A previously undocumented original accessibility broker has been unmasked as furnishing entry points to 3 different risk actors for mounting intrusions that assortment from monetarily enthusiastic ransomware attacks to phishing campaigns.
BlackBerry’s exploration and intelligence workforce dubbed the entity “Zebra2104,” with the group dependable for featuring a signifies of a digital solution to ransomware syndicates this kind of as MountLocker and Phobos, as perfectly as the advanced persistent menace (APT) tracked less than the moniker StrongPity (aka Promethium).
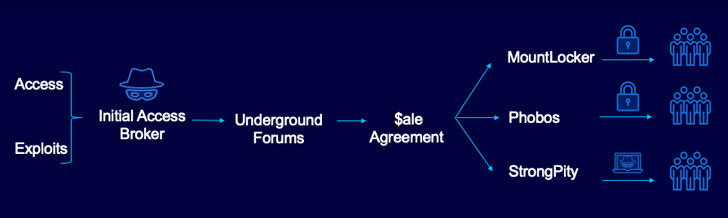
The risk landscape as we know it has been more and more dominated by a group of gamers known as the preliminary access brokers (IABs), who are recognised to supply other cyber-criminal groups, like ransomware affiliates, with a foothold to an infinite pool of prospective corporations belonging to varied geographies and sectors by means of persistent backdoors into the victim networks, proficiently constructing a pricing model for distant entry.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“IABs normally initial attain entry into a victim’s network, then provide that accessibility to the best bidder on underground message boards positioned in the dark web,” BlackBerry researchers noted in a specialized report printed final 7 days. “Later, the profitable bidder will usually deploy ransomware and/or other monetarily inspired malware inside the victim’s group, relying on the aims of their campaign.”
An August 2021 analysis of extra than 1,000 obtain listings marketed for sale by IABs in underground boards on the dark web identified that the average value of network accessibility was $5,400 for the interval July 2020 to June 2021, with the most valuable delivers like domain admin privileges to organization programs.
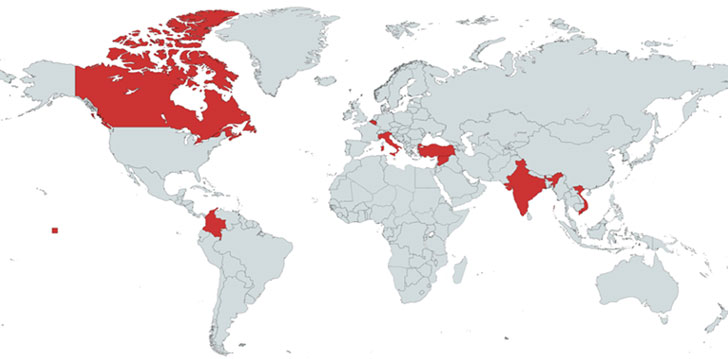
The Canadian cybersecurity company’s investigation commenced with a domain named “trashborting[.]com” that was uncovered delivering Cobalt Strike Beacons, utilizing it to backlink the broader infrastructure to a amount of malspam campaigns that resulted in the delivery of ransomware payloads, some of which focused Australian real estate providers and condition federal government departments in September 2020.

On leading of that, “supercombinating[.]com,” a different sister area registered along with trashborting[.]com, was discovered connected to destructive MountLocker and Phobos activity, even as the area fixed to an IP address “91.92.109[.]174,” which, in switch, was also applied to host a third domain “mentiononecommon[.]com” in between April and November 2020 and put to use as a command-and-control server in a June 2020 campaign linked with StrongPity.
The IAB’s overlaps and wide targeting has also led the researchers to imagine that the operator “both has a great deal of manpower or they have set up some substantial ‘hidden in simple sight’ traps throughout the internet,” enabling MountLocker, Phobos and StrongPity to supply their obtain to qualified networks.
“The interlinking web of destructive infrastructure noticed through this research has proven that, in a manner that mirrors the genuine organization planet, cybercrime groups are in some cases operate not unlike multinational businesses,” the researchers mentioned. “They build partnerships and alliances to assist advance their aims. If anything at all, it is risk-free to assume that these danger group ‘business partnerships’ are heading to turn into even a lot more commonplace in future.”
Located this write-up fascinating? Stick to THN on Fb, Twitter and LinkedIn to read through a lot more exceptional written content we article.
Some parts of this post are sourced from:
thehackernews.com

 Types of Penetration Testing
Types of Penetration Testing