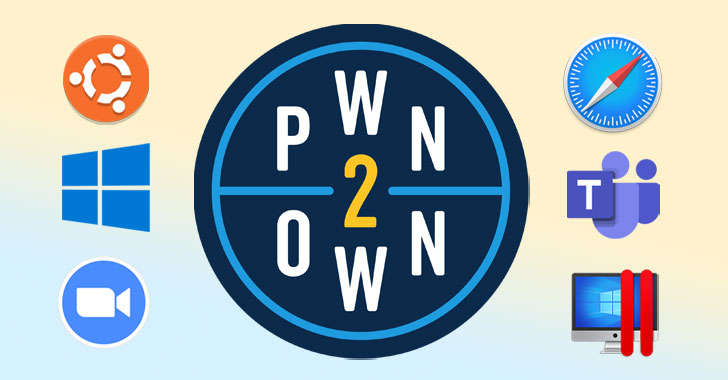
The 2021 spring version of Pwn2Very own hacking contest concluded previous week on April 8 with a 3-way tie amongst Group Devcore, OV, and Computest researchers Daan Keuper and Thijs Alkemade.
A complete of $1.2 million was awarded for 16 substantial-profile exploits over the class of the a few-working day digital occasion arranged by the Zero Day Initiative (ZDI).
Targets with successful makes an attempt incorporated Zoom, Apple Safari, Microsoft Exchange, Microsoft Teams, Parallels Desktop, Windows 10, and Ubuntu Desktop running units.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Some of the major highlights are as follows —
- Using an authentication bypass and a regional privilege escalation to wholly take over a Microsoft Exchange server, for which the Devcore staff netted $200,000
- Chaining a pair of bugs to attain code execution in Microsoft Groups, earning researcher OV $200,000
- A zero-click exploit targeting Zoom that utilized a 3-bug chain to exploit the messenger app and attain code execution on the target method. ($200,000)
- The exploitation of an integer overflow flaw in Safari and an out-of-bounds write to get kernel-amount code execution ($100,000)
- An exploit aimed at the Chrome renderer to hack Google Chrome and Microsoft Edge (Chromium) browsers ($100,000)
- Leveraging use-soon after-free, race ailment, and integer overflow bugs in Windows 10 to escalate from a regular user to Program privileges ($40,000 each and every)
- Combining 3 flaws — an uninitialized memory leak, a stack overflow, and an integer overflow — to escape Parallels Desktop and execute code on the underlying functioning program ($40,000)
- Exploiting a memory corruption bug to productively execute code on the host running procedure from inside of Parallels Desktop ($40,000)
- The exploitation of out-of-bounds entry bug to elevate from a common consumer to root on Ubuntu Desktop ($30,000)
The Zoom vulnerabilities exploited by Daan Keuper and Thijs Alkemade of Computest Security are especially noteworthy for the reason that the flaws call for no interaction of the victim other than becoming a participant on a Zoom contact. What is far more, it influences each Windows and Mac versions of the app, though it can be not very clear if Android and iOS variations are vulnerable as properly.
Complex particulars of the flaws keep on being unclear as however, and Zoom has a 90-day window to tackle the issues in advance of they are designed public. We have attained out to Zoom and we will update the story if we get a reaction.
In a assertion sharing the findings, the Dutch security business claimed the researchers “ended up then in a position to virtually absolutely consider about the program and perform actions such as turning on the digicam, turning on the microphone, studying e-mails, examining the monitor and downloading the browser heritage.”
Unbiased researcher Alisa Esage also manufactured historical past as the first female to acquire Pwn2Have just after locating a bug in virtualization software package Parallels. But she was only awarded a partial acquire for factors that the issue had been documented to ZDI prior to the party.
“I can only accept it as a fact that my profitable Pwn2Very own participation captivated scrutiny to specific debatable and likely outdated points in the contest guidelines,” Esage tweeted, introducing, “In the genuine world there is no this kind of thing as an ‘arguable point’. An exploit possibly breaks the concentrate on system or not.”
Discovered this posting fascinating? Adhere to THN on Fb, Twitter and LinkedIn to read through a lot more exclusive content we publish.
Some parts of this short article are sourced from:
thehackernews.com

 Hackers Tampered With APKPure Store to Distribute Malware Apps
Hackers Tampered With APKPure Store to Distribute Malware Apps