A phishing kit has been located working on at least 700 domains – and mimicking products and services by means of bogus SharePoint, OneDrive and Office environment 365 login portals.
A freshly-uncovered phishing kit, dubbed LogoKit, eliminates headaches for cybercriminals by mechanically pulling victims’ enterprise logos on to the phishing login website page. This gives attackers the equipment wanted to simply mimic corporation login webpages, a job that can at times be intricate.
Cybercriminals have relied on LogoKit to start phishing attacks on a lot more than 700 special domains about the previous 30 days (like 300 in the previous 7 days). These qualified services variety from generic login portals to bogus SharePoint, Adobe Doc Cloud, OneDrive, Business office 365, and cryptocurrency trade login portals.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“With LogoKit’s supposed operation to be centered all around singular e-mail for each URL and extracting company logos, this drastically enhances relieve of carrying out specific attacks versus companies and reusing pretexts with out altering templates,” mentioned Adam Castleman, security researcher with RiskIQ on Wednesday.
Phishing Kits
Phishing kits, which can be obtained by cybercriminals for nearly anything in between $20 and $880, have to have small complex understanding to run over and above modest programming competencies. These kits are used to steal several facts from victims – together with usernames, passwords, credit score card numbers, social security figures and additional.
In order to operate a kit, a cybercriminal should initially install it on a remote server – both by compromising a respectable information management program, or by making use of their personal infrastructure. The moment installed, an attacker just spams victims – by way of email messages, SMS or social media messages – with the URL that will just take them to the phishing kit’s landing page. Some phishing kits contain administrator dashboards exactly where cybercriminals can monitor the quantity of visits to their malicious website and watch the sensitive details disclosed.
Phishing kits are nothing new – on the other hand, LogoKit tends to make the deployment of phishing login internet pages even less complicated for cybercriminals. Lots of moments, cybercriminals that use phishing kits on top of compromised, reputable articles management units offer with sophisticated web page layouts and many documents. This could direct to glitches in the login web site that provide as prospective red flags for victims.
LogoKit skips more than this trouble with its simplicity, said researchers, as it executes only a couple of traces of customizable JavaScript. This makes it possible for undesirable actors to very easily integrate the kit into either existing HTML pretext templates or construct basic login sorts to mimic company login portals.
The package also stands out in that it has the potential to load sources from reliable resources, which include legitimate object storage buckets. This is one more trick that is not necessarily manufacturer new – but that makes pretend login internet pages seem fewer malicious by having customers navigate to a regarded area name.
In some situations, for occasion, attackers have been noticed hosting their phishing internet pages on Google Firebase as aspect of the LogoKit attack. Google Firebase is a mobile and web application advancement system that is backed by Google Cloud Storage and supplies protected file uploads and downloads for Firebase apps.
How It Functions
Though LogoKit has been observed working with these legitimate hosting providers, researchers have also observed compromised web web pages – several running WordPress — to be hosting LogoKit variants. In the two conditions, cybercriminals send victims a specially crafted URL made up of their email deal with. An case in point of a crafted URL that contains the email would be: “phishingpage[.]website/login.html#[email protected].”
“The area hash is then broken down into slices,” in accordance to scientists. “The slice’s delimiter is the ‘@’ symbol, letting the script to extract the user’s/company’s area to fetch the brand and finally redirect a target.”
If target clicks on the URL, LogoKit then fetches the enterprise symbol from a 3rd-party assistance, this sort of as advertising facts motor Clearbit or Google’s databases for favicons (the graphic icons linked with individual webpages).
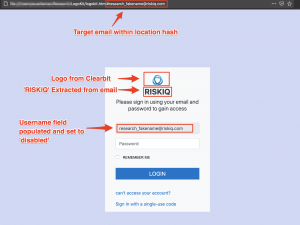
A phishing page running LogoKit. Credit history: RiskIQ
The victim’s email is also automobile-filled into the email or username input discipline of the login graphic. Scientists noted, this trick will make victims think they have previously logged into the web page.
Ought to a target enter their password, LogoKit performs an AJAX request, sending the target’s email and password to an exterior supply.
In some situations, as an added trick, soon after undertaking validation to ensure details is entered and a valid email deal with is current, the package will “fake a person out” by telling them that their password is incorrect and prompting them to enter the password once more. Then, as a closing move, the victim is redirected to their company web-site right after getting into their password.
Many sectors have been qualified by attackers making use of LogoKit, together with economical, authorized, and entertainment, mentioned scientists.
“The LogoKit offers a special opportunity for attackers, letting for easy integration into both current HTML pretext templates or setting up simple login varieties to mimic company login portals,” said Castleman. “Also, with the flexibility of both leveraging compromised infrastructure, attacker-hosted infrastructure, or item storage, attackers can speedily alter their supply source.”
Obtain our exceptional Cost-free Threatpost Insider E book Healthcare Security Woes Balloon in a Covid-Era Entire world , sponsored by ZeroNorth, to find out much more about what these security dangers imply for hospitals at the working day-to-working day stage and how healthcare security groups can put into action very best techniques to shield suppliers and patients. Get the complete tale and Down load the Ebook now – on us!
Some parts of this posting are sourced from:
threatpost.com


 McAfee’s MVISION XDR takes security beyond the endpoint
McAfee’s MVISION XDR takes security beyond the endpoint