The patch, urgently rushed out on Friday, is an crisis deal with for the commonly deployed platform, whose No. 1 most trafficked web-site is Amazon’s Seller Central.
Discourse – the extremely-well-liked, commonly deployed open-supply group forum and mailing listing management platform – has a critical distant code-execution (RCE) bug that was set in an urgent update on Friday.
Tracked as CVE-2021-41163, the flaw is found in Discourse variations 2.7.8 and previously. It’s rated with a suggestion-best CVSS severity rating of 10 and must be regarded an unexpected emergency repair.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Discourse is extensively made use of and wildly popular, currently being recognised for topping competing discussion board program platforms in conditions of usability. It gives functions that have been popularized by social-media networks, these types of as infinite scrolling, stay updates, drag-and-fall attachments and additional.

In accordance to market place-share and web-usage data, the top rated internet site working with Discourse is sellercentral.amazon.com, which sees a flood of 30 million regular monthly customers. Discourse is also applied to run the local community forum for the well known radio exhibit Car Communicate.

Top internet websites using Discourse. Source: SimilarTech.
Offered Discourse’s widespread use, the Cybersecurity and Infrastructure Company (CISA) on Sunday urged builders to possibly update to patched variations 2.7.9 or afterwards to resolve the bug or to utilize the important workarounds.
The exploit can be induced by an attacker who sends a maliciously crafted ask for that can direct to RCE owing to a absence of validation in subscribe_url values.
Update or Use the Workaround
The issue has been patched in the most current beta, secure and tests-handed variations of Discourse.
For these admins who simply cannot update to 2.7.9 or later on, the workaround is to block requests that get started with “/webhooks/aws path” at an upstream proxy.
The flaw is even now going through technological analysis, but the researcher who uncovered the vulnerability has published a specialized examination about it.
The details in his assessment – which he unveiled just a day immediately after the repair was issued – could be sufficient for attackers to exploit it. The researcher, “joernchen,” told BleepingComputer that he reported the issue to the Discourse staff promptly on finding it on Oct. 10 and that the patch by itself designed it quick to figure out how an exploit would operate.
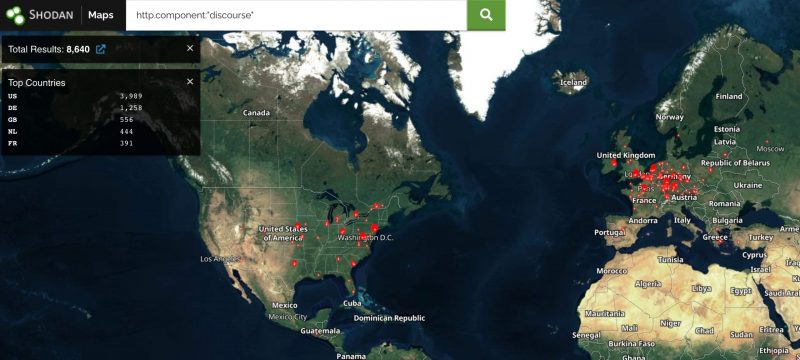
Though the application-as-a-assistance (SaaS) versions of Discourse were fixed as of Wednesday, there might however be a lot of vulnerable deployments. A Shodan research pulled up 8,640 Discourse deployments on Monday early morning.
Just can’t Deal with It If You Really don’t Know About It
Greg Fitzgerald, co-founder of Sevco Security, told Threatpost on Monday that this RCE vulnerability points to how tough it’s finding for corporations to assess their attack surfaces.
“There is much more knowledge flowing all over companies than ever right before,” he stated by means of email. “There are far more remedies set up than ever just before. The variety of equipment, customers and programs being employed by the business enterprise is a lot more intricate than at any time just before.”
It’s for that reason a lot more crucial than at any time to get asset inventory right, he continued. “All these ‘ever befores’ have designed the task of creating an exact IT asset inventory – and consequently knowledge what your serious attack area appears like – unbelievably hard for businesses,” Fitzgerald claimed. “Enterprises are likely to do a really fantastic position of patching the vulnerabilities that they know about speedily, but the true threats lurking underneath the floor for most group are the IT assets they’ve neglected about, which normally make an uncomplicated path to knowledge for attackers.”
Threatpost has achieved out to Discourse for far more specifics and to check with whether or not or not the crew has found any signs that the RCE has been exploited in the wild. We’ll update the story when we listen to back again.
Verify out our no cost upcoming live and on-need on line town halls – one of a kind, dynamic discussions with cybersecurity professionals and the Threatpost neighborhood.
Some parts of this posting are sourced from:
threatpost.com


 Countries Ranked According to Online Risks
Countries Ranked According to Online Risks