The operators of the XCSSET macOS malware have upped the stakes by earning iterative improvements that insert guidance for macOS Monterey by upgrading its supply code factors to Python 3.
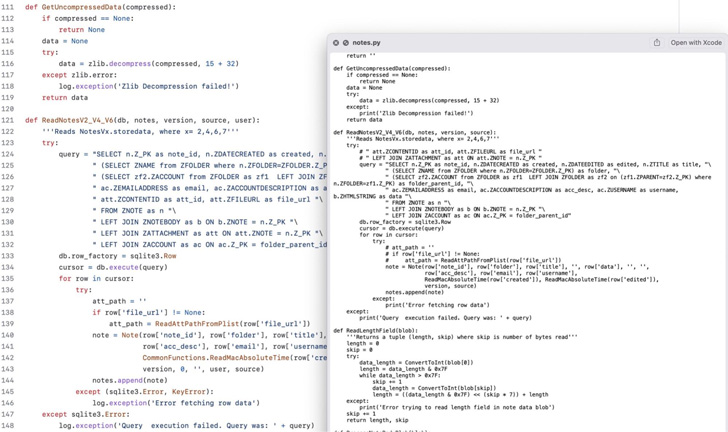
“The malware authors have modified from hiding the key executable in a faux Xcode.app in the initial versions in 2020 to a faux Mail.app in 2021 and now to a fake Notes.app in 2022,” SentinelOne researchers Phil Stokes and Dinesh Devadoss said in a report.
XCSSET, 1st documented by Pattern Micro in 2020, has lots of transferring pieces that enable it to harvest sensitive data from Apple Notes, WeChat, Skype, and Telegram inject malicious JavaScript code into several internet sites and dump cookies from Safari web browser.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

An infection chains entail utilizing a dropper to compromise users’ Xcode initiatives with the backdoor, with the latter also getting actions to evade detection by masquerading as both procedure software package or the Google Chrome web browser application.
The key executable is an AppleScript which is created to retrieve second-stage AppleScript payloads from a network of distant servers that siphon information saved in web browsers these as Google Chrome, Mozilla Firefox, Microsoft Edge, Brave, and Yandex Browser as nicely as chat applications like Telegram and WeChat.
The risk actor is also recognised to use a personalized AppleScript (“listing.applescript”) to identify “how up-to-day the victim is with Apple’s XProtect and MRT malware removal instrument, presumably all the greater to concentrate on them with far more efficient payloads,” the researchers said.
1 of the novel areas of the attack is that deploying the malware inside Xcode projects is observed as a technique of propagation by means of GitHub repositories to further more develop its access.
Besides leveraging AppleScripts, the malware also requires gain of Python scripts for dropping pretend software icons on the macOS Dock and thieving info from the legitimate Notes app.
The latest edition of XCSSET is also notable for incorporating modifications to AppleScripts to account for Apple’s elimination of Python 2.7 from macOS 12.3 produced on March 14, 2022, indicating that the authors are continually updating the malware to enhance their probability of good results.

To that stop, the adversary is mentioned to have current their “safari_remote.applescript” by removing Python 2 in favor of Python 3 for systems managing macOS Monterey 12.3 and higher than.
Despite getting in the wild for two yrs, pretty minimal is acknowledged about the id of the threat actors and their motivations or their exact targets. That reported, XCSSET malware attacks have been noted in China as not too long ago as May 2022 that demanded victims pay out 200 USDT in return for unlocking stolen accounts.
“At this point in time, it truly is unclear irrespective of whether these contaminated repos are victims or crops by menace actors hoping to infect unwary users,” the researchers pointed out. “It has been advised that unsuspecting users may well be pointed to the contaminated repositories via tutorials and screencasts for beginner developers.”
Uncovered this short article interesting? Observe THN on Facebook, Twitter and LinkedIn to browse additional unique material we publish.
Some sections of this report are sourced from:
thehackernews.com

 Firewall Bug Under Active Attack Triggers CISA Warning
Firewall Bug Under Active Attack Triggers CISA Warning