A danger actor with likely inbound links to an Indian cybersecurity organization has been very little if remarkably persistent in its attacks in opposition to military services organizations based mostly in South Asia, including Bangladesh, Nepal, and Sri Lanka, since at minimum September 2020 by deploying distinctive variants of its bespoke malware framework.
Slovak cybersecurity agency ESET attributed the really qualified attack to a hacking team known as Donot Group. “Donot Group has been persistently focusing on the exact same entities with waves of spear-phishing email messages with malicious attachments every single two to four months,” scientists Facundo Muñoz and Matías Porolli reported.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Functioning considering that at the very least 2016, Donot Workforce (also known as APT-C-35 and SectorE02) has been linked to a string of intrusions mostly targeting embassies, governments, and armed forces entities in Bangladesh, Sri Lanka, Pakistan, and Nepal with Windows and Android malware.
In Oct 2021, Amnesty International unearthed proof tying the group’s attack infrastructure to an Indian cybersecurity company named Innefu Labs, elevating suspicions that the risk actor could be advertising the adware or giving a hackers-for-hire assistance to governments of the area.
Although it’s not uncommon for APT groups to re-attack a formerly compromised network by deploying stealthier backdoors to protect up their tracks, Donot Group attempts a distinctive tack in that it deploys numerous variants of the malware already in its arsenal.
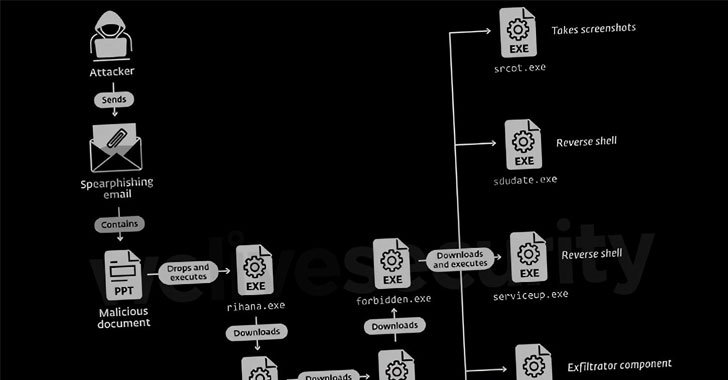
Sent through weaponized Microsoft Workplace files, the so-identified as yty malware framework is a chain of intermediary downloaders that culminates in the execution of a backdoor, which requires treatment of retrieving supplemental factors capable of harvesting data files, recording keystrokes and screenshots, and deploying reverse shells for remote accessibility.
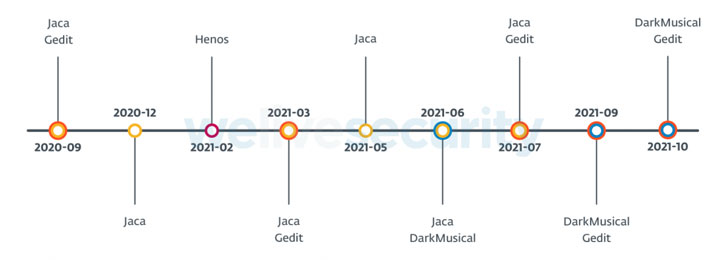
ESET dubbed the new variants of yty, DarkMusical and Gedit, with telemetry details pointing to attacks from a third variant referred to as Jaca from March to July 2021. The to start with wave of attacks applying DarkMusical is explained to have transpired in June 2021, although Gedit-connected strategies had been noticed as early as September 2020, only to decide up the tempo a calendar year afterwards.
What is extra, the fourth set of attacks that happened between February and March 2021 concentrating on armed service companies in Bangladesh and Sri Lanka leveraged a modified edition of Gedit codenamed Henos.
“Donot Team helps make up for its lower sophistication with tenacity,” the scientists concluded. “We expect that it will proceed to thrust on irrespective of its lots of setbacks. Only time will convey to if the group evolves its current TTPs and malware.”
Found this write-up fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to browse more distinctive content material we put up.
Some sections of this write-up are sourced from:
thehackernews.com


 A Trip to the Dark Site — Leak Sites Analyzed
A Trip to the Dark Site — Leak Sites Analyzed