The two flaws in Handle Web Panel – a well-liked web hosting administration software program utilized by 200K+ servers – allow code execution as root on Linux servers.
Researchers have learned two critical bugs in Manage Web Panel (CWP) – a well-known web hosting management software made use of by 200K+ servers – that could allow for for remote code execution (RCE) as root on susceptible Linux servers.
CWP, formerly identified as CentOS Web Panel, is an open up-resource Linux regulate panel program utilized for producing and handling web hosting environments. The software package supports the running methods CentOS, Rocky Linux, Alma Linux and Oracle Linux.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The two vulnerabilities – discovered by Octagon Networks’ Paulos Yibelo – are tracked as CVE-2021-45467 (a file inclusion vulnerability) and CVE-2021-45466 (a file publish bug). When chained, the two vulnerabilities can direct to RCE.
Exploitable Without the need of Authentication
The difficulties are found in elements of the CWP panel that are uncovered devoid of authentication in the webroot, in accordance to Octagon’s writeup.
“Turns out, not a ton is exposed,” the scientists wrote, but they observed a couple matters. Precisely, the two certain web pages Octagon focused on are /user/loader.php and /consumer/index.php, which have the pursuing file inclusion defense approach (/user/loader.php):

File inclusion safety method. Source: Octagon Networks.
Which is a technique that defines GETSecurity() as the adhering to:
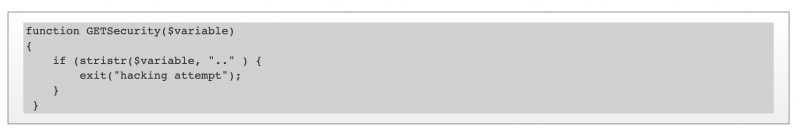
GETSecurity() definition. Source: Octagon Networks.
In get to exploit the vulnerability, inject destructive code from a distant source and execute code execution, an attacker would simply just need to change the contain assertion, which is utilised to insert the written content of just one PHP file into yet another PHP file prior to the server executes it.
To do so necessitates bypassing security protections to stop attackers from reaching the limited API section with out authentication: a feat that can be completed by registering an API important using the file inclusion bug and creating a malicious approved_keys file on the server making use of the file generate flaw.
It is not that CWP lacked protections that flag efforts to swap to a guardian listing. If a parameter script consists of “..” – as in, two dots – the app flags it as a “hacking attempt” and abstains from processing the enter.
But that safety didn’t halt the PHP interpreter from accepting a specially crafted string and correctly obtaining a total bypass – by fooling PHP “into considering there are no consecutive dots (..),” the researchers described.
Operating the fuzzer depicted down below received the Octagon researchers the bypass string /.%00./.

The fuzzer that obtained Octagon the bypass string /.%00./. Supply: Octagon Networks.
How it is finished, researchers explained:
The CVE-2021-45467 file inclusion vulnerability was patched, but Octagon scientists claimed that they continue to observed how “some managed to reverse the patch and exploit some servers.” They shared the adhering to video clip demonstrating the issue:
Octagon will be be releasing a comprehensive evidence of thought for obtaining the preauth RCE “once enough servers migrate to the newest version,” according to the report.
Look at out our free impending reside and on-demand from customers on line city halls – exceptional, dynamic discussions with cybersecurity industry experts and the Threatpost local community.
Some components of this write-up are sourced from:
threatpost.com


 MoleRats APT Launches Spy Campaign on Bankers, Politicians, Journalists
MoleRats APT Launches Spy Campaign on Bankers, Politicians, Journalists