Shutterstock
Cyber security scientists have uncovered a new underground organization design dubbed ‘access-as-a-service’ in which obtain to an organisation’s network is bought rather than an exploit or zero-working day vulnerability.
So-called access brokers are advertising immediate obtain to a firm’s network in which they’re already embedded through shared remote VPN connections. Attackers can pay out different sums for different levels of obtain.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The enterprise model, learned and comprehensive by Development Micro, could direct to a new way for ransomware operators to launch attacks without the need of possessing operating exploit by themselves.
Attackers are now in a position to purchase their way into a network, spending only as significantly as they have to have for the right level of access to attain their aim.
The organization product depends on stolen qualifications for obtain brokers to have a feasible provider and Development Micro claimed firms will have to place a greater emphasis on protecting credential theft to prevent foreseeable future breaches.
“Entry brokers in the criminal underground frequently advertise this service like it is a cinema ticket: Someone buys this ticket, and they get straight in,” examine the report. “In truth, on the other hand, items are a bit unique.
“For case in point, what particularly do buyers get in exchange for their revenue? From time to time, it’s access to a web shell or a equivalent straightforward process of having a command prompt into the compromised network. Extra generally than not, on the other hand, it is just a set of qualifications and a VPN server to join to.”
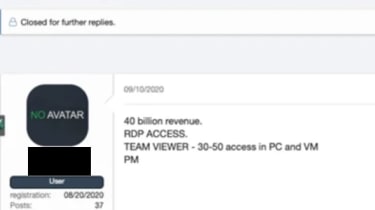
Remote Desktop Protocol (RDP) obtain and VPN-primarily based accessibility ended up the two most frequent products and solutions staying marketed, generally in the United States, Spain, Germany, France, and the UK.
Following viewing extra than a thousand adverts for providers on-line, the most typical targets Development Micro noticed ended up universities and educational facilities (36%), 11% made available entry to production corporations and professional services, with other miscellaneous providers comprising the remainder.
Pattern Micro
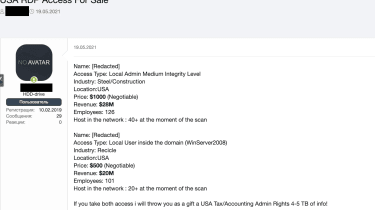
On line adverts ordinarily supply accessibility to a company with a broad description such as ‘big German vitality company’, offer you specifics of the amount of accessibility out there, variety of entry on provide (RDP or VPN), cost of the services, and in some cases specifics of the company’s turnover and personnel quantities.
Development Micro
Price ranges for expert services can variety among a number of US pounds for accessibility to a single equipment and 6-digit sums for admin credentials to an overall business, but most dedicated brokers will not publicize their costs brazenly, according to the researchers.
Entry brokers are commonly marketing their merchandise both on deep web felony marketplaces, as a result of a network of connections through underground community forums, and in considerably less common conditions committed on the web stores are made use of for scaled-down-scale, single-machine access.
Trend Micro manufactured several strategies for businesses wary of becoming exploited applying this new company product. Checking general public breaches can be handy in figuring out if credentials may well have been stolen and triggering a password reset for all employees if one is detected.
Enabling two-factor authentication (2FA) for distant employees will also assist stop distant obtain from criminals, as will intently checking user behaviour on the network.
For the most cautious, working on a zero-trust model and assuming all staff members have lost their passwords to criminals in advance of is recommended, applying the required security measures where by correct.
Some parts of this report are sourced from:
www.itpro.co.uk


 UK and Singapore align closer on digital trade
UK and Singapore align closer on digital trade