A Windows-based mostly remote accessibility Trojan considered to be developed by Pakistani hacker teams to infiltrate desktops and steal users’ facts has resurfaced just after a two-year span with retooled capabilities to goal Android and macOS equipment.
In accordance to cybersecurity organization Kaspersky, the malware — dubbed “GravityRAT” — now masquerades as legit Android and macOS applications to capture unit details, call lists, e-mail addresses, and phone and text logs and transmit them to an attacker-controlled server.
Initial documented by the Indian Laptop Unexpected emergency Reaction Crew (CERT-In) in August 2017 and subsequently by Cisco Talos in April 2018, GravityRAT has been regarded to focus on Indian entities and businesses through malware-laced Microsoft Business Term files at least considering the fact that 2015.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Noting that the danger actor formulated at least 4 diverse variations of the espionage instrument, Cisco reported, “the developer was intelligent enough to keep this infrastructure harmless, and not have it blacklisted by a security vendor.”
Then final yr, it emerged that Pakistani spies employed phony Fb accounts to arrive at out to a lot more than 98 officers from a variety of defence forces and organizations, these types of as the Indian Army, Air Force, and Navy, and trick them into putting in the malware disguised as a protected messaging app identified as Whisper.
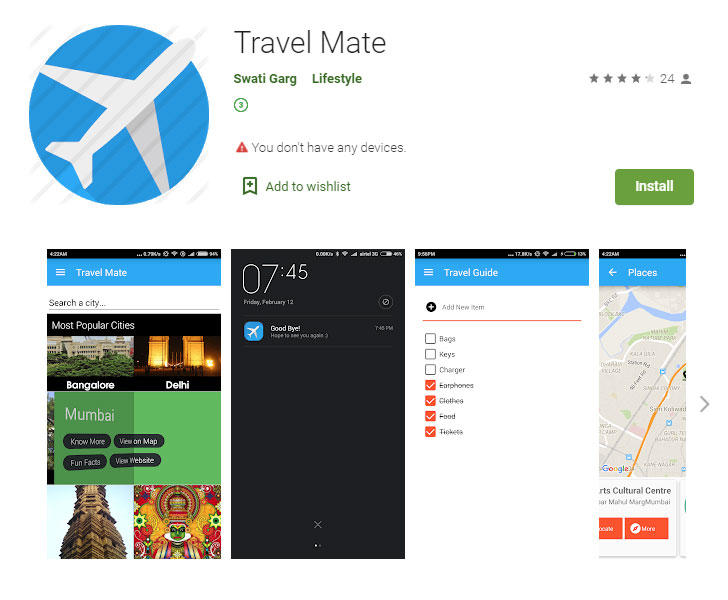
But even as the hottest evolution of GravityRAT goes beyond anti-malware evasion abilities to gain multi-system help — which include Android and macOS — the all round modus operandi remains the exact: sending targets back links to booby-trapped Android (e.g., Journey Mate Pro) and macOS applications (Enigma, Titanium) to distribute the malware.
Kaspersky reported it uncovered more than 10 variations of GravityRAT that had been being dispersed less than the guise of legitimate apps by cross-referencing the command-and-command (C2) addresses utilised by the Trojan.
In all, the trojanized purposes spanned throughout journey, file sharing, media gamers, and adult comics groups, catering to consumers of Android, macOS, and Windows, thereby allowing the attackers to grab technique facts, documents with particular extensions, a checklist of functioning processes, record keystrokes and choose screenshots, and even execute arbitrary Shell commands.
“Our investigation indicated that the actor at the rear of GravityRAT is continuing to invest in its spying capacities,” Kaspersky’s Tatyana Shishkova reported.
“Crafty disguise and an expanded OS portfolio not only let us to say that we can expect extra incidents with this malware in the APAC area, but this also supports the broader trend that destructive consumers are not essentially targeted on producing new malware, but creating confirmed types alternatively, in an try to be as profitable as achievable.”
Uncovered this post fascinating? Follow THN on Fb, Twitter and LinkedIn to browse a lot more exceptional information we put up.
Some components of this post are sourced from:
thehackernews.com

 IoT Security Foundation Launches Vulnerability Disclosure Platform
IoT Security Foundation Launches Vulnerability Disclosure Platform