Let us to start with just take a appear back at 2020!
Adding to the record of difficulties that surfaced previous year, 2020 was also grim for private facts security, as it has marked a new report number of leaked qualifications and PI info.
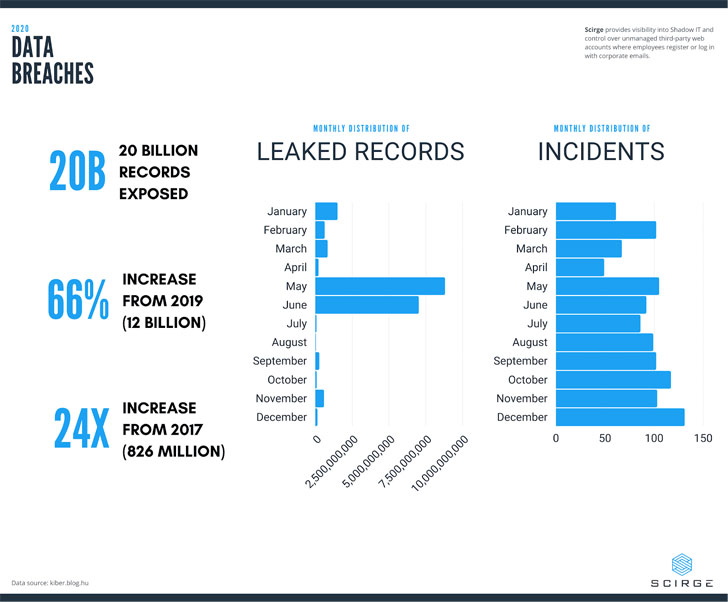
A whopping 20 billion documents were stolen in a solitary yr, increasing 66% from 12 billion in 2019. Incredibly, this is a 9x raise from the comparatively “modest” sum of 2.3 billion documents stolen in 2018.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
This craze would seem to in good shape an exponential curve even even worse, we are nonetheless to see the fallouts from the conclude of the yr “Solorigate” marketing campaign, which has the possible to marginalize even these numbers by the conclude of 2021.
Located among the the leaked knowledge are usernames, passwords, credit rating card numbers, lender account specifics, health care information, and other own info. Destructive actors employ these treasure troves of facts for fraud and even further attacks.
In just the initial quarter of 2020, the Dutch federal government managed to drop a tricky generate made up of confidential citizen data. Meanwhile, the UK federal government uncovered 28 million kid’s info to betting corporations, and Microsoft uncovered 250 million records of customer support—including customers’ geographic info, IP addresses, and other non-public info.
By April, Zoom had lost 500,000 passwords at the get started of the world remote performing time period. In June of Q2, Oracle had also leaked billions of web monitoring details by storing details on an unsecured server.
Q3 kicked off with Joe Biden’s marketing campaign application exposing millions of users’ sensitive voter data. This was adopted by 300,000 Spotify users slipping target to account takeover makes an attempt soon after their qualifications have been produced general public.
The 12 months finished with Solorigate: an incident with a lasting effects that has yet to be entirely seen. In the end, 2020 shut with a full of 1,114 incidents, with many governments and effectively-recognized brands—such as Estee Lauder, Marriott, Nintendo, and GoDaddy—involved in big-scale breaches.
Why are companies and corporations even now failing?
This craze of information breaches is really disappointing when when compared to the staggering $120 Billion in worldwide IT security spending according to Gartner, this range has grown every single 12 months quickly.
The only probable solution to this inconsistency rests in user recognition and the risk that existing technologies are lacking one thing significant to change the tide on these tendencies.
The most typical bring about guiding info breaches is the leak of some authentication measure—this could be a username, password, token, API-crucial, or a negligent password-considerably less server or application.
Consumers are registering to third-party web sites and services with corporate email addresses and qualifications every single working day. In tandem, they create huge blind spots in visibility and a field of Shadow IT that no audit or security tool has been in a position to mitigate hence far. Each individual worker has all-around 200 accounts—for each individual 1,000 employees, that is 200,000 probably unidentified or weak passwords, numerous of which may possibly be company similar.
The moment these 3rd events get compromised, the credentials received may be reused to attain unauthorized obtain to other company solutions, this sort of as email accounts or VPN servers, making use of attack approaches like credential stuffing or password spraying.
This was particularly the situation with British Airways, which gained a history GDPR high-quality of £20 million after 400,000 passengers’ info was breached, initiated via a VPN gateway accessed by a compromised account.
Most substantial organizations use facts leak avoidance systems however fail to defend against password leaks and account takeovers. This demonstrates an obvious have to have for a new approach—a hybrid of technological controls and fast person recognition advancement that implements a contemporary point of view on account defense.
Shedding Light on Shadow IT
Scirge was formulated with a easy and clear emphasis on solving an disregarded component of present IT security mechanisms: getting and shielding accounts designed by workforce in the cloud. This consists of the capability to observe all new registrations, as well as viewing logins with current credentials to websites and web programs.
In addition, it entails centrally managed toughness and complexity checks for all passwords while also warning consumers for good credential management.
Policy-primarily based controls may perhaps be developed to block the usage of selected email addresses or web sites. Scirge will right away offer consumers with awareness messages when they are misusing company credentials or disregarding password complexity needs.

Central intelligence assists unveil reused passwords and compromised accounts via comparing each individual enterprise-relevant account to leak databases and regionally-made use of (Energetic Directory) accounts. Scirge can illuminate organizations’ if not concealed cloud footprint though concurrently empowering end users with expertise about password hygiene, company policies, and undesirable conduct when making use of company accounts.
Scirge accomplishes each individual of these plans with a cleanse, browser-based technique. It eliminates the need to manage or look at network traffic, decrypt SSL, or burden shoppers with entire-blown agents—a common resource of general performance degradation and compatibility issues with other security equipment.
Utilizing its one of a kind features, Scirge produces visibility for all employee-made accounts and reveals password hygiene issues. Inventory for all users—including departing workers—is conveniently out there, unveiling unwanted account sharing amongst consumers and prospective insider threats of misusing identities when accessing on-line resources.
The dashboard also displays IT management what cloud applications are most utilized with out consent, helping the company comply with rules through collecting privacy procedures and T&Cs of all solutions.
Discover far more about account defense and Shadow IT recognition below or sign up to 1 of our webinars.
Found this posting exciting? Observe THN on Facebook, Twitter and LinkedIn to browse additional distinctive information we article.
Some parts of this post are sourced from:
thehackernews.com


 Chinese Hackers Targeted India’s Power Grid Amid Geopolitical Tensions
Chinese Hackers Targeted India’s Power Grid Amid Geopolitical Tensions