If you are pondering about accomplishing a penetration check on your organization, you could be interested in mastering about the different forms of checks offered. With that awareness, you may be much better outfitted to outline the scope for your venture, employ the correct skilled and, in the end, realize your security goals.
What is penetration testing?
Penetration tests, frequently referred to as “pen tests,” is a system that simulates true-life attacks on your IT programs to uncover weaknesses that could be exploited by hackers. Regardless of whether to comply with security polices this kind of as ISO 27001, gain customer and 3rd party believe in, or attain your personal peace of head, penetration tests is an successful approach utilised by contemporary companies to strengthen their cyber security posture and prevent details breaches.
Study about the distinctive kinds of penetration tests to obtain out which variety you can advantage from the most:

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Network penetration screening
As the name implies, a network penetration examination aims to determine weaknesses in your network infrastructure, be that on the premises or in cloud environments. It is a single of the most prevalent and crucial assessments to execute to make certain the security of your small business-critical knowledge.
Network penetration tests covers a broad assortment of checks, including insecure configurations, encryption vulnerabilities, and lacking security patches in buy to ascertain the techniques a hacker could just take to attack your organization. Security experts normally categorize this examination into two unique perspectives: external and inside.
External penetration tests requires searching for vulnerabilities that could be exploited by any attacker with obtain to the internet. In this state of affairs, penetration testers are striving to get entry to your business-critical systems and details in order to ascertain how an attacker without the need of any prior entry or understanding would be in a position to goal your business. You can believe of this exam as being carried out from the perspective of an “outsider”.
In contrast, interior penetration testing is concerned with testing your inner corporate ecosystem. This kind of testing considers situations in which an attacker has managed to get an original foothold in your company network, for instance by exploiting a vulnerability in a single of your internet-struggling with techniques, or by way of the use of social engineering. In this situation, the test is done from an “insider” viewpoint, with an objective of locating a way to steal delicate information or disrupting the operations of an business.
Commonly talking, exterior weaknesses are considered to pose a extra really serious danger than inner. For a single point, a hacker has to prevail over an exterior security barrier prior to accessing your inside networks and pivoting to other programs. If you haven’t executed any sort of penetration tests right before, an exterior or “perimeter” examination is generally the ideal area to start, as the perimeter is the best factor for attackers to get to. If you have trivial vulnerabilities in your internet-facing infrastructure, which is wherever the hackers will get started.
Web application penetration tests
Web application penetration screening tries to uncover vulnerabilities across websites and web apps, such as e-commerce platforms, written content administration techniques, and shopper marriage administration program. This kind of test bargains with reviewing the overall web application’s security, which includes its underlying logic and customized functionalities, to stop data breaches.
Some of the common vulnerabilities detected during a web app penetration take a look at contain database injections, cross-web site scripting (XSS), and broken authentication. If you are interested in learning more about distinct kinds of web software weaknesses, their severity and how you can avert them, the Open Web Software Security Challenge (OWASP) Best 10 is a great area to start off. Each few many years OWASP publishes data about the most regular and harmful web software flaws, basing its results on the info collected from many thousands of applications.
Looking at the prevalence of web apps in modern day companies, and the valuable info that they transmit and retail store, it is unsurprising that they are an beautiful target to cybercriminals. In accordance to Verizon’s “2021 Facts Breach Investigations Report”, the proportion of incidents, which included web application assets, reached almost 50%. For this explanation, organizations that are building or managing their individual internet-experiencing programs really should strongly take into consideration conducting web application penetration screening.
Automated penetration testing
Understandably, as penetration assessments can be highly-priced and infrequent (only run once or 2 times for every year), quite a few folks normally wonder if automated penetration screening is possible.
Although it really is not possible to absolutely automate a penetration check (as there will usually be an component of handbook function done by expert professionals), it truly is likewise unachievable for individuals to manually look at for every single vulnerability that exists, there are basically also many. Which is exactly where vulnerability scanning will come in, with these equipment you can: plan scans get swiftly examined for several hundreds of weaknesses and be notified of your benefits in a selection of channels and formats. It is no surprise that vulnerability scanners sort a critical portion of a penetration testers toolkit.
1 this kind of device that you can check out is Intruder. It gives automated security scanning that is designed to be simple and quickly, so you can get set-up and guarded in very little to no time. Intruder involves Rising Threat Scans, which proactively check out your methods for freshly learned vulnerabilities as before long as they are disclosed.
It may well not be a entirely automated penetration examination, but it undoubtedly is like obtaining an automated penetration tester observing over your systems. When you combine continuous vulnerability scanning with an annual penetration test, you can rest assured that your devices are protected by a robust and in depth cyber security software.
