A new wormable botnet that spreads through GitHub and Pastebin to put in cryptocurrency miners and backdoors on target systems has returned with expanded capabilities to compromise web programs, IP cameras, and routers.
Early very last month, scientists from Juniper Danger Labs documented a crypto-mining campaign known as “Gitpaste-12,” which utilized GitHub to host destructive code containing as many as 12 regarded attack modules that are executed by means of commands downloaded from a Pastebin URL.
The attacks occurred in the course of a 12-working day period starting up from Oct 15, 2020, prior to both of those the Pastebin URL and repository had been shut down on Oct 30, 2020.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Now in accordance to Juniper, the second wave of attacks commenced on November 10 utilizing payloads from a different GitHub repository, which, amid other folks, consists of a Linux crypto-miner (“ls”), a file with a listing of passwords for brute-drive tries (“move”), and a area privilege escalation exploit for x86_64 Linux systems.
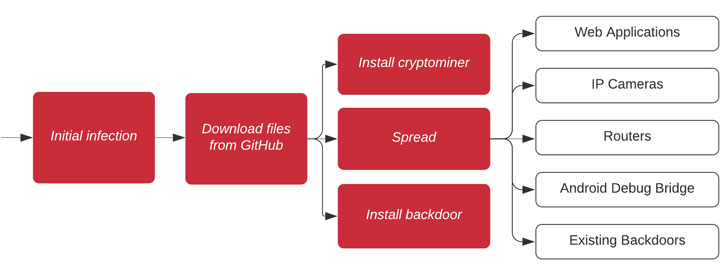
The initial an infection occurs by using X10-unix, a binary penned in Go programming language, that proceeds to down load the next-stage payloads from GitHub.
“The worm conducts a wide-ranging sequence of attacks focusing on web applications, IP cameras, routers and extra, comprising at the very least 31 regarded vulnerabilities — seven of which were also noticed in the previous Gitpaste-12 sample — as perfectly as makes an attempt to compromise open up Android Debug Bridge connections and present malware backdoors,” Juniper researcher Asher Langton observed in a Monday analysis.
Bundled in the record of 31 vulnerabilities are distant code flaws in F5 Big-IP Site visitors Management User Interface (CVE-2020-5902), Pi-hole Web (CVE-2020-8816), Tenda AC15 AC1900 (CVE-2020-10987), and vBulletin (CVE-2020-17496), and an SQL injection bug in Gasoline CMS (CVE-2020-17463), all of which came to light-weight this yr.
It is worth noting that Ttint, a new variant of the Mirai botnet, was noticed in October applying two Tenda router zero-day vulnerabilities, such as CVE-2020-10987, to unfold a Remote Access Trojan (RAT) able of carrying out denial-of-service attacks, execute destructive commands, and put into practice a reverse shell for distant obtain.
Aside from installing X10-unix and the Monero crypto mining computer software on the equipment, the malware also opens a backdoor listening on ports 30004 and 30006, uploads the victim’s exterior IP address to a private Pastebin paste, and makes an attempt to link to Android Debug Bridge connections on port 5555.
On a thriving link, it proceeds to download an Android APK file (“weixin.apk”) that sooner or later installs an ARM CPU model of X10-unix.
In all, at the very least 100 unique hosts have been spotted propagating the an infection, per Juniper estimates.
The entire established of malicious binaries and other suitable Indicators of Compromise (IoCs) connected with the campaign can be accessed listed here.
Discovered this article interesting? Adhere to THN on Fb, Twitter and LinkedIn to read more distinctive content we submit.
Some areas of this post are sourced from:
thehackernews.com


 Government Threatens Tech Firms with Fines of 10% of Turnover
Government Threatens Tech Firms with Fines of 10% of Turnover