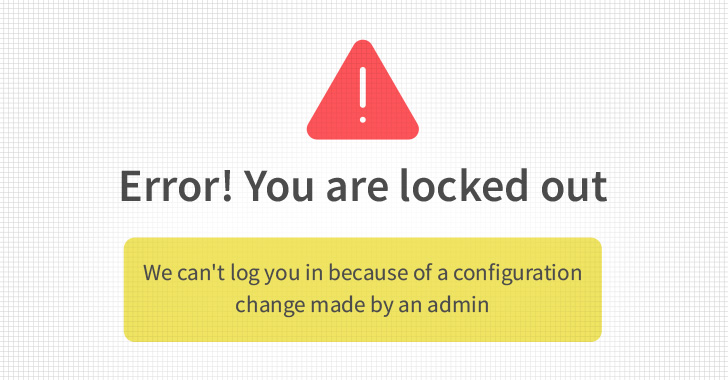
Think about this: a corporation-wide lockout to the business CRM, like Salesforce, for the reason that the organization’s external admin tries to disable MFA for by themselves. They never believe to consult with with the security crew and you should not take into account the security implications, only the ease which they will need for their workforce to use their login.
This CRM, however, defines MFA as a top rated-tier security placing for instance, Salesforce has a “Superior Assurance Login Value” configuration and quickly locks out all people as a security precaution. The full business hits a standstill and is disappointed and puzzled.
Deeply about, this is not a 1-off occasion, admins for business enterprise-critical SaaS apps often sit outside the house the security office and have profound handle. Untrained and not targeted on security steps, these admins are doing the job towards their departmental KPIs. For instance, Hubspot is commonly owned by the promoting department, also, Salesforce is generally owned by the business enterprise section, etcetera. Enterprise departments individual these applications simply because it is what permits them to do their occupation effectively. On the other hand, the paradox lies in the fact that it can be the security team’s obligation to protected the organization’s SaaS app stack and they are unable to correctly execute this job without having full handle of the SaaS app.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The 2022 SaaS Security Survey Report, operate by CSA and Adaptive Defend, delves into the reality of this paradox, presenting details from CISOs and security industry experts right now. This report will take a look at critical details details from the respondents and talk about what the resolution for security teams could be.
Find out how your security groups can regain management of all SaaS apps.
SaaS Apps in the Palms of Enterprise Departments
Throughout a common group, a broad array of SaaS apps are employed (see figure 1), from cloud knowledge platforms, file sharing and collaboration applications to CRM, project and do the job management, internet marketing automation, and a total ton extra. The will need for each and each SaaS app fills a particular niche position expected by the organization. With no the use of all these SaaS applications, a enterprise could obtain by itself lagging or using extra time to accomplish its KPIs.
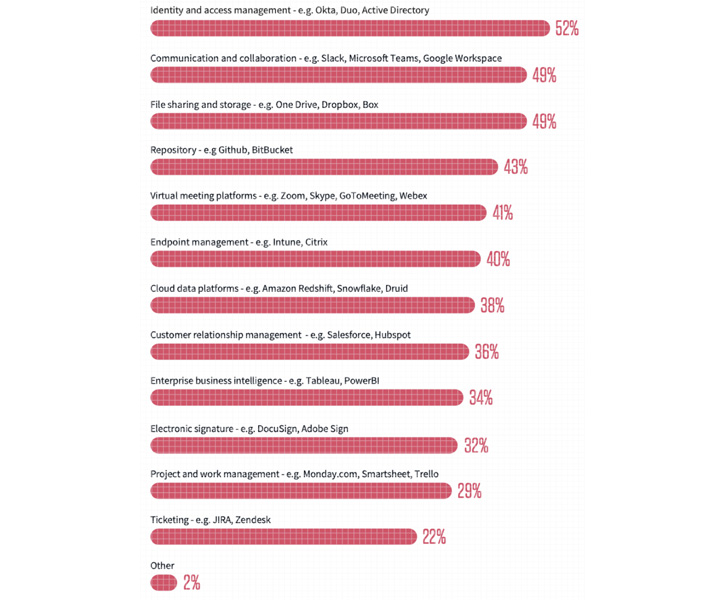 Figure 1. Kinds of Applications Applied, 2022 SaaS Security Survey Report
Figure 1. Kinds of Applications Applied, 2022 SaaS Security Survey Report
The 2022 SaaS Security Survey Report stories that 40% of these applications are managed and owned by non-security teams, these kinds of as income, internet marketing, legal, etc. (see in determine 2). Although the security and IT groups are claimed to be the most important location for SaaS app administration, it is the 40% of small business departments also getting portion and having whole accessibility that complicates the risk landscape.
Security groups cannot get away this possession as the enterprise applications’ homeowners want to keep a superior amount of access to their appropriate SaaS applications for optimum use. Yet, without in-depth expertise of security or the vested curiosity (a security KPI that reflects on their get the job done products), it’s not acceptable for the security staff to hope that the small business operator will make sure a higher stage of security in their SaaS.