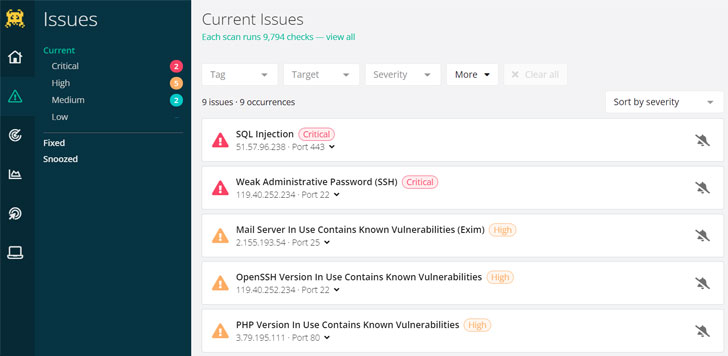 Intruder mechanically separates purely informational benefits from actionable issues, substantially saving specialized teams time on analyzing their scan effects.
Intruder mechanically separates purely informational benefits from actionable issues, substantially saving specialized teams time on analyzing their scan effects.
If you’d like to see the automated software in motion, you can just take Intruder’s Pro Plan for a spin with the 30-day totally free demo.
Social engineering
In comparison to earlier described penetration tests kinds, which target on acquiring weaknesses in technology, social engineering makes an attempt to compromise the security of an organization by exploiting human psychology. It can consider a selection of kinds and could be executed the two remotely, for instance by making an attempt to get sensitive information and facts from customers by way of phishing email messages or phone calls, or on-web site, in which circumstance a penetration tester will endeavor to gain obtain to a physical facility. In all cases, an objective of this penetration test is to manipulate individuals, generally the firm’s personnel, to give absent valuable details.
The accomplishment of a social engineering penetration check largely depends on the facts collected in the “reconnaissance” period, which will involve researching targeted individuals or an business by working with publicly available open-supply intelligence (OSINT). After making a much more exact picture of their concentrate on, a penetration tester can use uncovered info to carry on with the development of a personalized attack system.
A person of the most typical attack vectors in social engineering is a phishing attack, typically shipped by email. When carrying out a phishing attack, a penetration tester does not essentially prevent when an unsuspecting worker clicks on a malicious backlink, but can go further, making an attempt to steal person qualifications and get accessibility to an employee’s laptop. Such attacks can be really thriving, in particular when executed by experienced penetration testers.
Social engineering penetration testing is not as broadly adopted as network or web application testing. Having said that, if your firm is previously carrying out frequent security consciousness coaching, conducting a committed social engineering take a look at can be a terrific addition to your arsenal for identifying and repairing security issues in your operations.
Pink teaming
This state-of-the-art procedure has its origin in armed service schooling workout routines. It is intended to challenge an organization’s security, procedures, policies and plans by adopting an adversarial mindset. In distinction, Blue teaming, if not identified as “defensive security,” entails detecting and withstanding Purple team attacks as well as authentic-lifetime adversaries.
Pink Teaming combines digital, social and physical domains to employ detailed true-daily life attack eventualities. As this sort of, Crimson Teaming can be regarded as a distinct operation from penetration testing, but considering that its responsibilities span all of the penetration screening kinds described above, we thought it was truly worth mentioning it in this posting.
An objective of a normal penetration check is to obtain as numerous vulnerabilities as probable inside of a offered timeframe. The breath of this examination is in a natural way limited by the scope of function but genuine-daily life adversaries really don’t have these synthetic limitations to observe. As a final result, even if an business frequently performs penetration tests and vulnerability scans, it can nonetheless be exposed to extra refined attacks these types of as the place social engineering and inside network weaknesses are chained together. This is the place Crimson Teaming comes in. It assesses an organization’s setting as a complete, knowledge how all components functionality with each other. It then applies critical contemplating to find new vulnerabilities that attackers can exploit, encouraging the business to assess its response to authentic-entire world attacks.
Compared to the typical penetration check, which lasts several times or weeks, Pink Workforce assessments generally just take considerably longer, in some cases several months to finish. Owing to its sophisticated character, it is a instead rare procedure, commonly carried out by much larger corporations or by governing administration contractors with effectively-proven security programmes.
To conclude
Penetration screening is a broad discipline that encompasses various tactics, so it is crucial to fully grasp the relative pitfalls that your corporation is facing in get to opt for the most acceptable variety. If you are nevertheless doubtful what kind of screening is appropriate for your organization, you can get to out to Intruder’s crew of knowledgeable penetration testers, who will be ready to aid you.
About Intruder
Intruder is an intercontinental cyber security corporation that aids organizations lower their cyber publicity by offering an easy vulnerability scanning solution. Providing industry-foremost security checks, ongoing monitoring, and an simple-to-use system, Intruder keeps enterprises of all dimensions harmless from hackers.
Visit their web page to come across out extra about Intruder and to consider their on the web vulnerability scanner for free.
Identified this short article appealing? Adhere to THN on Facebook, Twitter and LinkedIn to browse far more unique content we write-up.
Some areas of this posting are sourced from:
thehackernews.com


 Critical Flaws in Philips TASY EMR Could Expose Patient Data
Critical Flaws in Philips TASY EMR Could Expose Patient Data