”
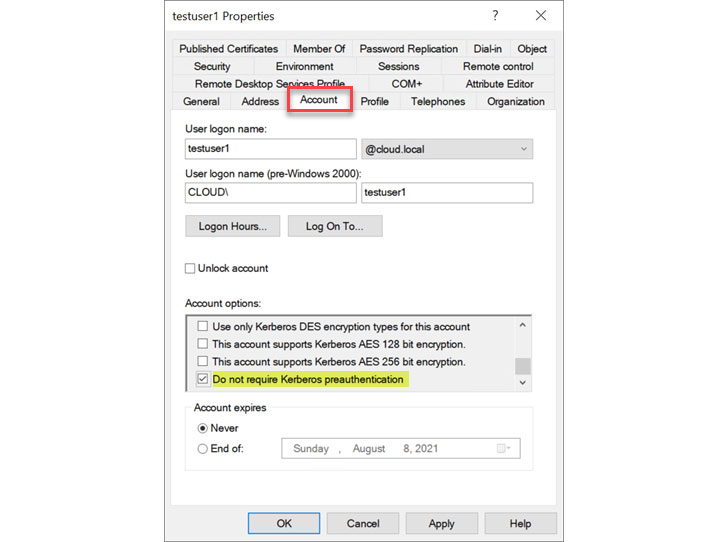 Placing the do not have to have Kerberos preauthentication flag in Active Listing
Placing the do not have to have Kerberos preauthentication flag in Active Listing
AS-REP Roasting is the system that enables retrieving password hashes for consumers that have this flag established in Lively Directory. On top of that, different cybersecurity and hacking equipment let cracking the TGTs harvested from Lively Listing. These include Rubeus and Hashcat.
Utilizing a software like Rubeus, attackers can obtain the accounts that do not demand preauthentication and then extract the ticket-granting ticket (TGT) knowledge for cracking the password offline.
Data can be reworked into a structure that can be cracked by an offline instrument these types of as Hashcat, which can use brute force password cracking towards the hashes. This approach incorporates the use of a dictionary file for brute-force password guessing.
Blocking the AS-REP Roasting attack
An noticeable way to stop the AS-REP Roasting attack is to audit your Active Listing environment and ensure there are no accounts configured with the “Do not have to have Kerberos preauthentication.”
In addition to auditing your Energetic Listing settings for improperly configured preauthentication, you want to make sure customers are expected to use strong, advanced passwords.
Also, it is very important to ensure passwords are not identified in a breached password database as breached password lists are made use of to crack passwords extracted making use of the AS-REP Roasting attack. Breached password defense is not natively identified in Energetic Listing. So, a third-party option is required for this style of security.
Breached password safety with Specops
Imposing efficient password insurance policies and applying a breached password safety option for Lively Listing is essential to assure your atmosphere is not susceptible to Kerberos attacks these as AS-REP Roasting. In addition, successful password insurance policies assistance make sure people are utilizing solid passwords that are not quickly guessed or normally effortless to attack with brute pressure or other prevalent password attacks.
Specops Password Plan will take password procedures into the modern era with operation and characteristics not natively observed in Energetic Listing. It helps prevent weak and even breached passwords from use in the ecosystem applying one of the most critical capabilities of Specops Password Plan, Breached Password Defense.
Just lately, Specops unveiled the next iteration of Breached Password Safety with Reside Attack Information. The Reside Attack Information arrives from a world honeypot alternative made use of by Specops to get the passwords that are applied in stay brute drive attacks. These are built-in with the present safety made available by Specops to clients utilizing the Breached Password database and the resolution is continuously up-to-date with the most modern breached passwords.
In addition, with Breached Password Defense identified in Specops Password Coverage, corporations can swiftly apply breached password safety to prevent users from applying compromised passwords. For illustration, if consumers try to decide on a password uncovered in the intensive database of breached passwords taken care of by Specops (around two billion), the password is not approved. In addition, if a user’s password turns into breached soon after it has been outlined in Energetic Listing, companies can use Specops Password Plan to pressure their buyers to change the password at up coming login.
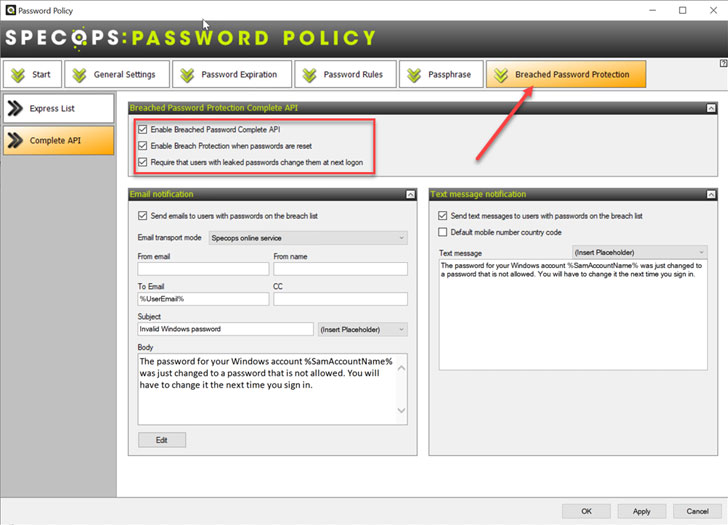 Specops Password Coverage Breached Password Protection
Specops Password Coverage Breached Password Protection
On top of the Breached Password Safety in Specops Password Policy, it adds a lot of other features and benefits to bolster your organization’s ability to tailor password insurance policies to match the organization desires and sustain large stages of security in your surroundings. These incorporate:
- Means to increase a number of custom made password dictionaries
- Size-based mostly password growing old
- Constructed-in password expiration notifications
- Password content material restrictions
- Frequent expressions to even more handle password information
- Several password reset options
- Minimal quantity of people that are demanded adjusted for a password reset
Concerns
Active Listing is the amount a person identity option utilised in companies these days. Unfortunately, his usually means attackers greatly goal Lively Directory environments to obtain techniques to steal credentials. Their attack approaches consist of attacking the authentication protocols made use of by Lively Listing, together with Kerberos. AS-REP Roasting is a style of attack that appears to be to locate accounts with the preauthentication flag for Kerberos unset for people.
As soon as identified, hacking equipment can be made use of to brute power consumer passwords. Just one of the ideal means companies can defend on their own is to have excellent password procedures in area alongside with breached password security, as attackers typically use breached password databases in an AS-REP Roasting attack. Specops Password Coverage allows companies bolster their password security, like Breached Password Security.
Uncovered this article fascinating? Comply with THN on Facebook, Twitter and LinkedIn to read through extra distinctive articles we post.
Some parts of this short article are sourced from:
thehackernews.com


 Cisco Patches Critical Authentication Bug With Public Exploit
Cisco Patches Critical Authentication Bug With Public Exploit