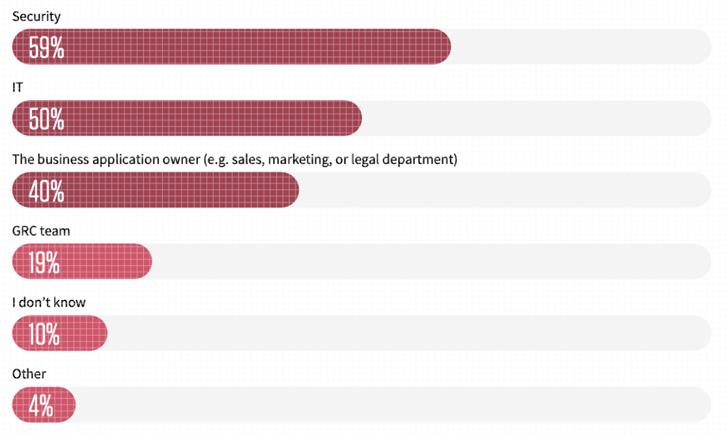 Figure 2. Departments Managing SaaS applications, 2022 SaaS Security Study Report
Figure 2. Departments Managing SaaS applications, 2022 SaaS Security Study Report
Unpacking the SaaS Application Ownership Paradox
When requested the primary rationale for misconfiguration-led security incidents (determine 3), respondents of the study report cited these at their major 4: (1) There are too lots of departments with access to security settings (2) Deficiency of visibility to security configurations when they are adjusted (3) Lack of SaaS security awareness (4) Misappropriated person permissions. All of these reasons, either overtly or implied, can be attributed to the SaaS App Possession Paradox.
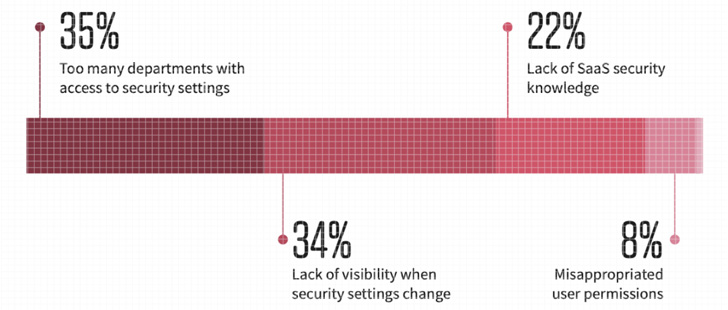 Figure 3. Leading Leads to of Security Incidents, 2022 SaaS Security Study Report
Figure 3. Leading Leads to of Security Incidents, 2022 SaaS Security Study Report
The leading result in of security incidents induced by misconfigurations is possessing much too lots of departments with entry to security configurations. This goes hand in hand with the upcoming induce – absence of visibility when security improvements are altered. A enterprise department may make changes to an application setting to improve its relieve of use with out consulting with or notifying the security division.
In addition, misappropriated person permissions can effortlessly stem from a small business section owner at the helm who is not spending cautious interest to the app’s security. Frequently people are granted privileged permissions that they will not even need to have.
How Security Groups Can Get back Regulate
With this shared accountability design, the only economical way to bridge this communication hole is by a SaaS Security Posture Management platform (SSPM). Hailed as a Have to HAVE alternative to repeatedly assess security challenges and manage the SaaS applications’ security posture in the “4 Should-Have Technologies That Manufactured the Gartner Hoopla Cycle for Cloud Security, 2021”, this kind of a remedy can notify the security staff on any app configuration adjust made by the app operator, and supply very clear instructions on how to fix it as a result of a ticketing or collaboration administration technique.
With an SSPM solution, owned and managed by the organization’s security staff, the security staff can obtain full visibility of all the firm’s SaaS apps and their security settings, which includes person roles and permissions. W
Organizations can acquire it just one stage even more and have the application house owners be a part of the SSPM system so they can actively management and oversee all configurations in their owned apps. By using a scoped admin functionality (figure 4) the security group can grant the app proprietors accessibility to the apps they individual and can remediate security issues, with their supervision and direction.
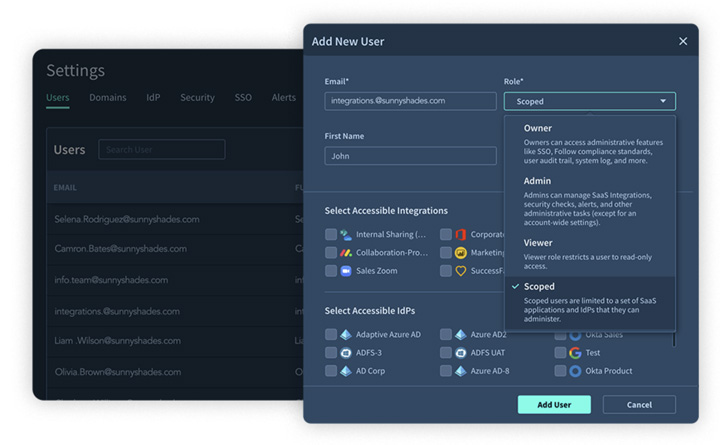 Determine 4. Scoped Admin element in Adaptive Shield’s SSPM system
Determine 4. Scoped Admin element in Adaptive Shield’s SSPM system
You will find no way to reduce business departments’ entry to SaaS application security settings, and even though consumers throughout the firm really should be educated on standard SaaS security in purchase to decrease the risk that may occur from company departments, it would not often occur or it is just not more than enough. Organizations need to put into practice a alternative that can help stay clear of these scenarios by enabling visibility and command for the security crew, alerting on configuration drifts, audit logs that give perception into steps in just the SaaS apps and scoped admins.
Get a 10-moment demo of how Adaptive Shield’s SSPM alternative assists security groups regain command.
Discovered this article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to browse much more distinctive information we post.
Some elements of this article are sourced from:
thehackernews.com

 CREST and OWASP Partner on Verification Standard Program
CREST and OWASP Partner on Verification Standard Program